Part B. Baseband Specification
vAtlanta r00
This Part describes the specification of the Bluetooth Link Controller which carries out the Baseband protocols and other low-level link routines.
1. General description
This part specifies the normal operation of a Bluetooth Baseband.
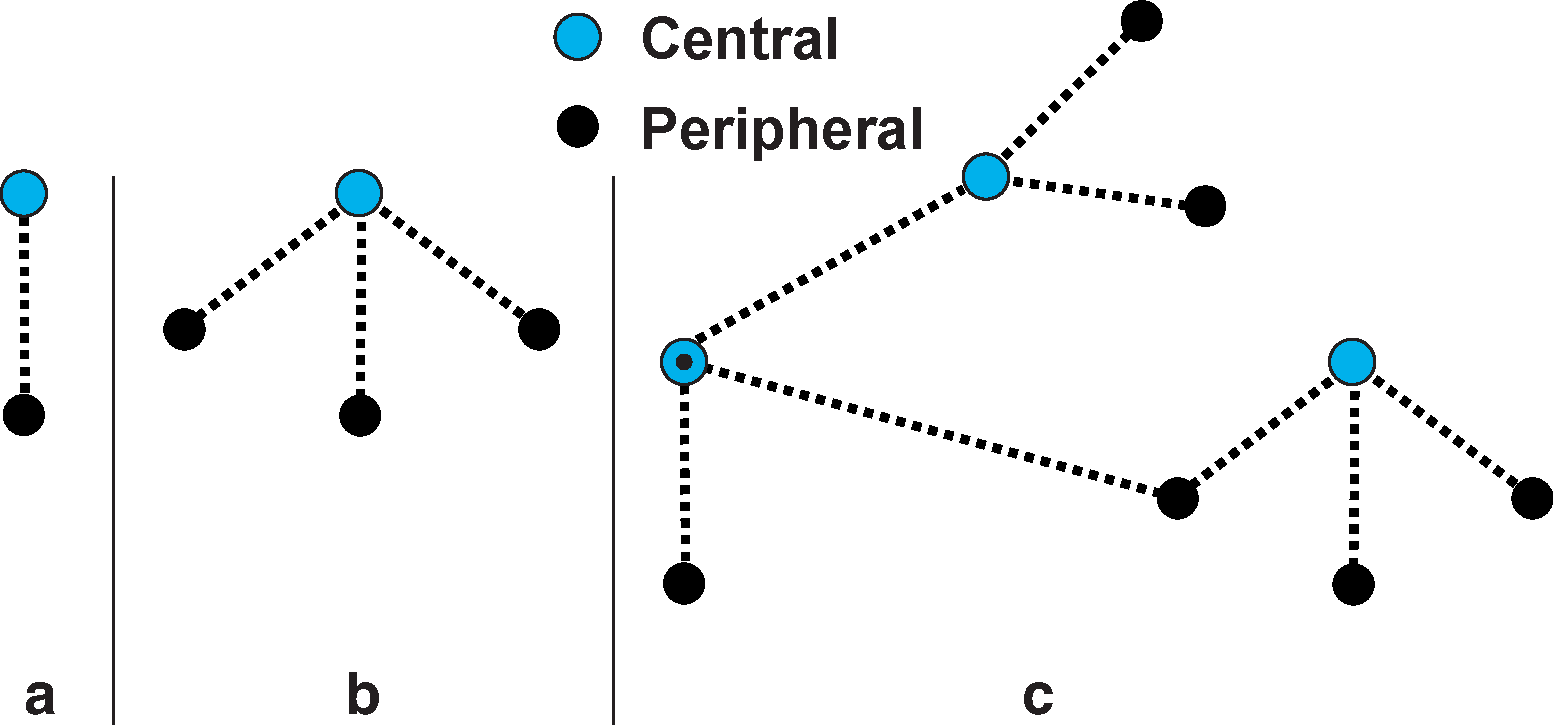
The Bluetooth system provides a point-to-point connection or a point-to-multipoint connection, see (a) and (b) in Figure 1.1. In a point-to-point connection the physical channel is shared between two Bluetooth devices. In a point-to-multipoint connection, the physical channel is shared among several Bluetooth devices. Two or more devices sharing the same physical channel form a piconet. One Bluetooth device acts as the Central of the piconet, whereas the other device(s) act as Peripheral(s). Up to seven Peripherals can be active in the piconet. The channel access is controlled by the Central. An unlimited number of Peripherals can receive data on the physical channel carrying the Connectionless Peripheral Broadcast physical link.
Piconets that have common devices are called a scatternet, see (c) in Figure 1.1. Each piconet only has a single Central, however, Peripherals can participate in different piconets on a time-division multiplex basis. In addition, a Central in one piconet can be a Peripheral in other piconets. Piconets shall not be frequency synchronized and each piconet has its own hopping sequence.
Data is transmitted over the air in packets. Two modes are defined: a mandatory mode called Basic Rate and an optional mode called Enhanced Data Rate. The symbol rate for all modulation modes is 1 Msym/s. The gross air data rate is 1 Mb/s for Basic Rate. Enhanced Data Rate has a primary modulation mode that provides a gross air data rate of 2 Mb/s, and a secondary modulation mode that provides a gross air data rate of 3 Mb/s.
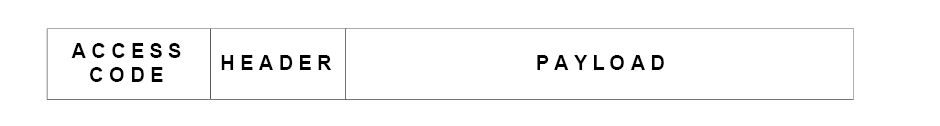
The general Basic Rate packet format is shown in Figure 1.2. Each packet consists of 3 entities: the access code, the header, and the payload.
The general Enhanced Data Rate packet format is shown in Figure 1.3. Each packet consists of 6 entities: the access code, the header, the guard period, the synchronization sequence, the Enhanced Data Rate payload and the trailer. The access code and header use the same modulation mode as for Basic Rate packets while the synchronization sequence, the Enhanced Data Rate payload and the trailer use the Enhanced Data Rate modulation mode. The guard time allows for the transition between the modulation modes.

1.1. Bluetooth clock
Every Bluetooth device shall have a native clock that shall be derived from a free running reference clock. Offsets may be added to the reference clock to synchronize the native clock with other non-Bluetooth systems. For synchronization with other Bluetooth devices, offsets are used that, when added to the native clock, provide temporary Bluetooth clocks that are mutually synchronized. It should be noted that the Bluetooth clock has no relation to the time of day; it may therefore be initialized to any value. The clock has a cycle of about a day. If the clock is implemented with a counter, a 28-bit counter is required that shall wrap around at 228 -1. The least significant bit (LSB) shall tick in units of 312.5 μs (i.e. half a time slot), giving a clock rate of 3.2 kHz.
The clock determines critical periods and triggers the events in the device. Four periods are important in the Bluetooth system: 312.5 μs, 625 μs, 1.25 ms, and 1.28 s; these periods correspond to the timer bits CLK0, CLK1, CLK2, and CLK12, respectively, see Figure 1.4.

In the different modes and states a device can reside in, the clock has different appearances:
CLKR reference clock
CLKN native clock
CLKE estimated clock
CLK Central's clock
CLKR is the reference clock driven by the free running system clock. CLKN may be offset from the reference clock by a timing offset. In Standby state and in Hold, Sniff, and Connectionless Peripheral Broadcast modes the reference clock shall have a worst case accuracy of ±250 ppm. In all other circumstances, it shall have a worst case accuracy of ±20 ppm; this accuracy shall also be used by the piconet Central while performing Piconet Clock Adjustment (see Section 8.6.10).
See Section 2.2.4 for the definition of CLK and Section 2.4.1 for the definition of CLKE.
The Central may adjust its native clock during the existence of the piconet within certain limits (see Section 8.6.10.3). The Central may also perform a coarse adjustment of the native clock by using the LMP_CLK_ADJ sequence.
1.2. Bluetooth Device addressing
Each Bluetooth device shall be allocated a unique 48-bit Bluetooth Device Address (BD_ADDR). The address shall be a 48-bit extended unique identifier (EUI-48) created in accordance with section 8.2 ("Universal addresses") of the IEEE 802-2014 standard (http://standards.ieee.org/findstds/standard/802-2014.html).
Creation of a valid EUI-48 requires one of the following MAC Address Block types to be obtained from the IEEE Registration Authority:
MAC Address Block Large (MA-L)
MAC Address Block Medium (MA-M)
MAC Address Block Small (MA-S)
See http://standards.ieee.org/develop/regauth/index.html for information on obtaining one of these MAC Address Blocks. See also the IEEE’s guidelines for use of these addresses (https://standards.ieee.org/develop/regauth/tut/eui.pdf).
Figure 1.5 illustrates how the LAP, UAP, and NAP map to the EUI-48. The bit pattern in Figure 1.5 is an example BD_ADDR.
 |
The BD_ADDR may take any values except those that would have any of the 64 reserved LAP values for general and dedicated inquiries (see Section 1.2.1).
1.2.1. Reserved addresses
A block of 64 contiguous LAPs is reserved for inquiry operations; one LAP common to all devices is reserved for general inquiry, the remaining 63 LAPs are reserved for dedicated inquiry of specific classes of devices (see Assigned Numbers). The same LAP values are used regardless of the contents of UAP and NAP. Consequently, none of these LAPs can be part of a user BD_ADDR.
The reserved LAP addresses are 0x9E8B00 to 0x9E8B3F. The general inquiry LAP is 0x9E8B33. All addresses have the LSB at the rightmost position, hexadecimal notation. The default check initialization (DCI) is used as the UAP whenever one of the reserved LAP addresses is used. The DCI is defined to be 0x00 (hexadecimal).
1.3. Access codes
In the Bluetooth system all transmissions over the physical channel begin with an access code. Three different access codes are defined, see also Section 6.3.1:
device access code (DAC)
channel access code (CAC)
inquiry access code (IAC)
All access codes are derived from the LAP of a device address or an inquiry address. The device access code is used during Page, Page Scan, Central Page Response, and Peripheral Page Response substates and shall be derived from the paged device’s BD_ADDR. The channel access code is used in the Connection state, Synchronization Train substate, and Synchronization Scan substate, and forms the beginning of all packets exchanged on the piconet physical channel. The channel access code shall be derived from the LAP of the Central’s BD_ADDR. Finally, the inquiry access code shall be used in the Inquiry substate. There is one general IAC (GIAC) for general inquiry operations and there are 63 dedicated IACs (DIACs) for dedicated inquiry operations.
The access code also indicates to the receiver the arrival of a packet. It is used for timing synchronization and offset compensation. The receiver correlates against the entire synchronization word in the access code, providing very robust signaling.
2. Physical channels
The lowest architectural layer in the Bluetooth system is the physical channel. A number of types of physical channels are defined. All Bluetooth physical channels are characterized by the combination of a basic pseudo-random frequency hopping sequence (which, for physical links on the adapted piconet physical channel, is then modified by the AFH_channel_map (defined in [Vol 2] Part C, Section 5.2) for that link), the specific slot timing of the transmissions, the access code and packet header encoding. These aspects, together with the range of the transmitters, define the signature of the physical channel. For the basic and adapted piconet physical channels frequency hopping is used to change frequency periodically to reduce the effects of interference and to satisfy local regulatory requirements.
Two devices that wish to communicate use a shared physical channel for this communication. To achieve this, their transceivers must be tuned to the same RF frequency at the same time, and they must be within a nominal range of each other.
Given that the number of RF carriers is limited and that many Bluetooth devices could be operating independently within the same spatial and temporal area there is a strong likelihood of two independent Bluetooth devices having their transceivers tuned to the same RF carrier, resulting in a physical channel collision. To mitigate the unwanted effects of this collision each transmission on a physical channel starts with an access code that is used as a correlation code by devices tuned to the physical channel. This channel access code is a property of the physical channel. The access code is always present at the start of every transmitted packet.
Several Bluetooth physical channels are defined. Each is optimized and used for a different purpose. Two of these physical channels (the basic piconet channel and adapted piconet channel) are used for communication between connected devices and are associated with a specific piconet. Other physical channels are used for discovering (the inquiry scan channel) and connecting (the page scan channel) Bluetooth devices. The synchronization scan physical channel is used by devices to obtain timing and frequency information about the Connectionless Peripheral Broadcast physical link or to recover the current piconet clock.
A Bluetooth device can only use one of these physical channels at any given time. In order to support multiple concurrent operations the device uses time-division multiplexing between the channels. In this way a Bluetooth device can appear to operate simultaneously in several piconets, as well as being discoverable and connectable.
Whenever a Bluetooth device is synchronized to the timing, frequency and access code of a physical channel it is said to be 'connected' to this channel (whether or not it is actively involved in communications over the channel.) At a minimum, a device need only be capable of connection to one physical channel at a time, however, advanced devices may be capable of connecting simultaneously to more than one physical channel, but the specification does not assume that this is possible.
2.1. Physical channel definition
Physical channels, apart from the synchronization scan physical channel (which uses a set of fixed RF channels), are defined by a basic pseudo-random RF channel hopping sequence, the packet (slot) timing, and an access code. The hopping sequences are determined by the UAP and LAP of a Bluetooth Device Address, the selected basic hopping sequence, and – for the adapted piconet physical channel – the AFH_channel_map being used on a physical link. The phase in the hopping sequence is determined by the Bluetooth clock. All physical channels are subdivided into time slots. Within the physical channel, each reception or transmission event is associated with a time slot or time slots. For each reception or transmission event an RF channel is selected by the hop selection kernel (see Section 2.6).The maximum hop rate is 1600 hops per second in the Connection state, the Synchronization Train substate, and the Synchronization Scan substate and the maximum is 3200 hops per second in the Inquiry and Page substates.
The following physical channels are defined:
basic piconet physical channel
adapted piconet physical channel
page scan physical channel
inquiry scan physical channel
synchronization scan physical channel
2.2. Basic piconet physical channel
During the Connection state the basic piconet physical channel is used by default. The adapted piconet physical channel may also be used. The adapted piconet physical channel is identical to the basic piconet physical channel except for the differences listed in Section 2.3.
2.2.1. Central and Peripheral roles
The basic piconet physical channel is defined by the Central of the piconet. The Central controls the traffic on the piconet physical channel by a polling scheme (see Section 8.5).
By definition, the device that initiates a connection by paging is the Central. Once a piconet has been established, the Central and Peripheral may exchange roles. This is described in Section 8.6.5.
2.2.2. Hopping characteristics
The basic piconet physical channel is characterized by a pseudo-random hopping through all 79 RF channels. The frequency hopping in the piconet physical channel is determined by the Bluetooth clock and BD_ADDR of the Central. When the piconet is established, the Central's clock is communicated to the Peripherals. Each Peripheral shall add an offset to its native clock to synchronize with the Central's clock. Since the clocks are independent, the offsets must be updated regularly. All devices participating in the piconet are time-synchronized and hop-synchronized to the channel.
The basic piconet physical channel uses the basic channel hopping sequence and is described in Section 2.6.
2.2.3. Time slots
The basic piconet physical channel is divided into time slots, each 625 μs in length. The time slots are numbered according to the most significant 27 bits of the Bluetooth clock CLK27-1 of the piconet Central. The slot numbering ranges from 0 to 227-1 and is cyclic with a cycle length of 227. The time slot number is denoted as k.
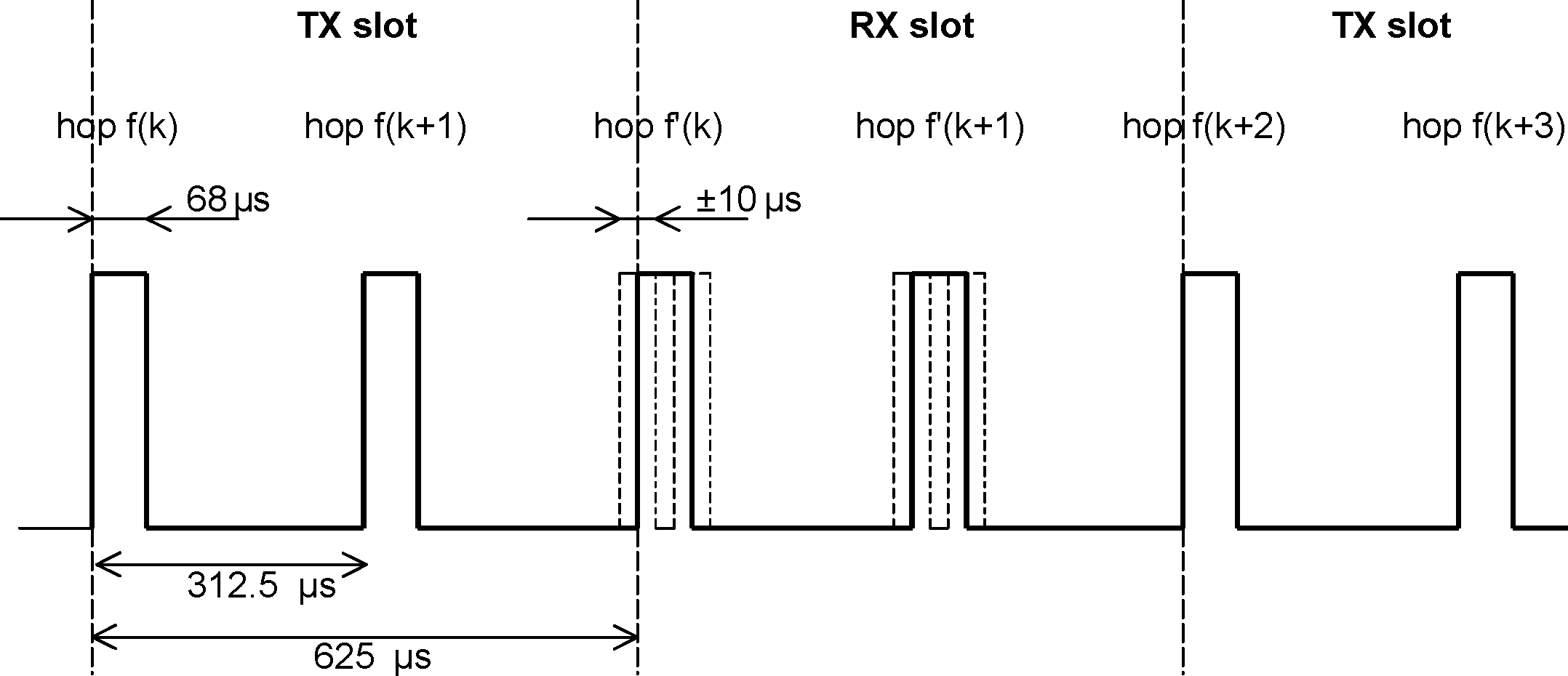
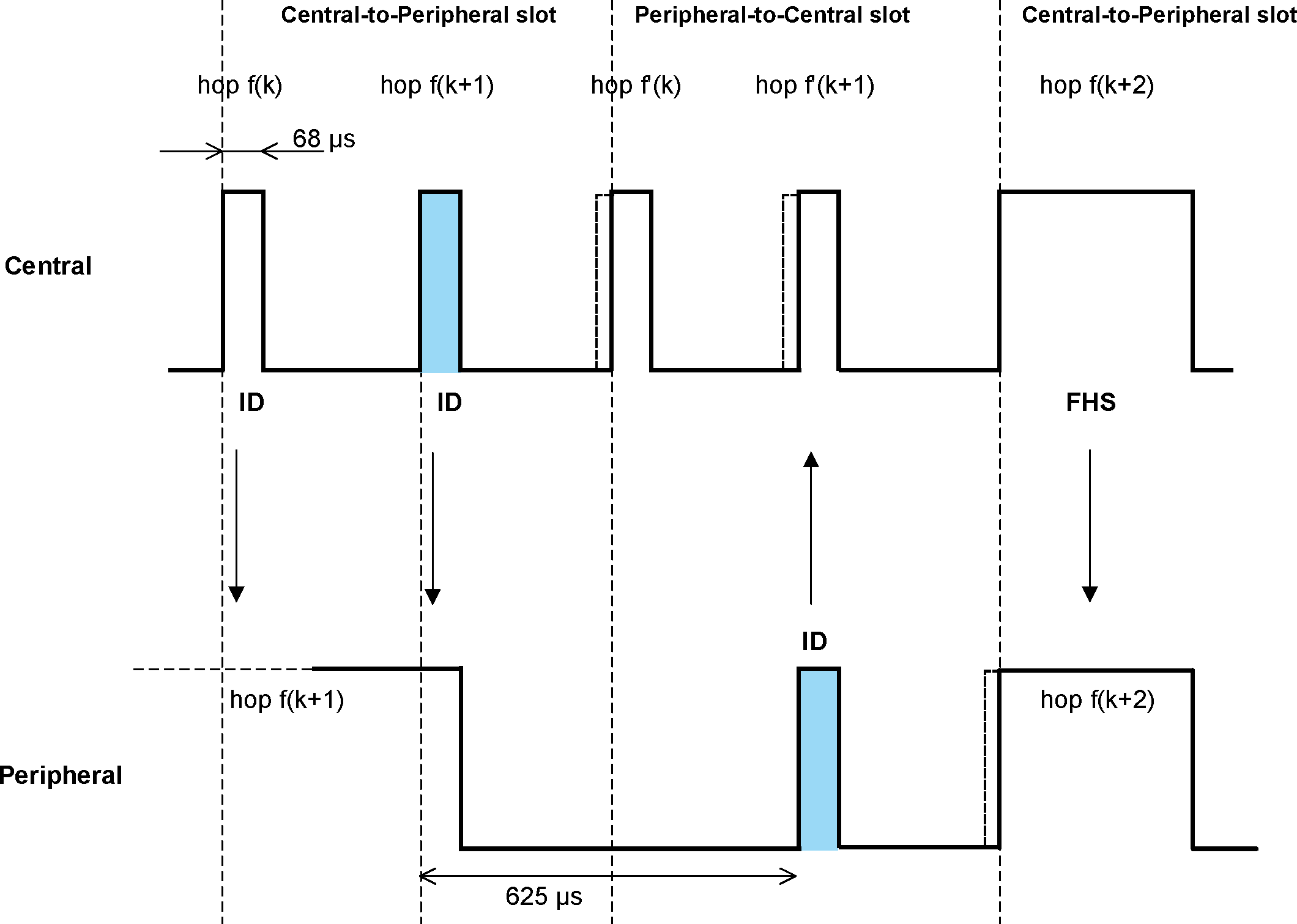
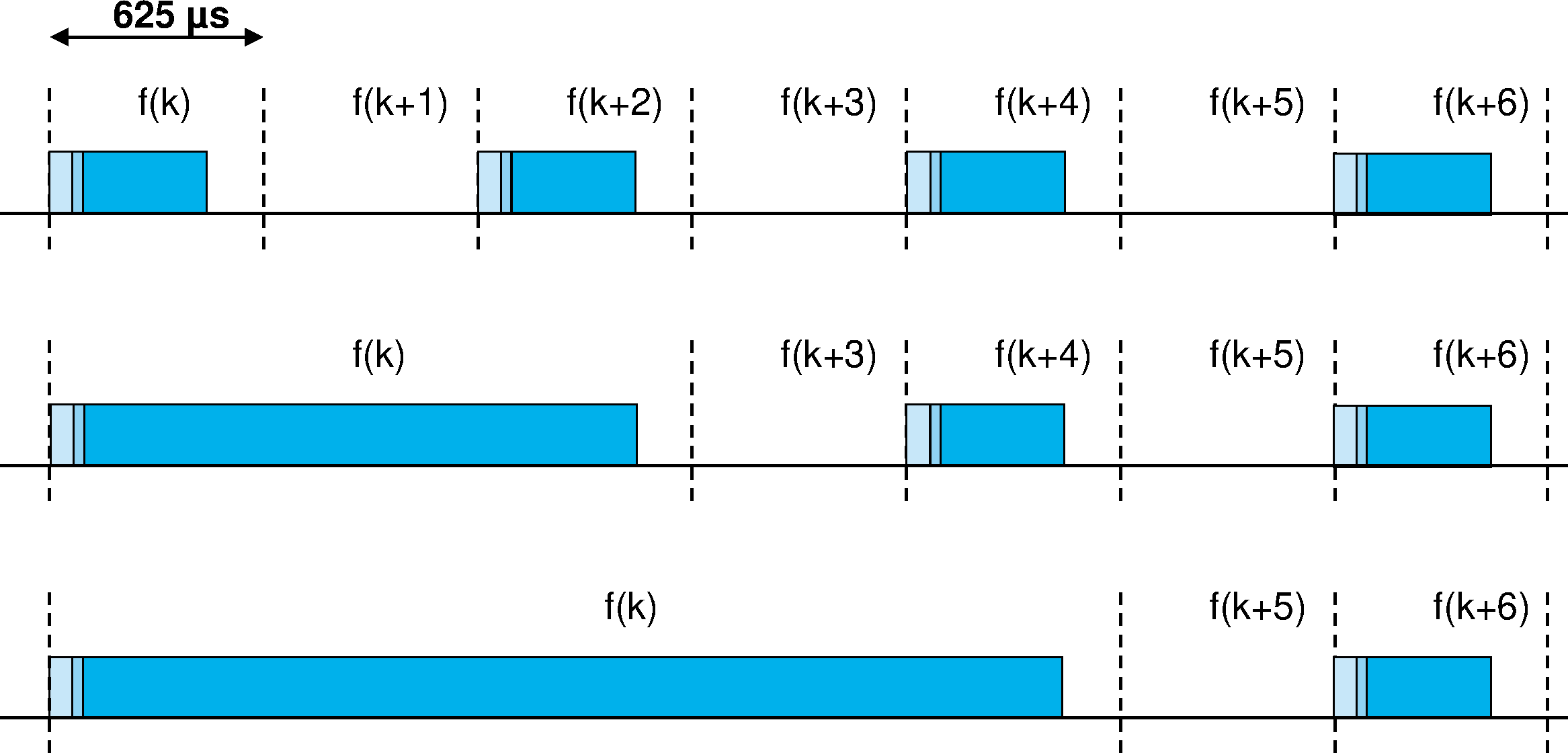
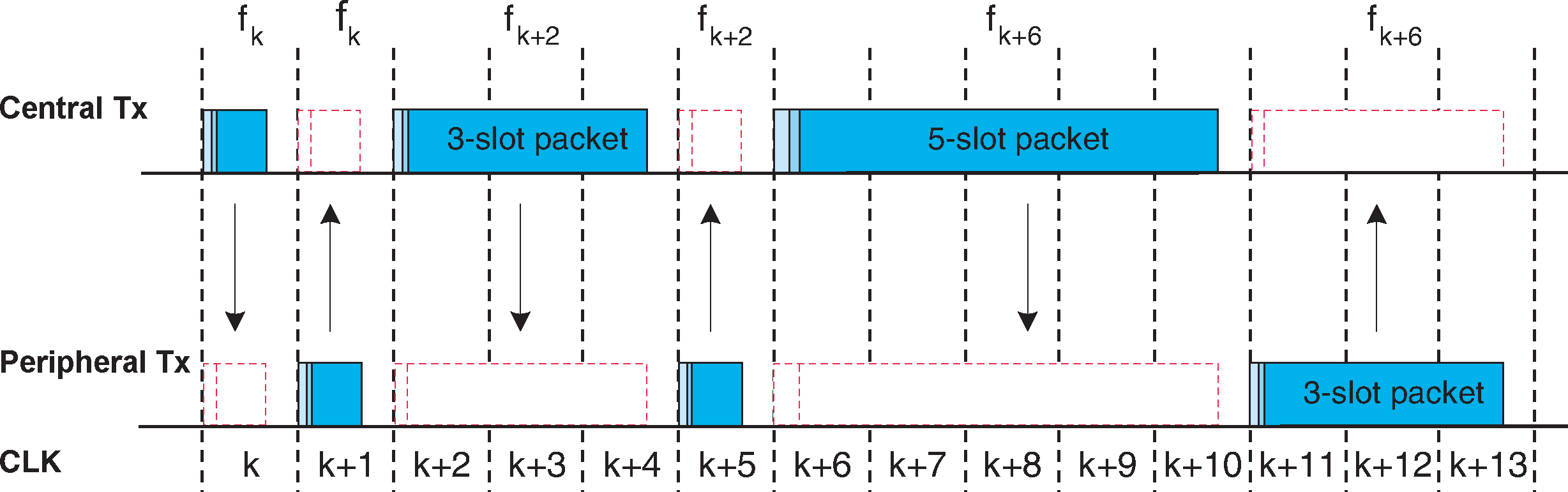
A TDD scheme is used where Central and Peripheral alternately transmit, see Figure 2.1. The packet start shall be aligned with the slot start. Packets may extend over up to five time slots.

The term slot pairs is used to indicate two adjacent time slots starting with a Central-to-Peripheral transmission slot.
2.2.4. Piconet clocks
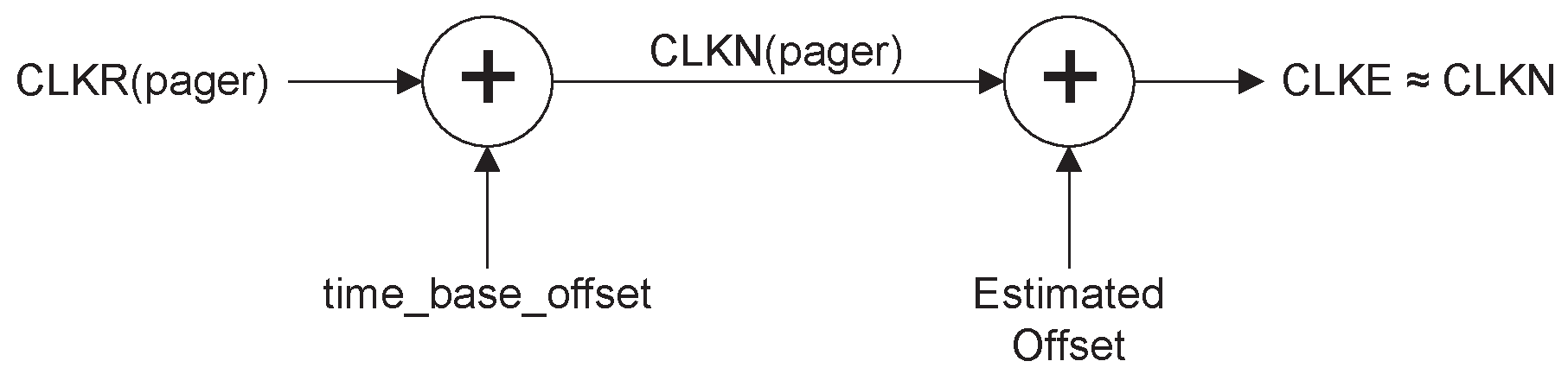
CLK is the clock of the Central of the piconet. It shall be used for all timing and scheduling activities in the piconet. All devices shall use the CLK to schedule their transmission and reception. The CLK shall be derived from the reference clock CLKR (see Section 1.1) by adding a time_base_offset and a peripheral_clock_offset, see Figure 2.2. The time_base_offset is a value that devices may use to store a locally generated offset to CLKN caused by alignment to an external time base. The peripheral_clock_offset shall be zero for the Central since CLK is identical to its own native clock CLKN. Each Peripheral shall add an appropriate peripheral_clock_offset to its CLKN such that the CLK corresponds to the CLKN of the Central. Although all CLKNs in the devices run at the same nominal rate, mutual drift causes inaccuracies in CLK. Therefore, the peripheral_clock_offset in the Peripherals must be regularly updated such that CLK is approximately CLKN of the Central.
 |
Changes in time_base_offset are only made by the Central of a piconet; a device acting only as a Peripheral has no need to distinguish CLKR and CLKN in normal operation. In a scatternet situation, a Controller may be changing both time_base_offset to align its CLKN with an external clock, either collocated or at the request of a Peripheral, and peripheral_clock_offset to maintain synchronization with a different piconet clock. In some cases, it is not possible to determine how much of an observed offset is caused by external frame timing alignment (time_base_offset) and how much is caused by the offset between Central and Peripheral (peripheral_clock_offset).
2.2.5. Transmit/receive timing
The Central transmission shall always start at even numbered time slots (CLK1=0) and the Peripheral transmission shall always start at odd numbered time slots (CLK1=1). Due to packet types that cover more than a single slot, Central transmission may continue in odd numbered slots and Peripheral transmission may continue in even numbered slots, see Figure 2.1.
All timing diagrams shown in Section 2 are based on the signals as present at the antenna. The term “exact” when used to describe timing refers to an ideal transmission or reception and neglects timing jitter and clock frequency imperfections.
The average timing of packet transmission shall not drift faster than 20 ppm relative to the ideal slot timing of 625 μs. The instantaneous timing shall not deviate more than 1 μs from the average timing. Thus, the absolute packet transmission timing tk of slot boundary k shall fulfill the equation:
where TN is the nominal slot length (625 μs), jk denotes jitter () at the start of slot k, and, dk, denotes the drift () within slot k. The jitter and drift can vary arbitrarily within the given limits for every slot, while offset is an arbitrary but fixed constant. For Hold and Sniff modes the drift and jitter parameters specified in Link Manager Protocol [Vol 2] Part C, Section 4.3.1 apply.
2.2.5.1. Piconet physical channel timing
In the figures, only single-slot packets are shown as an example.
The Central TX/RX timing is shown in Figure 2.3. In Figure 2.3 and Figure 2.4 the channel hopping frequencies are indicated by f(k) where k is the time slot number. After transmission, a return packet is expected N × 625 μs after the start of the TX packet where N is an odd, integer larger than 0. N depends on the type of the transmitted packet.
To allow for some time slipping, an uncertainty window is defined around the exact receive timing. During normal operation, the window length shall be 20 μs, which allows the RX packet to arrive up to 10 μs too early or 10 μs too late. It is recommended that Peripherals implement variable sized windows or time tracking to accommodate a Central's absence of more than 250 ms.
During the beginning of the RX cycle, the access correlator shall search for the correct channel access code over the uncertainty window. If an event trigger does not occur the receiver may go to sleep until the next RX event. If in the course of the search, it becomes apparent that the correlation output will never exceed the final threshold, the receiver may go to sleep earlier. If a trigger event occurs, the receiver shall remain open to receive the rest of the packet unless the packet is for another device, a non-recoverable header error is detected, or a non-recoverable payload error is detected.
 |
Each Central transmission shall be derived from bit 2 of the Central's native Bluetooth clock, thus the current transmission will be scheduled M × 1250 μs after the start of the previous Central TX burst where M depends on the transmitted and received packet type and is an even, integer larger than 0. The Central TX timing shall be derived from the Central's native Bluetooth clock, and thus it will not be affected by time drifts in the Peripheral(s).
Peripherals maintain an estimate of the Central’s native clock by adding a timing offset to the Peripheral’s native clock (see Section 2.2.4). This offset shall be updated each time a packet is received from the Central. By comparing the exact RX timing of the received packet with the estimated RX timing, Peripherals shall correct the offset for any timing misalignments. Since only the channel access code is required to synchronize the Peripheral, Peripheral RX timing can be corrected with any packet sent in the Central-to-Peripheral transmission slot.
The Peripheral's TX/RX timing is shown in Figure 2.4. The Peripheral’s transmission shall be scheduled N × 625 μs after the start of the Peripheral’s RX packet where N is an odd, positive integer larger than 0. If the Peripheral’s RX timing drifts, so will its TX timing. During periods when a Peripheral is in the Active mode (see Section 8.6) and is prevented from receiving valid channel access codes from the Central due to local RF interference, Peripheral activity in a different piconet, or any other reason, the Peripheral may increase its receive uncertainty window and/or use predicted timing drift to increase the probability of receiving the Central's bursts when reception resumes.
 |
2.2.5.2. Piconet physical channel re-synchronization
In the piconet physical channel, a Peripheral can lose synchronization if it does not receive a packet from the Central at least every 200 ms (or less if the low power clock is used). The Central may fail to transmit to the Peripheral due to the Central being busy with other tasks such as maintaining connections to other devices in Sniff or Hold modes, due to SCO, eSCO, or Connectionless Peripheral Broadcast activity, due to the Central being involved in a scatternet, or due to interference. When re-synchronizing to the piconet physical channel a Peripheral shall listen for the Central before it may send information (except for a Connectionless Peripheral Broadcast Receiver device which shall listen for the Transmitter but does not send information). In this case, the length of the synchronization search window in the Peripheral may be increased from 20 µs to a larger value X µs as illustrated in Figure 2.5. Only RX hop frequencies are used: the hop frequency used in the Central-to-Peripheral (RX) slot shall also be used in the uncertainty window, even when it is extended into the preceding time interval normally used for the Peripheral-to-Central (TX) slot.
If the length of search window, X, exceeds 1250 µs, consecutive windows shall avoid overlapping search windows. Consecutive windows should instead be centered at f(k), f(k+4),... f(k+4i) (where 'i' is an integer), which gives a maximum value X=2500 µs, or even at f(k), f(k+6),...f(k+6i) which gives a maximum value X=3750 µs. The RX hop frequencies used shall correspond to the Central-to-Peripheral transmission slots.
It is recommended that single slot packets are transmitted by the Central during Peripheral re-synchronization.
 |
2.3. Adapted piconet physical channel
For devices that enter Connectionless Peripheral Broadcast mode, the device that transmits Connectionless Peripheral Broadcast packets is the Central of the piconet and any device that receives Connectionless Peripheral Broadcast packets is a Peripheral of the piconet.
2.3.1. Hopping characteristics
Each physical link on the adapted piconet physical channel shall use at least Nmin RF channels (where Nmin is 20).
The adapted piconet physical channel uses the adapted channel hopping sequence described in Section 2.6.
Adapted piconet physical channels can be used for connected devices that have adaptive frequency hopping (AFH) enabled. There are two distinctions between basic and adapted piconet physical channels. The first is the same channel mechanism that makes the Peripheral frequency the same as the preceding Central transmission. The second aspect is that the adapted piconet physical channel may be based on less than the full 79 frequencies of the basic piconet physical channel. Each physical link on an adapted piconet physical channel may use a different set of frequencies.
2.4. Page scan physical channel
Although Central and Peripheral roles are not defined prior to a connection, the term Central is used for the paging device (that becomes a Central in the Connection state) and Peripheral is used for the page scanning device (that becomes a Peripheral in the Connection state).
2.4.1. Clock estimate for paging
A paging device uses an estimate of the native clock of the page scanning device, CLKE; i.e. an offset shall be added to the CLKN of the pager to approximate the CLKN of the recipient, see Figure 2.6. CLKE shall be derived from the native CLKN by adding an offset. By using the CLKN of the recipient, the pager might be able to speed up the connection establishment.
Note
Note: CLKR is never used for deriving CLKE or for any other control of the hopping kernel.
2.4.2. Hopping characteristics
The page scan physical channel follows a slower hopping pattern than the basic piconet physical channel and is a short pseudo-random hopping sequence through the RF channels. The timing of the page scan channel shall be determined by the native Bluetooth clock of the scanning device. The frequency hopping sequence is determined by the Bluetooth address of the scanning device.
The page scan physical channel uses the page, Central page response, Peripheral page response, and page scan hopping sequences specified in Section 2.6.
2.4.3. Paging procedure timing
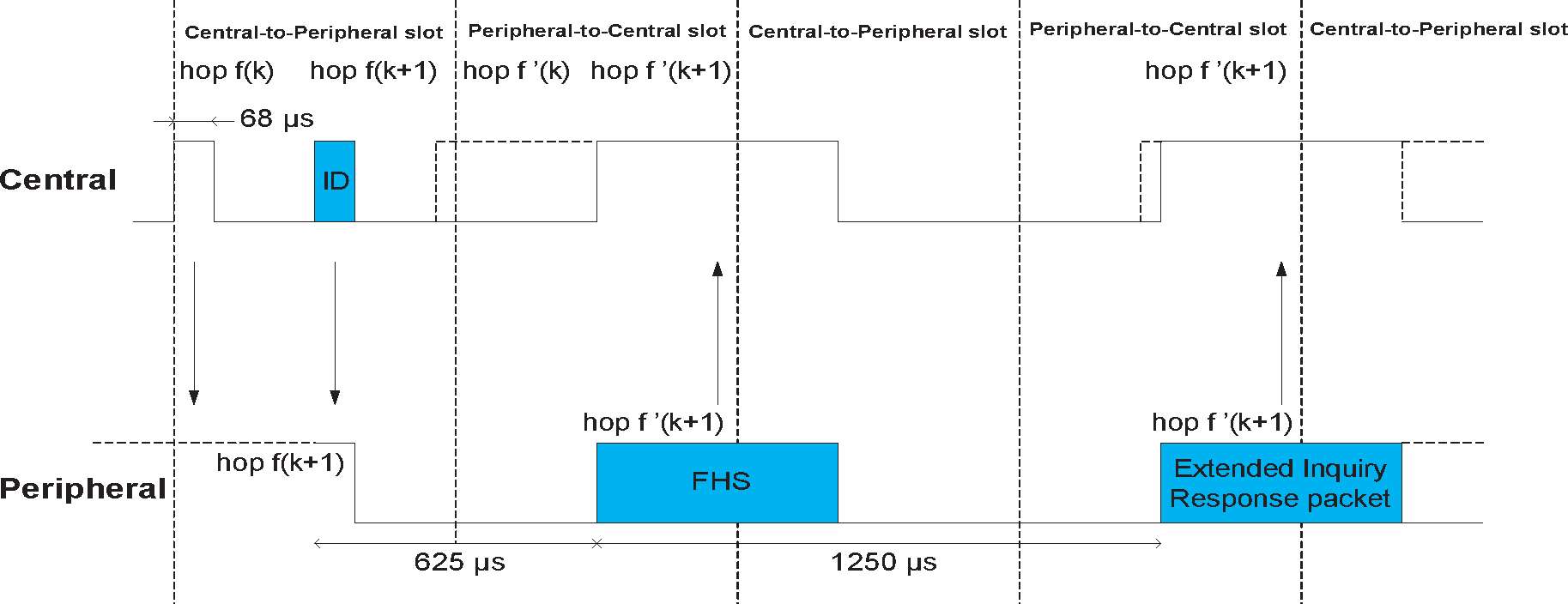
During the paging procedure, the Central shall transmit paging messages (see Table 8.3) corresponding to the Peripheral to be connected. Since the paging message is a very short packet, the hop rate is 3200 hops per second. In a single TX slot interval, the paging device shall transmit on two different hop frequencies. In Figure 2.7 to Figure 2.11, f(k) is used for the frequencies of the page hopping sequence and f'(k) denotes the corresponding page response sequence frequencies. The first transmission starts where CLK0 = 0 and the second transmission starts where CLK0 = 1.
In a single RX slot interval, the paging device shall listen for the Peripheral page response message on two different hop frequencies. Similar to transmission, the nominal reception starts where CLK0 = 0 and the second reception nominally starts where CLK0 = 1; see Figure 2.7. During the TX slot, the paging device shall send the paging message at the TX hop frequencies f(k) and f(k+1). In the RX slot, it shall listen for a response on the corresponding RX hop frequencies f’(k) and f’(k+1). The listening periods shall be exactly timed 625 μs after the corresponding paging packets, and shall include a ±10 μs uncertainty window.
2.4.4. Page response timing
At connection setup a Central page response packet is transmitted from the Central to the Peripheral (see Table 8.3). This packet establishes the timing and frequency synchronization. After the Peripheral has received the page message, it shall return a response message that consists of the Peripheral page response packet and shall follow 625 μs after the receipt of the page message. The Central shall send the Central page response packet in the TX slot following the RX slot in which it received the Peripheral’s response, according to the RX/TX timing of the Central. The time difference between the Peripheral page response and Central page response message will depend on the timing of the page message the Peripheral received. In Figure 2.8, the Peripheral receives the paging message sent first in the Central-to-Peripheral slot. It then responds with a first Peripheral page response packet in the first half of the Peripheral-to-Central slot. The timing of the Central page response packet is based on the timing of the page message sent first in the preceding Central-to-Peripheral slot: there is an exact 1250 μs delay between the first page message and the Central page response packet. The packet is sent at the hop frequency f(k+1) which is the hop frequency following the hop frequency f(k) the page message was received in.

In Figure 2.9, the Peripheral receives the paging message sent second in the Central-to-Peripheral slot. It then responds with a Peripheral page response packet in the second half of the Peripheral-to-Central slot exactly 625 μs after the receipt of the page message. The timing of the Central page response packet is still based on the timing of the page message sent first in the preceding Central-to-Peripheral slot: there is an exact 1250 μs delay between the first page message and the Central page response packet. The packet is sent at the hop frequency f(k+2) which is the hop frequency following the hop frequency f(k+1) the page message was received in.
The Peripheral shall adjust its RX/TX timing according to the reception of the Central page response packet (and not according to the reception of the page message). That is, the second Peripheral page response message that acknowledges the reception of the Central page response packet shall be transmitted 625 μs after the start of the Central page response packet.
2.5. Inquiry scan physical channel
Although Central and Peripheral roles are not defined prior to a connection, the term Central is used for the inquiring device and Peripheral is used for the inquiry scanning device.
2.5.1. Clock for inquiry
The clock used for inquiry and inquiry scan shall be the device's native clock.
2.5.2. Hopping characteristics
The inquiry scan channel follows a slower hopping pattern than the piconet physical channel and is a short pseudo-random hopping sequence through the RF channels. The timing of the inquiry scan channel is determined by the native Bluetooth clock of the scanning device while the frequency hopping sequence is determined by the general inquiry access code.
The inquiry scan physical channel uses the inquiry, inquiry response, and inquiry scan hopping sequences described in Section 2.6.
2.5.3. Inquiry procedure timing
During the inquiry procedure, the Central shall transmit inquiry messages with the general or dedicated inquiry access code. The timing for inquiry is the same as for paging (see Section 2.4.3).
2.5.4. Inquiry response timing
An inquiry response packet is transmitted from the Peripheral to the Central after the Peripheral has received an inquiry message (see Table 8.5). This packet contains information necessary for the inquiring Central to page the Peripheral (see definition of the FHS packet in Section 6.5.1.4) and follows 625 μs after the receipt of the inquiry message. If the Peripheral transmits an extended inquiry response packet, it shall be transmitted 1250 μs after the start of the inquiry response packet.
In Figure 2.10 and Figure 2.11, f(k) is used for the frequencies of the inquiry hopping sequence and f'(k) denotes the corresponding inquiry response sequence frequency. The inquiry response packet and the extended inquiry response packet are received by the Central at the hop frequency f'(k) when the inquiry message received by the Peripheral was first in the Central-to-Peripheral slot.
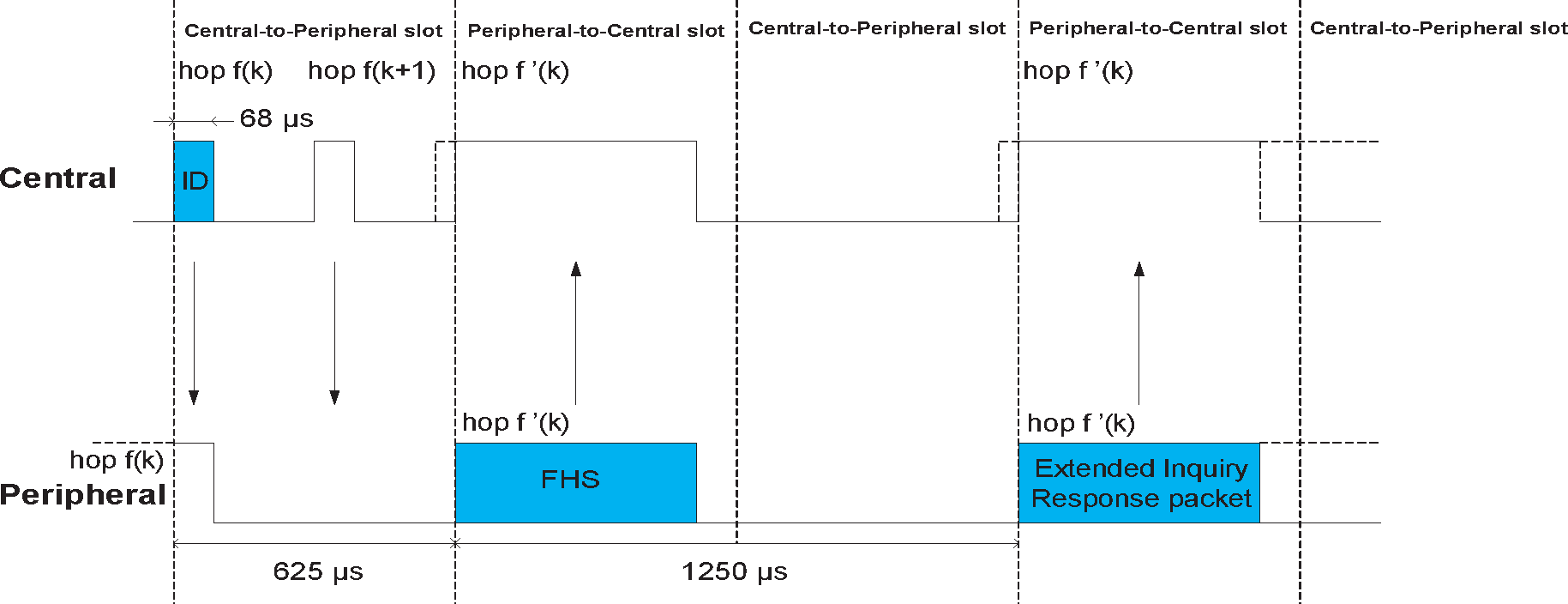
When the inquiry message received by the Peripheral was the second in the Central-to-Peripheral slot the inquiry response packet and the extended inquiry response packet are received by the Central at the hop frequency f'(k+1).
2.6. Hop selection
Bluetooth devices shall use the hopping kernel as defined in the following sections.
In total, six types of hopping sequence are defined – five for the basic hop system and one for an adapted set of hop locations used by adaptive frequency hopping (AFH). These sequences are:
A page hopping sequence with 32 wake-up frequencies distributed equally over the 79 MHz, with a period length of 32.
A page response hopping sequence covering 32 response frequencies that are in a one-to-one correspondence to the current page hopping sequence. The Central and Peripheral use different rules to obtain the same sequence.
An inquiry hopping sequence with 32 wake-up frequencies distributed equally over the 79 MHz, with a period length of 32.
An inquiry response hopping sequence covering 32 response frequencies that are in a one-to-one correspondence to the current inquiry hopping sequence.
A basic channel hopping sequence which has a very long period length, which does not show repetitive patterns over a short time interval, and which distributes the hop frequencies equally over the 79 MHz during a short time interval.
An adapted channel hopping sequence derived from the basic channel hopping sequence which uses the same channel mechanism and may use fewer than 79 frequencies. The adapted channel hopping sequence is only used in place of the basic channel hopping sequence. All other hopping sequences are not affected by hop sequence adaptation.
In addition, a set of synchronization train RF channels with 3 fixed frequencies is defined.
2.6.1. General selection scheme
The selection scheme consists of two parts:
selecting a sequence;
mapping this sequence onto the hop frequencies.
The general block diagram of the hop selection scheme is shown in Figure 2.12. The mapping from the input to a particular RF channel index is performed in the selection box.
The inputs to the selection box are the selected clock, frozen clock, N, koffset, interlace_offset, address, sequence selection and AFH_channel_map. The source of the clock input depends on the hopping sequence selected. Additionally, each hopping sequence uses different bits of the clock (see Table 2.2). N, interlace_offset, and koffset are defined in Section 2.6.4.
The sequence selection input can be set to the following values:
page scan
inquiry scan
page
inquiry
Central page response
Peripheral page response
inquiry response
basic channel
adapted channel
The address input consists of 28 bits as specified in Table 2.3 (see Section 2.6.4). The hopping sequence is selected by the sequence selection input to the selection box.
When the adapted channel hopping sequence is selected, the AFH_channel_map is an additional input to the selection box. The AFH_channel_map indicates which channels shall be used and which shall be unused. These terms are defined in Section 2.6.3.

The output, RF channel index, constitutes a pseudo-random sequence. The RF channel index is mapped to RF channel frequencies using the equation in [Vol 2] Part A, Table 2.1.
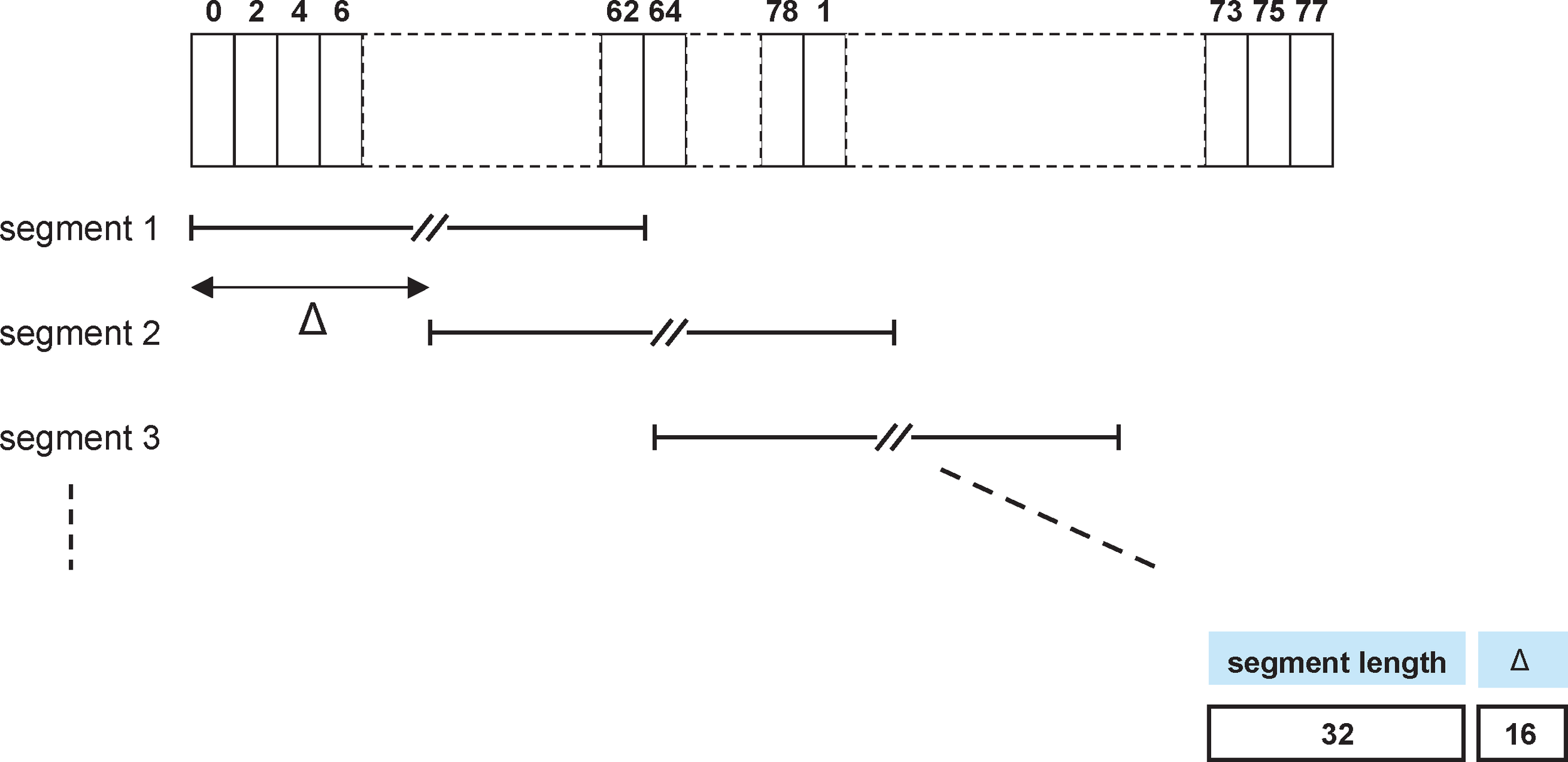
The selection scheme chooses a segment of 32 hop frequencies spanning about 64 MHz and visits these hops in a pseudo-random order. Next, a different 32-hop segment is chosen, etc. In the page, Central page response, Peripheral page response, page scan, inquiry, inquiry response and inquiry scan hopping sequences, the same 32-hop segment is used all the time (the segment is selected by the address; different devices will have different paging segments). When the basic channel hopping sequence is selected, the output constitutes a pseudo-random sequence that slides through the 79 hops. The principle is depicted in Figure 2.13.
The RF frequency shall remain fixed for the duration of the packet. The RF frequency for the packet shall be derived from the Bluetooth clock value in the first slot of the packet. The RF frequency in the first slot after a multi-slot packet shall use the frequency as determined by the Bluetooth clock value for that slot. Figure 2.14 illustrates the hop definition on single- and multi-slot packets.
When the adapted channel hopping sequence is used, the pseudo-random sequence contains only frequencies that are in the RF channel set defined by the AFH_channel_map input. The adapted sequence has similar statistical properties to the non-adapted hop sequence. In addition, the Peripheral responds with its packet on the same RF channel that was used by the Central to address that Peripheral (or would have been in the case of a synchronous reserved slot without a validly received Central-to-Peripheral transmission). This is called the same channel mechanism of AFH. Thus, the RF channel used for the Central to Peripheral packet is also used for the immediately following Peripheral to Central packet. An example of the same channel mechanism is illustrated in Figure 2.15. The same channel mechanism shall be used whenever the adapted channel hopping sequence is selected.
2.6.2. Selection kernel
The basic hop selection kernel shall be as shown in Figure 2.16 and is used for the page, page response, inquiry, inquiry response and basic channel hopping selection kernels. In these substates the AFH_channel_map input is unused. The adapted channel hopping selection kernel is described in Section 2.6.3. The X input determines the phase in the 32-hop segment, whereas Y1 and Y2 selects between Central-to-Peripheral and Peripheral-to-Central. The inputs A to D determine the ordering within the segment, the inputs E and F determine the mapping onto the hop frequencies. The kernel addresses a register containing the RF channel indices. This list is ordered so that first all even RF channel indices are listed and then all odd hop frequencies. In this way, a 32-hop segment spans about 64 MHz.
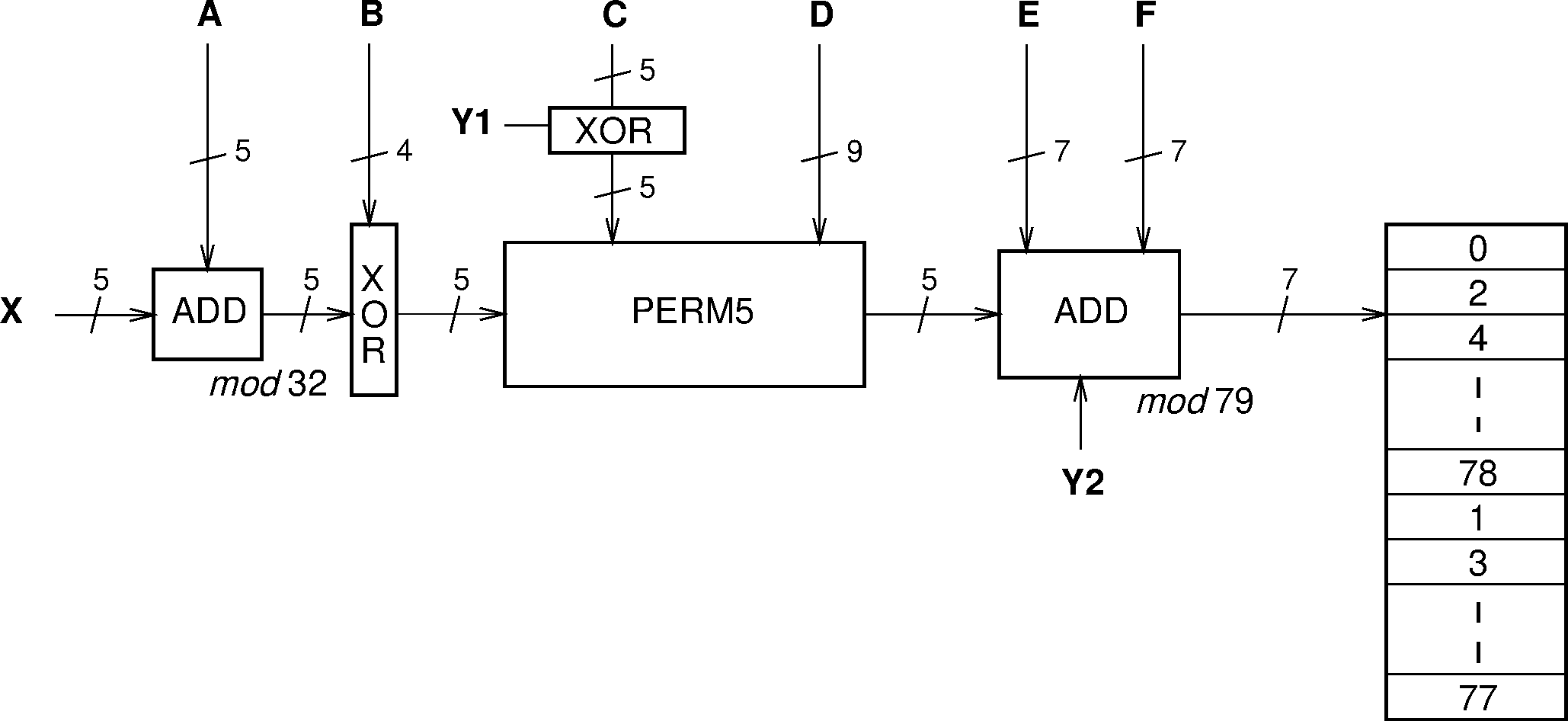
The selection procedure consists of an addition, an XOR operation, a permutation operation, an addition, and finally a register selection. In Section 2.6.2 and Table 2.2, the notation Ai is used for bit i of the BD_ADDR.
2.6.2.1. First addition operation
The first addition operation only adds a constant to the phase and applies a mod 32 operation. For the page hopping sequence, the first addition is redundant since it only changes the phase within the segment. However, when different segments are concatenated (as in the basic channel hopping sequence), the first addition operation will have an impact on the resulting sequence.
2.6.2.2. XOR operation
In the XOR operation, the four LSBs of the output of the first addition (designated Z′ here) are XORed with the address bits A22-19, while the Z′4 bit is left unaltered. The operation is illustrated in Figure 2.17.

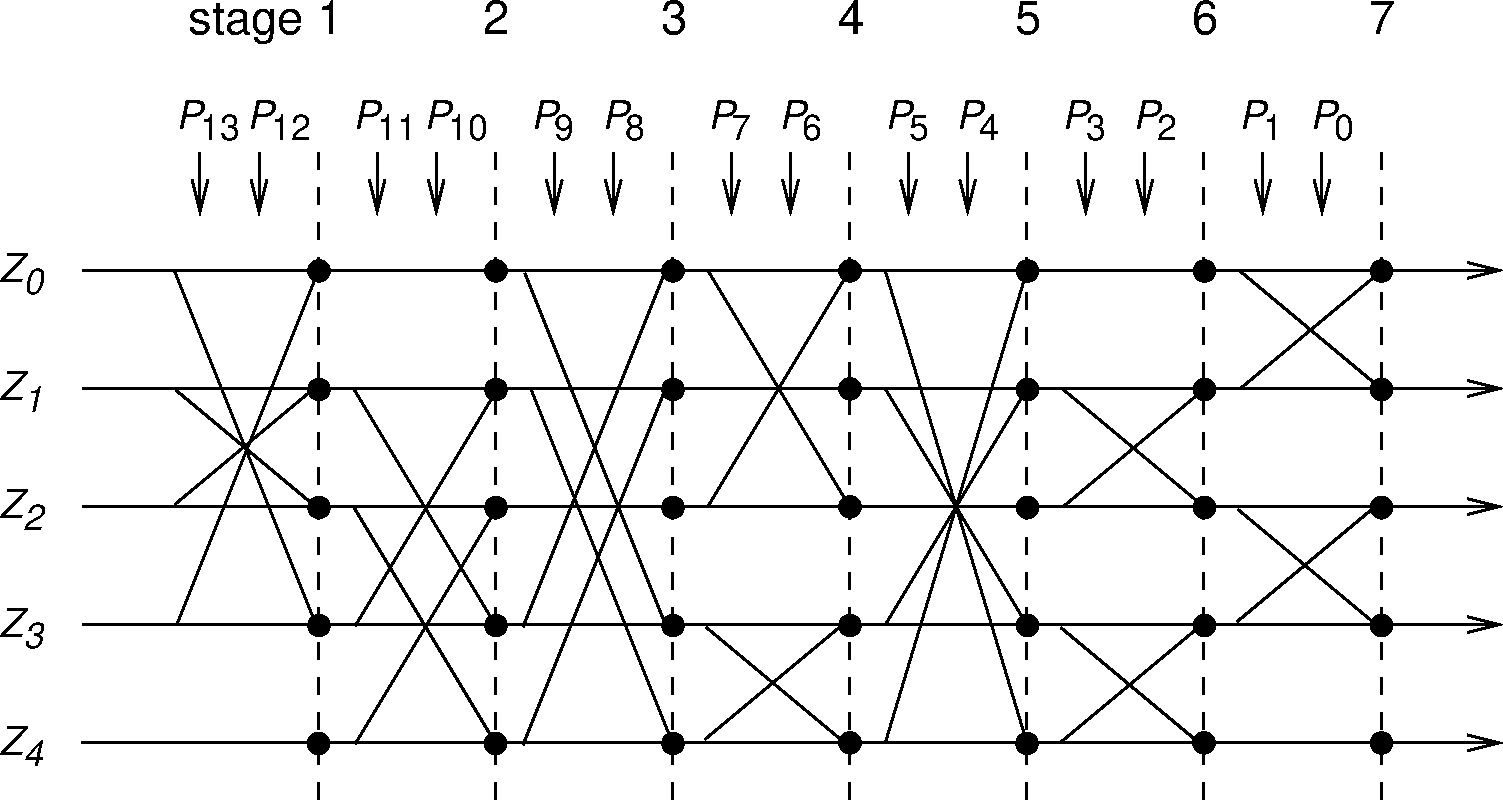
2.6.2.3. Permutation operation
The permutation operation involves the switching from 5 inputs to 5 outputs for the hop system, controlled by the control word. The permutation or switching box shall be as shown in Figure 2.18. It consists of 7 stages of butterfly operations. The control of the butterflies by the control signals P is shown in Table 2.1. P0-8 corresponds to D0-8, and, Pi+9 corresponds to for in Figure 2.16.
Control signal | Butterfly | Control signal | Butterfly |
|---|---|---|---|
P0 | {Z0,Z1} | P7 | {Z3,Z4} |
P1 | {Z2,Z3} | P8 | {Z1,Z4} |
P2 | {Z1,Z2} | P9 | {Z0,Z3} |
P3 | {Z3,Z4} | P10 | {Z2,Z4} |
P4 | {Z0,Z4} | P11 | {Z1,Z3} |
P5 | {Z1,Z3} | P12 | {Z0,Z3} |
P6 | {Z0,Z2} | P13 | {Z1,Z2} |
The Z input is the output of the XOR operation as described in the previous section. The butterfly operation can be implemented with multiplexers as depicted in Figure 2.19.
 |
 |
2.6.2.4. Second addition operation
The addition operation selects the hop frequencies to be used by the current segment and also switches between Central-to-Peripheral and Peripheral-to-Central. It adds the output of the current permutation (which selects a channel within the segment), a constant, the clock bit selecting Central or Peripheral slots, and a value used to switch each segment to a new set of channels in Connection state. The addition is applied mod 79.
2.6.2.5. Register bank
The output of the adder addresses a bank of 79 registers. The registers are loaded with the synthesizer code words corresponding to the hop frequencies 0 to 78.
The upper half of the bank contains the even hop frequencies, whereas the lower half of the bank contains the odd hop frequencies.
2.6.3. Adapted hop selection kernel
The adapted hop selection kernel is based on the basic hop selection kernel defined in the preceding sections.
The inputs to the adapted hop selection kernel are the same as for the basic hop system kernel except that the input AFH_channel_map (defined in Link Manager Protocol [Vol 2] Part C, Section 5.2) is used. The AFH_channel_map indicates which RF channels shall be used and which shall be unused. When hop sequence adaptation is enabled, the number of used RF channels may be reduced from 79 to some smaller value N. All devices shall be capable of operating on an adapted hop sequence (AHS) with Nmin ≤ N ≤ 79, with any combination of used RF channels within the AFH_channel_map that meets this constraint. Nmin is defined in Section 2.3.1.
Adaptation of the hopping sequence is achieved through two additions to the basic channel hopping sequence according to Figure 2.16:
Unused RF channels are re-mapped uniformly onto used RF channels. That is, if the hop selection kernel of the basic system generates an unused RF channel, an alternative RF channel out of the set of used RF channels is selected pseudo-randomly.
The used RF channel generated for the Central-to-Peripheral packet is also used for the immediately following Peripheral-to-Central packet (see Section 2.6.1).
2.6.3.1. Channel re-mapping function
When the adapted hop selection kernel is selected, the basic hop selection kernel according to Figure 2.16 is initially used to determine an RF channel. If this RF channel is unused according to the AFH_channel_map, the unused RF channel is re-mapped by the re-mapping function to one of the used RF channels. If the RF channel determined by the basic hop selection kernel is already in the set of used RF channels, no adjustment is made. The hop sequence of the (non-adapted) basic hop equals the sequence of the adapted selection kernel on all locations where used RF channels are generated by the basic hop. This property facilitates all Peripherals remaining synchronized even if they are not all using the same hopping sequence.
A block diagram of the re-mapping mechanism is shown in Figure 2.20. The re-mapping function is a post-processing step to the selection kernel from Figure 2.16, denoted as ‘Hop selection of the basic hop’. The output fk of the basic hop selection kernel is an RF channel number that ranges between 0 and 78. This RF channel will either be in the set of used RF channels or in the set of unused RF channels.
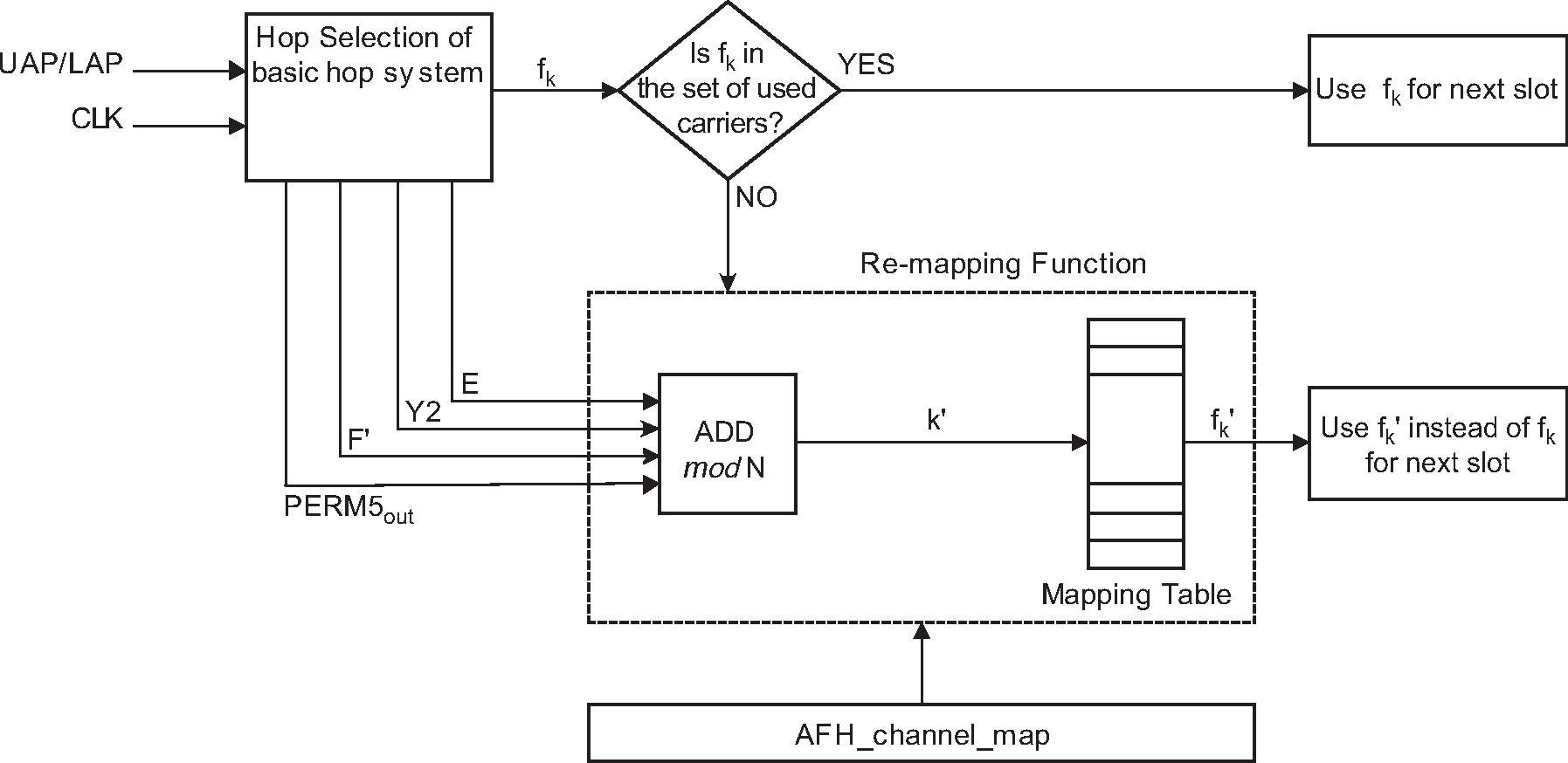
When an unused RF channel is generated by the basic hop selection mechanism, it is re-mapped to the set of used RF channels as follows. A new index k’ ∈ {0, 1,..., N-1} is calculated using some of the parameters from the basic hop selection kernel:
k’ = (PERM5out + E + F’ + Y2) mod N
where F’ is defined in Table 2.2. The index k’ is then used to select the re-mapped channel from a mapping table that contains all of the even used RF channels in ascending order followed by all the odd used RF channels in ascending order (i.e., the mapping table of Figure 2.16 with all the unused RF channels removed).
2.6.4. Control word
The control word of the kernel is controlled by the overall control signals X, Y1, Y2, A to F, and F’ as illustrated in Figure 2.16 and Figure 2.20. During paging and inquiry, the inputs A to E use the address values as given in the corresponding columns of Table 2.2. In addition, the inputs X, Y1 and Y2 are used. The F and F’ inputs are unused. The clock bits CLK6-2 (i.e., input X) specify the phase within the length 32 sequence. CLK1 (i.e., inputs Y1 and Y2) is used to select between TX and RX. The address inputs determine the sequence order within segments. The final mapping onto the hop frequencies is determined by the register contents.
During the Connection state (see Section 8.5), the inputs A, C and D shall be derived from the address bits being bit-wise XORed with the clock bits as shown in the “Connection state” column of Table 2.2 (the two most significant bits, MSBs, are XORed together, the two second MSBs are XORed together, etc.).
Page scan / Generalized Interlaced Page Scan / Inquiry scan / Generalized Interlaced Inquiry Scan | Page/Inquiry | Central page response / Peripheral page response / Inquiry response | Connection state | |
|---|---|---|---|---|
X | CLKN16 – 12 / (CLKN16 – 12 + interlace offset) mod 32 / Xir4 – 0 / (Xir4 – 0 + interlace offset) mod 32 | Xp4 – 0 / Xi4 – 0 | Xprc4 – 0 / Xprp4 – 0 / Xir 4 – 0 | CLK6 – 2 |
Y1 | 0 | CLKE1 / CLKN1 | CLKE1 / CLKN1 / 1 | CLK1 |
Y2 | 0 | 32 × CLKE1 / 32 × CLKN1 | 32 × CLKE1 / 32 × CLKN1 / 32 × 1 | 32 × CLK1 |
A | A 27 – 23 | A 27 – 23 | A 27 – 23 | |
B | A 22 – 19 | A 22 – 19 | A 22 – 19 | A 22 – 19 |
C | A 8, 6, 4, 2, 0 | A 8, 6, 4, 2, 0 | A 8, 6, 4, 2, 0 | |
D | A 18 – 10 | A 18 – 10 | A 18 – 10 | |
E | A 13, 11, 9, 7, 5, 3, 1 | A 13, 11, 9, 7, 5, 3, 1 | A 13, 11, 9, 7, 5, 3, 1 | A 13, 11, 9, 7, 5, 3, 1 |
F | 0 | 0 | 0 | 16 × CLK27 – 7 mod 79 |
F’ | n/a | n/a | n/a | 16 × CLK27 – 7 mod N |
The five X input bits vary depending on the current state of the device. In the Page Scan and Inquiry Scan substates, the native clock (CLKN) shall be used. In Connection state the Central's clock (CLK) shall be used as input. The situation is somewhat more complicated for the other states.
The address bits A0 to A27 depend on the sequence selection input as specified in Table 2.3.
Sequence | A23–0 | A27–24 |
|---|---|---|
Page scan Page Central page response Peripheral page response | LAP of the device being paged | UAP3–0 of the device being paged |
Inquiry scan Inquiry Inquiry response | GIAC (0x9E8B33) | DCI (0x00) |
Basic channel Adapted channel | LAP of the Central | UAP3–0 of the Central |
2.6.4.1. Page scan and inquiry scan hopping sequences
For the transmitted access code and in the receiver correlator, the appropriate GIAC or DIAC shall be used. The application decides which inquiry access code to use depending on the purpose of the inquiry.
2.6.4.2. Page hopping sequence
When the sequence selection input is set to page, the paging device shall start using the A-train, i.e., , where f(k) is the source’s estimate of the current receiver frequency in the paged device. The index k is a function of all the inputs in Figure 2.16. There are 32 possible paging frequencies within each 1.28 second interval. Half of these frequencies belong to the A-train, the rest (i.e., ) belong to the B-train. In order to achieve the -8 offset of the A-train, a constant of 24 shall be added to the clock bits (which is equivalent to -8 due to the mod 32 operation). The B-train is obtained by setting the offset to 8. In the case where slots to receive the first Peripheral response are periodically not available, an additional offset (knudge) is added to the clock bits in order to shift the train by an integer multiple of 1.25 ms duration. A cyclic shift of the order within the trains is also necessary in order to avoid a possible repetitive mismatch between the paging and scanning devices. Thus,
where
Alternatively, each switch between the A- and B-trains may be accomplished by adding 16 to the current value of koffset (originally initialized with 24).
2.6.4.3. Peripheral page response hopping sequence
When the sequence selection input is set to Peripheral page response, in order to eliminate the possibility of losing the link due to discrepancies of the native clock CLKN and the Central’s clock estimate CLKE, the five bits CLKN16-12 shall be frozen at their current value. The value shall be frozen at the content it has in the slot where the recipient’s access code is detected. The native clock shall not be stopped; it is merely the values of the bits used for creating the X-input that are kept fixed for a while. A frozen value is denoted by an asterisk (*) in the discussion below.
For each response slot the paged device shall use an X-input value one larger (mod 32) than in the preceding response slot. However, the first response shall be made with the X-input kept at the same value as it was when the access code was recognized. Let N be a counter starting at zero. Then, the X-input in the (N + 1) -th response slot (the first response slot being the one immediately following the page slot now responding to) of the Peripheral Page Response substate is:
The counter N shall be set to zero in the slot where the Peripheral acknowledges the page (see Figure 8.3 and Figure 8.4). Then, the value of N shall be increased by one each time CLKN1 is set to zero, which corresponds to the start of a Central TX slot. The X-input shall be constructed this way until the first FHS packet is received and the immediately following response packet has been transmitted. After this the Peripheral shall enter the Connection state using the parameters received in the FHS packet.
2.6.4.4. Central page response hopping sequence
When the sequence selection input is set to Central page response, the Central shall freeze its estimate of the Peripheral's clock to the value that triggered a response from the paged device. It is equivalent to using the values of the clock estimate when receiving the Peripheral’s response (since only CLKE1 will differ from the corresponding page transmission). Thus, the values are frozen when the Peripheral’s ID packet is received. In addition to the clock bits used, the current values of koffset and knudge shall also be frozen. The Central shall adjust its X-input in the same way the paged device does, i.e., by incrementing this value by one for each time CLKE1 is set to zero. The first increment shall be done before sending the FHS packet to the paged device. Let N be a counter starting at one. The rule for forming the X-input is:
The value of N shall be increased each time CLKE1 is set to zero, which corresponds to the start of a Central TX slot.
2.6.4.5. Inquiry hopping sequence
When the sequence selection input is set to inquiry, the X-input is similar to that used in the page hopping sequence. Since no particular device is addressed, the native clock CLKN of the inquirer shall be used. Moreover, which of the two train offsets to start with is of no real concern in this state. Consequently,
where koffset and knudge are defined by (EQ 3) and (EQ 4).
The initial choice of koffset is arbitrary.
2.6.4.6. Inquiry response hopping sequence
The inquiry response hopping sequence is similar to the Peripheral page response hopping sequence with respect to the X-input. The clock input shall not be frozen, thus the following equation applies:
Furthermore, the counter N is increased not on CLKE1 basis, but rather after each FHS packet has been transmitted in response to the inquiry. There is no restriction on the initial value of N as it is independent of the corresponding value in the inquiring unit.
The Xir value used for the extended inquiry response packet shall be the same Xir value as calculated for the immediately preceding FHS packet.
2.6.4.7. Basic and adapted channel hopping sequence
In the basic and adapted channel hopping sequences, the clock bits to use in the basic or adapted hopping sequence generation shall always be derived from the Central's clock, CLK.
2.6.4.8. Synchronization train RF channels
The synchronization train and synchronization scan use RF channels from the set of three fixed RF channels with indices 0, 24, and 78.
2.7. Synchronization scan physical channel
The synchronization scan physical channel enables devices to receive synchronization train packets.
2.7.1. Hopping characteristics
When a device enters the Synchronization Scan substate, it shall scan the synchronization train RF channels using the timing defined in Section 2.7.3. Each individual scan window shall use a different RF channel than the previous two scan windows.
The synchronization scan physical channel shall use all of the synchronization train RF channels defined in Section 2.6.4.8.
2.7.2. Synchronization Train procedure timing
The Central shall use the synchronization train procedure only when Connectionless Peripheral Broadcast mode is enabled or during the Coarse Clock Adjustment Recovery Mode ( Section 8.6.10.2); these can happen concurrently. During the synchronization train procedure, the Central shall attempt to transmit synchronization train packets on all of the RF channels specified in Section 2.6.4.8. The transmission of synchronization train packets on each RF channel is independent of the transmission on other RF channels. For each RF channel, the Central shall:
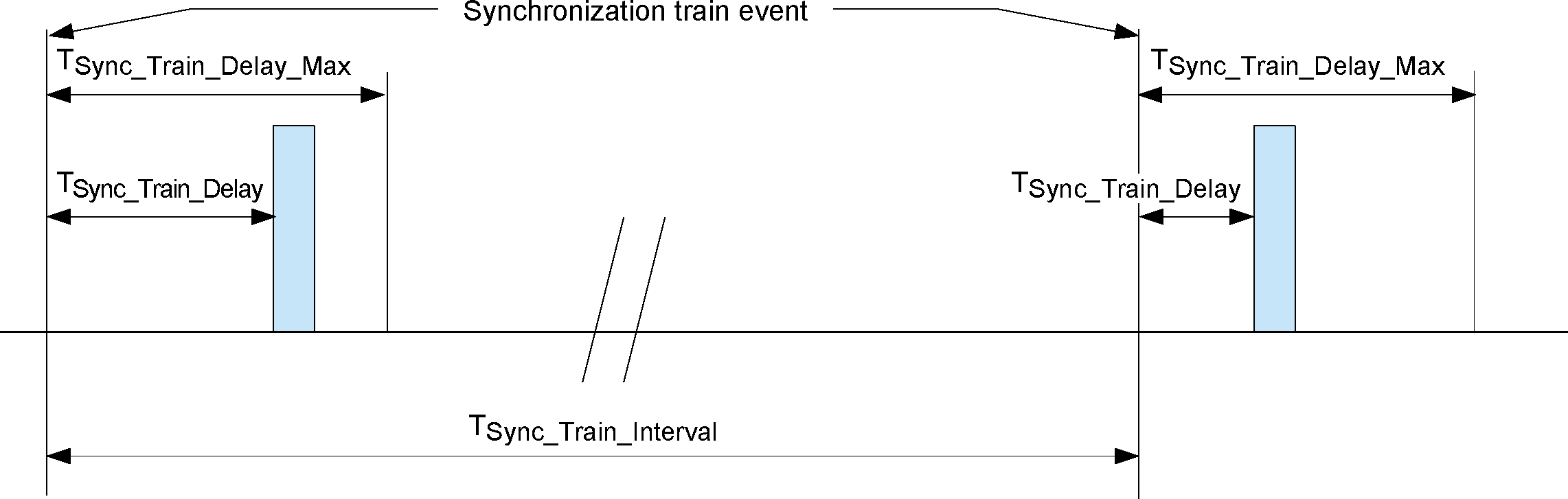
Establish synchronization train events that are separated by TSync_Train_Interval slots. During Coarse Clock Adjustment Recovery Mode the value of TSync_Train_Interval shall be 32. At all other times, it shall be the value selected by the Controller from a range provided by the Host ([Vol 4] Part E, Section 7.3.90).
Attempt to send a synchronization train packet between each pair of synchronization train events.
In the absence of scheduling conflicts, delay the start of the synchronization train packet transmission by TSync_Train_Delay slots from the synchronization train event, where TSync_Train_Delay is a (pseudo-)random number between 0 and TSync_Train_Delay_Max. Each value of TSync_Train_Delay shall be an even integer. TSync_Train_Delay_Max shall equal 4 slots during Coarse Clock Adjustment Recovery Mode and 16 slots at all other times. Each synchronization packet transmission shall start at the beginning of a time slot where CLK[1:0]=0b00.
If the transmission of the synchronization train packet conflicts with the timing of higher priority packets, the actual delay may be adjusted to avoid the conflict. The actual delay should stay within the range 0 to TSync_Train_Delay_Max and shall not be greater than or equal to TSync_Train_Interval. If it is not possible to transmit the complete packet before the next synchronization train event, it shall not be transmitted.
Increasing the delay beyond the recommended range (0 to TSync_Train_Delay_Max) increases the chance that the scanning device will miss the packet.
There shall be no more than one synchronization train packet transmitted between any two consecutive synchronization train events.
The actual delays used shall not all be the same for any three consecutive synchronization train packets (though any two may be).
Note
Note: Subject to the above requirements, synchronization train events on different RF channels may be managed separately or may be co-ordinated using the same value of TSync_Train_Delay.
Figure 2.21 shows the timing relationship of consecutive synchronization train packets on a single RF channel.
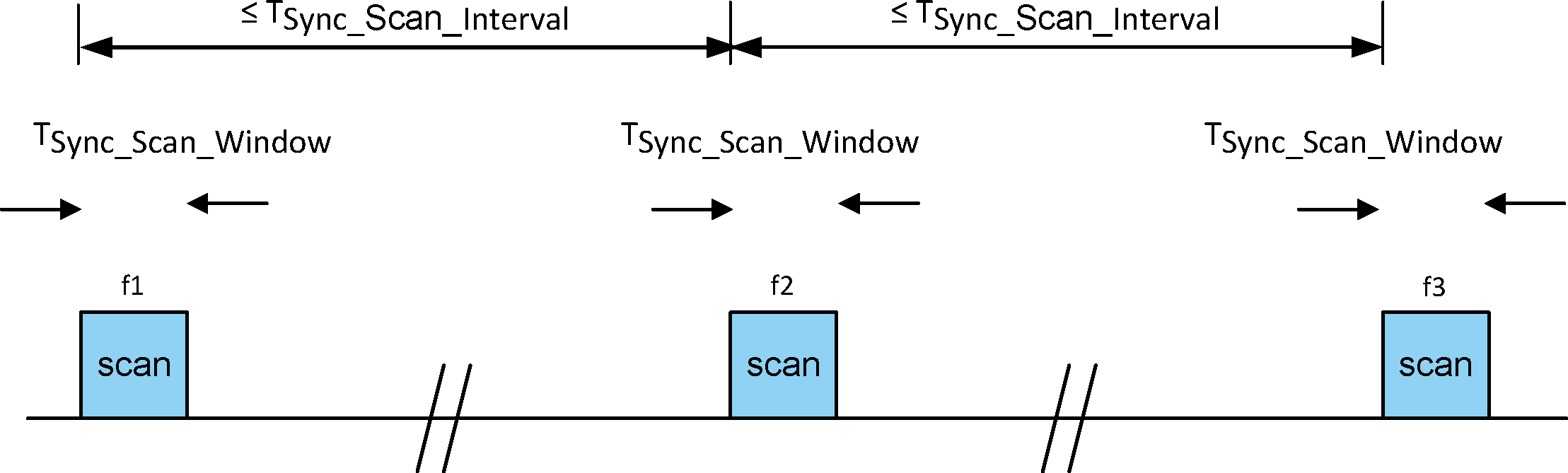
2.7.3. Synchronization Scan procedure timing
During the Synchronization Scan procedure, a device performs synchronization scans on the synchronization train RF channels. During each scan window, the device listens for the duration of TSync_Scan_Window. The RF channel for each scan window shall be selected as specified in Section 2.7.1. Each scan window should be continuous and not interrupted by other activities. The interval between the start of consecutive scan windows shall be equal to TSync_Scan_Interval. The values for TSync_Scan_Window and TSync_Scan_Interval shall be chosen as follows:
During Connectionless Peripheral Broadcast, refer to [Vol 4] Part E, Section 7.1.52.
During Coarse Clock Adjustment Recovery Mode, the values chosen are implementation specific.
This timing relationship is shown in Figure 2.22.
3. Physical links
A physical link represents a Baseband connection between devices. A physical link is always associated with exactly one physical channel. Physical links have common properties that apply to all logical transports on the physical link.
Other than the Connectionless Peripheral Broadcast physical link, common properties of physical links are:
Power control (see [Vol 2] Part C, Section 4.1.3)
Link supervision (see Section 3.1 and [Vol 2] Part C, Section 4.1.6)
Encryption (see [Vol 2] Part H, Section 4 and [Vol 2] Part C, Section 4.2.5)
Channel quality-driven data rate change (see [Vol 2] Part C, Section 4.1.7)
Multi-slot packet control (see [Vol 2] Part C, Section 4.1.10)
and for physical links on the adapted piconet physical channel:
AFH channel map (see Section 2.3 and [Vol 2] Part C, Section 4.1.4)
The Connectionless Peripheral Broadcast physical link is associated with the BR/EDR adapted piconet physical channel, a single logical transport (the CPB logical transport), and does not support the Link Manager protocol. For information on link supervision on Connectionless Peripheral Broadcast physical links, see Section 3.2. Multi-slot packets on Connectionless Peripheral Broadcast physical links are controlled by the Host and specified at the profile level.
3.1. Link supervision for active physical links
A connection can break down due to various reasons such as a device moving out of range, encountering severe interference or a power failure condition. Since this can happen without any prior warning, it is important to monitor the link on both the Central and the Peripheral side to avoid possible collisions when the logical transport address (see Section 4.2) is reassigned to another Peripheral.
To be able to detect link loss, both the Central and the Peripheral shall use a link supervision timer, T supervision. Upon reception of a valid packet header with one of the Peripheral's addresses (see Section 4.2) on the physical link, the timer shall be reset. If at any time in Connection state, the timer reaches the supervisionTO value, the connection shall be considered disconnected. The same link supervision timer shall be used for SCO, eSCO, and ACL logical transports.
The timeout period, supervisionTO, is negotiated by the Link Manager. Its value shall be chosen so that the supervision timeout will be longer than hold and sniff periods.
3.2. Link supervision for Connectionless Peripheral Broadcast physical links
For Connectionless Peripheral Broadcast physical links, only the Receiver side monitors the link. To detect link loss, the Receiver shall use a link supervision timer, TCPB_Supervision. Each Connectionless Peripheral Broadcast Receiver shall reset the timer upon reception of a Connectionless Peripheral Broadcast packet with a valid packet header. If at any time in Connectionless Peripheral Broadcast mode of the Connection state, the timer reaches the CPB_supervisionTO value, the connection shall be considered disconnected.
For each Receiver, the timeout period, CPB_supervisionTO, can be provided by the Host (see Section B.1.7).
3.3. Authenticated payload timeout for active links
For active physical links, when encryption is enabled and AES-CCM is used, a device monitors the time between receiving packets from the remote device containing a MIC. To ensure the integrity of the link, an Authenticated Payload timer, TAuthenticated_Payload, is used. Each device shall reset the timer upon reception of a packet with a valid MIC. The timer shall not be reset upon the reception of a retransmitted packet. If at any time in the Connection state, the timer reaches the authenticatedPayloadTO value, the Host shall be notified. The timeout period, authenticatedPayloadTO, shall be provided by the Host.
The device shall reset the timer each time after the Host is notified. The Controller shall reset the timer when the Host writes the authenticatedPayloadTO value.
4. Logical transports
4.1. General
Between Central and Peripheral(s), different types of logical transports may be established. Five logical transports have been defined:
Synchronous Connection-Oriented (SCO) logical transport
Extended Synchronous Connection-Oriented (eSCO) logical transport
Asynchronous Connection-Oriented (ACL) logical transport
Active Peripheral Broadcast (APB) logical transport
Connectionless Peripheral Broadcast (CPB) logical transport.
The synchronous logical transports are point-to-point logical transports between a Central and a single Peripheral in the piconet. The synchronous logical transports typically support time-bounded information like voice or general synchronous data. The Central maintains the synchronous logical transports by using reserved slots at regular intervals. In addition to the reserved slots the eSCO logical transport may have a retransmission window after the reserved slots.
The ACL logical transport is also a point-to-point logical transport between the Central and a Peripheral. In the slots not reserved for synchronous logical transport(s), the Central can establish an ACL logical transport on a per-slot basis to any Peripheral, including the Peripheral(s) already engaged in a synchronous logical transport.
The APB logical transport is used by a Central to communicate with active Peripherals.
The CPB logical transport is used by a Central to send profile broadcast data to zero or more Peripherals.
4.2. Logical transport address (LT_ADDR)
Each Peripheral active in a piconet is assigned a primary 3-bit logical transport address (LT_ADDR). The all-zero LT_ADDR is reserved for APB broadcast messages. The CPB logical transport uses a single non-zero LT_ADDR. The Central does not have an LT_ADDR. A Central's timing relative to the Peripherals’ distinguishes it from the Peripherals. A secondary LT_ADDR is assigned to the Peripheral for each eSCO logical transport in use in the piconet. The secondary LT_ADDR shall not be 0. Only eSCO traffic (i.e. NULL, POLL, and one of the EV packet types as negotiated at eSCO logical transport setup) may be sent on these LT_ADDRs. ACL traffic (including LMP) shall always be sent on the primary LT_ADDR. A Peripheral shall only accept packets with matching primary or secondary LT_ADDR and broadcast packets. The LT_ADDR is carried in the packet header (see Section 6.4). The LT_ADDR shall only be valid for as long as a Peripheral is connected. As soon as it is disconnected, the Peripheral shall lose all of its LT_ADDRs.
The primary LT_ADDR shall be assigned by the Central to the Peripheral when the Peripheral is activated. This is either at connection establishment or role switch, when the primary LT_ADDR is carried in the FHS payload.
At any given time an LT_ADDR (other than the special case of the all-zero LT_ADDR) is either unused or is used for exactly one of the three purposes of the primary address for a Peripheral, a secondary address for eSCO traffic, or for a CPB logical transport. Therefore allocating a secondary LT_ADDR for an eSCO logical transport, or reserving an LT_ADDR for the CPB logical transport, reduces the maximum number of active Peripherals possible in the piconet.
4.3. Synchronous logical transports
The first type of synchronous logical transport, the SCO logical transport, is a symmetric, point-to-point transport between the Central and a specific Peripheral. The SCO logical transport reserves slots and can therefore be considered as a circuit-switched connection between the Central and the Peripheral. The Central may support up to three SCO links to the same Peripheral or to different Peripherals. A Peripheral may support up to three SCO links from the same Central, or two SCO links if the links originate from different Centrals. SCO packets are never retransmitted.
The second type of synchronous logical transport, the eSCO logical transport, is a point-to-point logical transport between the Central and a specific Peripheral. eSCO logical transports may be symmetric or asymmetric. Similar to SCO, eSCO reserves slots and can therefore be considered a circuit-switched connection between the Central and the Peripheral. In addition to the reserved slots, eSCO supports a retransmission window immediately following the reserved slots. Together, the reserved slots and the retransmission window form the complete eSCO window.
4.4. Asynchronous logical transport
In the slots not reserved for synchronous logical transports, the Central may exchange packets with any Peripheral on a per-slot basis. The ACL logical transport provides a packet-switched connection between the Central and all active Peripherals participating in the piconet. Both asynchronous and isochronous services are supported. Only a single ACL logical transport shall exist between any two devices. For most ACL packets, packet retransmission is applied to assure data integrity.
ACL packets not addressed to a specific Peripheral (LT_ADDR=0) are considered as broadcast packets and should be received by every Peripheral except Peripherals with only a CPB logical transport. If there is no data to be sent on the ACL logical transport and no polling is required, no transmission is required.
4.5. Transmit/receive routines
This section describes the way to use the packets as defined in Section 6 in order to support the traffic on the ACL, SCO and eSCO logical transports. Both single-Peripheral and multi-Peripheral configurations are considered. In addition, the use of buffers for the TX and RX routines are described.
4.5.1. TX routine
The TX routine is carried out separately for each asynchronous and synchronous logical transport. Figure 4.1 shows the asynchronous and synchronous buffers as used in the TX routine. In this figure, only a single TX asynchronous buffer and a single TX synchronous buffer are shown. In the Central, there is a separate TX asynchronous buffer for each Peripheral. In addition there can be one or more TX synchronous buffers for each synchronous Peripheral (different SCO or eSCO logical transports could either reuse the same TX synchronous buffer, or each have their own TX synchronous buffer). Each TX buffer consists of two FIFO registers: one current register which can be accessed and read by the Link Controller in order to compose the packets, and one next register that can be accessed by the Baseband Resource Manager to load new information. The positions of the switches S1 and S2 determine which register is current and which register is next; the switches are controlled by the Link Controller. The switches at the input and the output of the FIFO registers can never be connected to the same register simultaneously.
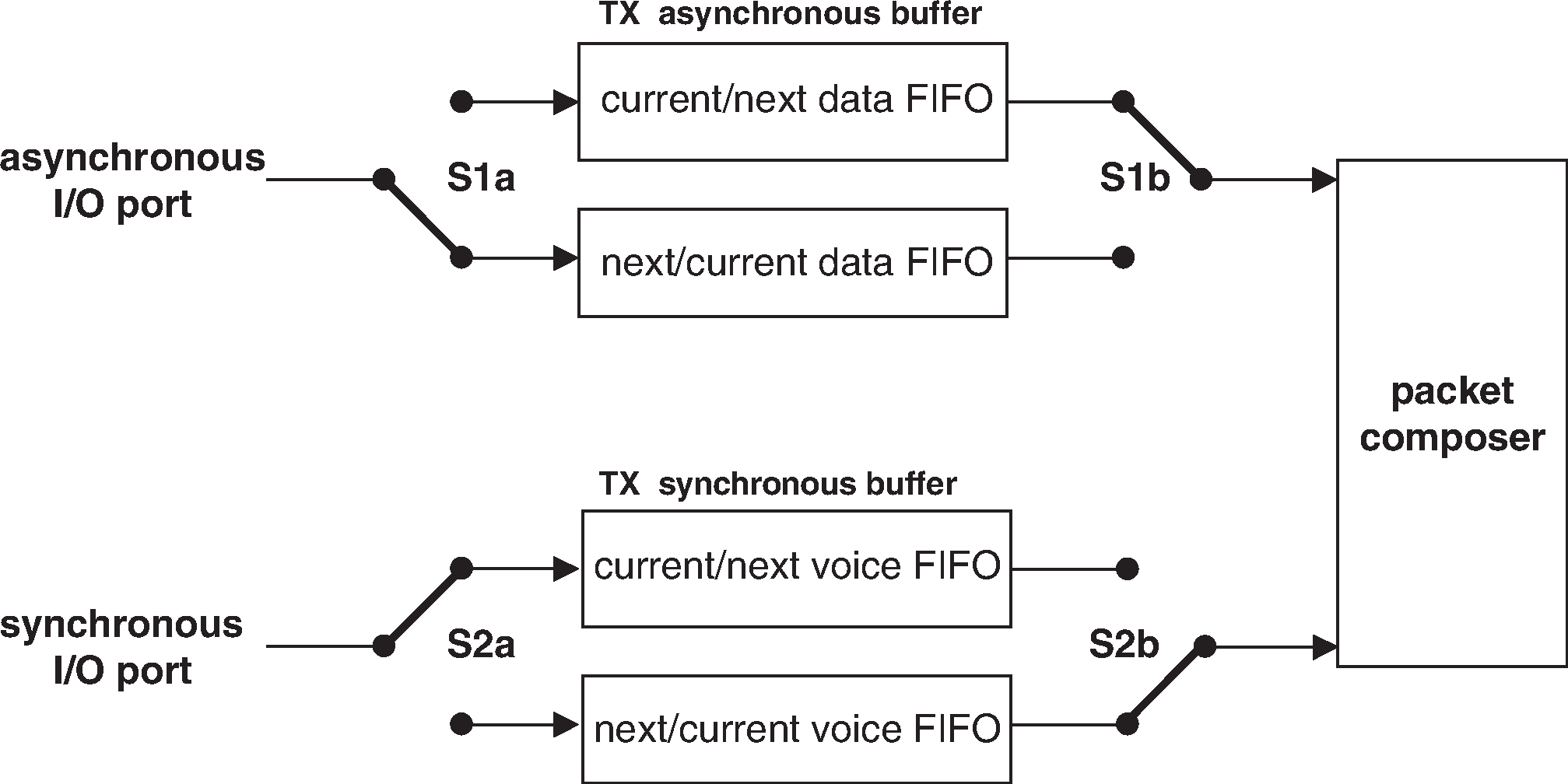 |
Of the packets common to the ACL and SCO logical transports (NULL, POLL and DM1), only the DM1 packet carries a payload that is exchanged between the Link Controller and the Link Manager; this packet makes use of the asynchronous buffer. All ACL packets make use of the asynchronous buffer. All SCO and eSCO packets make use of the synchronous buffer except for the DV packet where the synchronous data part is handled by the synchronous buffer and the data part is handled by the asynchronous buffer. In the next sections, the operation for ACL traffic, SCO traffic, eSCO traffic, and combined data-voice traffic on the SCO logical transport are described.
4.5.1.1. ACL traffic
In the case of asynchronous data only the TX ACL buffer in Figure 4.1 has to be considered. In this case, only packet types DM or DH are used, and these can have different lengths. The length is indicated in the payload header. The selection of DM or DH packets should depend on the quality of the link. See [Vol 2] Part C, Section 4.1.7.
The default packet type in pure data traffic is NULL (see Section 6.5.1.2). This means that, if there is no data to be sent (the data traffic is asynchronous, and therefore pauses occur in which no data is available) or no Peripherals need to be polled, NULL packets are sent instead – in order to send link control information to the other device (e.g. ACK/STOP information for received data). When no link control information is available (either no need to acknowledge and/or no need to stop the RX flow) no packet is sent at all.
The TX routine works as follows. The Baseband Resource Manager loads new data information in the register to which the switch S1a points. Next, it gives a command to the Link Controller, which forces the switch S1 to change (both S1a and S1b switch synchronously). When the payload needs to be sent, the packet composer reads the current register and, depending on the packet type, builds a payload which is appended to the channel access code and the header and is subsequently transmitted. In the response packet (which arrives in the following RX slot if it concerned a Central transmission, or may be postponed until some later RX slot if it concerned a Peripheral transmission), the result of the transmission is reported back. In case of an ACK, the switch S1 changes position; if a NAK (explicit or implicit) is received instead, the switch S1 will not change position. In that case, the same payload is retransmitted at the next TX occasion.
As long as the Baseband Resource Manager keeps loading the registers with new information, the Link Controller will automatically transmit the payload; in addition, retransmissions are performed automatically in case of errors. The Link Controller will send NULL or nothing when no new data is loaded. If no new data has been loaded in the next register, during the last transmission, the packet composer will be pointing to an empty register after the last transmission has been acknowledged and the next register becomes the current register. If new data is loaded in the next register, a Flush command is required to switch the S1 switch to the proper register. As long as the Baseband Resource Manager keeps loading the data and type registers before each TX slot, the data is automatically processed by the Link Controller since the S1 switch is controlled by the ACK information received in response. However, if the traffic from the Baseband Resource Manager is interrupted once and a default packet is sent instead, a Flush command is necessary to continue the flow in the Link Controller.
The Flush command may also be used in case of time-bounded (isochronous) data. In case of a bad link, many retransmissions are necessary. In certain applications, the data is time-bounded: if a payload is retransmitted all the time because of link errors, it may become outdated, and the system might decide to continue with more recent data instead and skip the payload that does not come through. This is accomplished by the Flush command as well. With the flush, the switch S1 is forced to change and the Link Controller is forced to consider the next data payload and overrules the ACK control. Any ACL type of packet can be used to send data or link control information to any other ACL Peripheral.
4.5.1.2. SCO traffic
On the SCO logical transport only HV and DV packet types are used, See Section 6.5.2. The synchronous port may continuously load the next register in the synchronous buffer. The S2 switches are changed according to the Tsco interval. This Tsco interval is negotiated between the Central and the Peripheral at the time the SCO logical transport is established.
For each new SCO slot, the packet composer reads the current register after which the S2 switch is changed. If the SCO slot has to be used to send control information with high priority concerning a control packet between the Central and the SCO Peripheral, or a control packet between the Central and any other Peripheral, the packet composer will discard the SCO information and use the control information instead. This control information shall be sent in a DM1 packet. Data or link control information may also be exchanged between the Central and the SCO Peripheral by using the DV or DM1 packets.
4.5.1.3. Mixed data/voice traffic
In Section 6.5.2, a DV packet has been defined that can support both data and voice simultaneously on a single SCO logical transport. When the TYPE is DV, the Link Controller reads the data register to fill the data field and the voice register to fill the voice field. Thereafter, the switch S2 is changed. However, the position of S1 depends on the result of the transmission as on the ACL logical transport: only if an ACK has been received will the S1 switch change its position. In each DV packet, the voice information is new, but the data information might be retransmitted if the previous transmission failed. If there is no data to be sent, the SCO logical transport will automatically change from DV packet type to the current HV packet type used before the mixed data/voice transmission.
A Flush command is necessary when the data stream has been interrupted and new data has arrived.
Combined data-voice transmission can also be accomplished by using a separate ACL logical transport in addition to the SCO logical transport(s) if channel capacity permits this.
4.5.1.4. eSCO traffic
On the eSCO logical transport only EV, POLL and NULL packet types are used, see Section 6.5.3. The synchronous port may continuously load the next register in the synchronous buffer. The S2 switches are changed according to the TeSCO interval. This TeSCO interval is negotiated between the Central and the Peripheral at the time the eSCO logical transport is established.
For each new eSCO slot, the packet composer reads the current register after which the S2 switch is changed. If the eSCO slot has to be used to send control information with high priority concerning a control packet between the Central and the eSCO Peripheral, or an ACL packet between the Central and any other Peripheral, the packet composer will discard the eSCO information and use the control information instead. Control information to the eSCO Peripheral is sent in a DM1 packet on the primary LT_ADDR.
4.5.1.5. Default packet types
On the ACL links, the default type is always NULL both for the Central and the Peripheral. This means that if no user information needs to be sent, either a NULL packet is sent if there is ACK or STOP information, or no packet is sent at all. The NULL packet can be used by the Central to allocate the next Peripheral-to-Central slot to a certain Peripheral (namely the one addressed). However, the Peripheral is not forced to respond to the NULL packet from the Central. If the Central requires a response, it sends a POLL packet.
The SCO and eSCO packet types are negotiated at the LM level when the SCO or eSCO logical transport is established. The agreed packet type is also the default packet type for the reserved SCO or eSCO slots.
4.5.2. RX routine
The RX routine is carried out separately for the ACL logical transport and the synchronous logical transports. However, in contrast to the Central TX asynchronous buffer, a single RX buffer is shared among all Peripherals. For the synchronous buffer, how the different synchronous logical transports are distinguished depends on whether extra synchronous buffers are required or not. Figure 4.2 shows the asynchronous and synchronous buffers as used in the RX routine. The RX asynchronous buffer consists of two FIFO registers: one register that can be accessed and loaded by the Link Controller with the payload of the latest RX packet, and one register that can be accessed by the Baseband Resource Manager to read the previous payload. The RX synchronous buffer also consists of two FIFO registers: one register which is filled with newly arrived voice information, and one register which can be read by the voice processing unit.
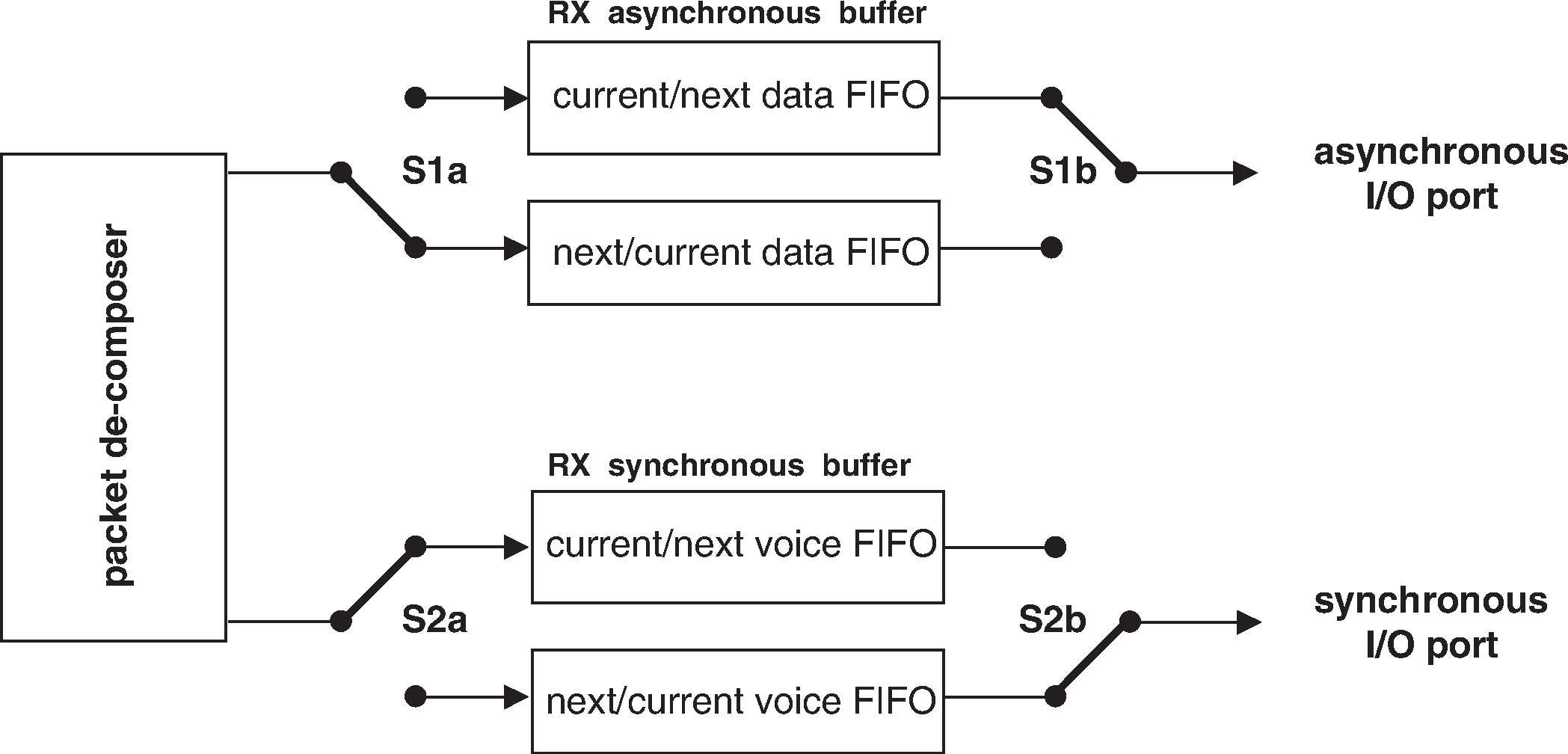 |
Since the TYPE indication in the header (see Section 6.4.2) of the received packet indicates whether the payload contains data and/or voice, the packet de-composer can automatically direct the traffic to the proper buffers. The switch S1 changes every time the Baseband Resource Manager reads the old register. If the next payload arrives before the RX register is emptied, a STOP indication is included in the packet header of the next TX packet that is returned. The STOP indication is removed again as soon as the RX register is emptied. The SEQN field is checked before a new ACL payload is stored into the asynchronous register (flush indication in LLID and broadcast messages influence the interpretation of the SEQN field see Section 7.6).
The S2 switch is changed every TSCO or TeSCO for SCO and eSCO respectively. If, due to errors in the header, no new synchronous payload arrives, the switch still changes. The synchronous data processing unit then processes the synchronous data to account for the missing parts.
4.5.3. Flow control
Since the RX ACL buffer can be full while a new payload arrives, flow control is required. The header field FLOW in the return TX packet may use STOP or GO in order to control the transmission of new data.
4.5.3.1. Destination control
As long as data cannot be received, a STOP indication shall be transmitted which is automatically inserted by the Link Controller into the header of the return packet. STOP shall be returned as long as the RX ACL buffer is not emptied by the Baseband Resource Manager. When new data can be accepted again, the GO indication shall be returned. GO shall be the default value. All packet types not including data can still be received. Voice communication for example is not affected by the flow control. Although a device can-not receive new information, it may still continue to transmit information: the flow control shall be separate for each direction.
4.5.3.2. Source control
On the reception of a STOP signal, the Link Controller shall automatically switch to the default packet type. The ACL packet transmitted just before the reception of the STOP indication shall be kept until a GO signal is received. It may be retransmitted as soon as a GO indication is received. Only default packets shall be sent as long as the STOP indication is received. When no packet is received, GO shall be assumed implicitly. The default packets contain link control information (in the header) for the receive direction (which may still be open) and may contain synchronous data (HV or EV packets). When a GO indication is received, the Link Controller may resume transmitting the data that is present in the TX ACL buffers.
In a multi-Peripheral configuration, only the transmission to the Peripheral that issued the STOP signal shall be stalled. This means that the Central shall only stop transmission from the TX ACL buffer corresponding to the Peripheral that momentarily cannot accept data.
4.6. Active Peripheral broadcast transport
The Active Peripheral Broadcast logical transport is used to transport L2CAP user traffic and certain LMP traffic to all devices in the piconet that are currently connected to the piconet physical channel that is used by the APB. There is no acknowledgment protocol and the traffic is uni-directional from the piconet Central to the Peripherals.
The APB logical transport is unreliable. To improve reliability somewhat each packet is transmitted a number of times. An identical sequence number is used to assist with filtering retransmissions at the Peripheral.
The APB logical transport is identified by the reserved, all-zero, LT_ADDR. Packets on the APB logical transport may be sent by the Central at any time.
4.7. [This section is no longer used]
4.8. Connectionless Peripheral Broadcast logical transport
The CPB logical transport is used to transport profile broadcast data from a Transmitter (Central) to multiple Receivers (Peripherals). There is no acknowledgment scheme and the traffic is unidirectional.
Note
Note: The CPB logical transport is not used for L2CAP connection-oriented channels, L2CAP control signaling, or LMP control signaling.
The CPB logical transport is unreliable. To improve reliability each packet payload may be transmitted a number of times.
5. Logical links
The following logical links are defined:
Link Control (LC)
ACL Control (ACL-C and APB-C)
User Asynchronous/Isochronous (ACL-U and APB-U)
User Synchronous (SCO-S)
User Extended Synchronous (eSCO-S)
Profile Broadcast Data (PBD)
The control logical link LC is used at the link control level. The ACL-C and APB-C logical links are used at the link manager level. The ACL-U and APB-U logical links are used to carry either asynchronous or isochronous user information. The SCO-S, and eSCO-S logical links are used to carry synchronous user information. The PBD logical link is used to carry profile broadcast data. The LC logical link is carried in the packet header, all other logical links are carried in the packet payload. The ACL-C, ACL-U, APB-C, and APB-U logical links are indicated in the logical link ID, LLID, field in the payload header. The SCO-S and eSCO-S logical links are carried by the synchronous logical transports only; the ACL-U link is normally carried by the ACL logical transport; however, it may also be carried by the data in the DV packet on the SCO logical transport. The ACL-C link may be carried either by the SCO or the ACL logical transport. The APB-C and APB-U links are carried by the APB logical transport. The PBD logical link is carried by the CPB logical transport.
5.1. Link Control logical link (LC)
The LC control logical link shall be mapped onto the packet header. This logical link carries low level link control information like ARQ, flow control, and payload characterization. The LC logical link is carried in every packet except in the ID packet which does not have a packet header.
5.2. ACL Control logical links (ACL-C and APB-C)
The ACL-C and APB-C logical links shall carry control information exchanged between the link managers of the Central and the Peripheral(s). The ACL-C logical link shall use DM1 or DV packets. DV packets shall only be used on the ACL-C link if the ACL-C message is less than or equal to 9 bytes and an HV1 synchronous logical transport is in use. The APB-C logical link shall use DM1 packets. The ACL-C and APB-C logical links are indicated by the LLID code 0b11 in the payload header.
5.3. User asynchronous/isochronous logical links (ACL‑U and APB‑U)
The ACL-U and APB-U logical links shall carry L2CAP asynchronous and isochronous user data. These messages may be transmitted in one or more Baseband packets. For fragmented messages, the start packet shall use an LLID code of 0b10 in the payload header. Remaining continuation packets shall use LLID code 0b01. If there is no fragmentation, all packets shall use the LLID start code 0b10.
For each logical link, the Controller shall transmit data over the air in the same order that it is received from the Host. The boundaries between packets over the air for a specific L2CAP PDU may be different from the boundaries in the data provided by the Host. Each new L2CAP PDU shall start a new packet over the air. (See [Vol 3] Part A, Section 7.2.1 for related requirements in L2CAP.)
For each logical link, the Controller shall transmit the data received over the air to the Host (whether over HCI or otherwise) in the same order that it was received. The boundaries in the data sent to the Host for a specific L2CAP PDU may be different from the boundaries between packets received over the air. The Controller shall retain boundaries between L2CAP PDUs. Data from different logical links may be interleaved. (See [Vol 3] Part A, Section 7.2.2 for related requirements in L2CAP.)
5.3.1. Pausing the ACL-U logical link
When paused by the LM, the Link Controller transmits the current packet with ACL-U information, if any, until an ACK is received. While the ACL-U logical link is paused, the Link Controller shall not transmit any (more) packets with ACL-U logical link information.
When the ACL-U logical link is resumed by the LM, the Link Controller may resume transmitting packets with ACL-U information.
5.4. User synchronous data logical link (SCO-S)
The SCO-S logical link carries transparent synchronous user data. This logical link is carried over the synchronous logical transport SCO.
5.5. User extended synchronous data logical link (eSCO-S)
The eSCO-S logical link also carries transparent synchronous user data. This logical link is carried over the extended synchronous logical transport eSCO.
5.6. Logical link priorities
The ACL-C logical link shall have a higher priority than the ACL-U logical link when scheduling traffic on the shared ACL logical transport, except in the case when retransmissions of unacknowledged ACL packets shall be given priority over traffic on the ACL-C logical link. The APB-C logical link shall have a higher priority than the APB-U logical link when scheduling traffic on the shared APB logical transport. The ACL-C logical link should also have priority over traffic on the SCO-S and eSCO-S logical links but opportunities for interleaving the logical links should be taken. The ACL-C, SCO-S, and eSCO-S logical links should have priority over traffic on the PBD logical link.
5.7. Profile broadcast data logical link
The PBD logical link carries profile broadcast data. Messages shall not be fragmented and shall always use LLID start code 0b10.
6. Packets
Bluetooth devices shall use the packets as defined in the following sections.
6.1. General format
6.1.1. Basic Rate
The general packet format of Basic Rate packets is shown in Figure 6.1. Each packet consists of 3 entities: the access code, the header, and the payload. In the figure, the number of bits per entity is indicated.
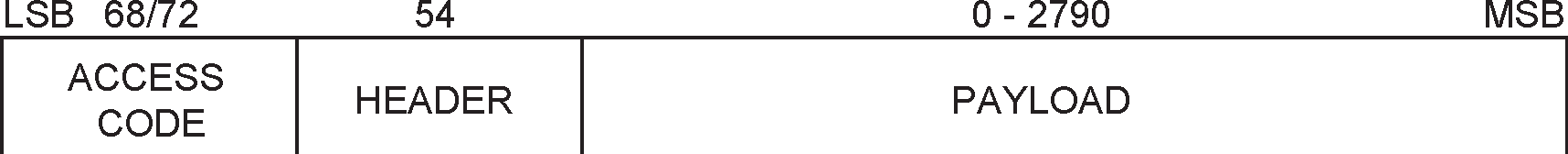
The access code is 72 or 68 bits and the header is 54 bits. The payload ranges from zero to a maximum of 2790 bits. Different packet types have been defined. A packet may consist of:
the shortened access code only (see Section 6.5.1.1)
the access code and the packet header
the access code, the packet header and the payload.
6.1.2. Enhanced Data Rate
The general format of Enhanced Data Rate packets is shown in Figure 6.2. The access code and packet header are identical in format and modulation to Basic Rate packets. Enhanced Data Rate packets have a guard time and synchronization sequence following the packet header. Following the payload are two trailer symbols. The guard time, synchronization sequence and trailer are defined in Section 6.6.

6.2. Bit ordering
The bit ordering when defining packets and messages in the Baseband Specification, follows the little-endian format. The following rules apply:
The least significant bit (LSB) corresponds to b0;
The LSB is the first bit sent over the air;
In illustrations, the LSB is shown on the left side;
Furthermore, data fields generated internally at Baseband level, such as the packet header fields and payload header length, shall be transmitted with the LSB first. For instance, a 3-bit parameter X=3 is sent as:
b0b1b2 = 110
over the air where 1 is sent first and 0 is sent last.
6.3. Access code
Every packet starts with an access code. If a packet header follows, the access code is 72 bits long, otherwise the access code is 68 bits long and is known as a shortened access code. The shortened access code does not contain a trailer. This access code is used for synchronization, DC offset compensation and identification. The access code identifies all packets exchanged on a physical channel: all packets sent in the same physical channel are preceded by the same access code. In the receiver of the device, a sliding correlator correlates against the access code and triggers when a threshold is exceeded. This trigger signal is used to determine the receive timing.
The shortened access code is used in paging and inquiry. In this case, the access code itself is used as a signaling message and neither a header nor a payload is present.
The access code consists of a preamble, a sync word, and possibly a trailer, see Figure 6.3. For details see Section 6.3.1.

6.3.1. Access code types
The different access code types use different Lower Address Parts (LAPs) to construct the sync word. The LAP field of the BD_ADDR is explained in Section 1.2. A summary of the different access code types is in Table 6.1.
Code type | LAP | Code length | Comments | ||||||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
CAC | Central | 72 | See also Section 1.3 | ||||||||||||||||||||||||||||||||||||||||||||||
DAC | Paged device | 68/72[1] | |||||||||||||||||||||||||||||||||||||||||||||||
GIAC | Reserved | 68/72[1] | |||||||||||||||||||||||||||||||||||||||||||||||
DIAC | Dedicated | 68/72[1] | |||||||||||||||||||||||||||||||||||||||||||||||
[1] length 72 is only used in combination with FHS packets | |||||||||||||||||||||||||||||||||||||||||||||||||
The CAC consists of a preamble, sync word, and trailer and its total length is 72 bits. When used as self-contained messages without a header, the DAC and IAC do not include the trailer bits and are of length 68 bits.
6.3.2. Preamble
The preamble is a fixed zero-one pattern of 4 symbols used to facilitate DC compensation. The sequence is either ‘1010’ or ‘0101’ (in transmission order), depending on whether the LSB of the following sync word is 1 or 0, respectively. The preamble is shown in Figure 6.4.

6.3.3. Sync word
The sync word is a 64-bit code word derived from a 24 bit address (LAP); for the CAC the Central’s LAP is used; for the GIAC and the DIAC, reserved, dedicated LAPs are used; for the DAC, the Peripheral LAP is used. The construction results in a large Hamming distance between sync words based on different LAPs. In addition, the good auto correlation properties of the sync word improve timing acquisition.
6.3.3.1. Synchronization word definition
The sync words are based on a (64,30) expurgated block code with an overlay (bit-wise XOR) of a 64 bit full length pseudo-random noise (PN) sequence. The expurgated code results in a large Hamming distance (dmin = 14) between sync words based on different addresses. The PN sequence improves the auto correlation properties of the access code. The following steps describe how the sync word shall be generated:
Generate information sequence;
XOR this with the “information covering” part of the PN overlay sequence;
Generate the codeword;
XOR the codeword with all 64 bits of the PN overlay sequence;
The information sequence is generated by appending 6 bits to the 24 bit LAP (step 1). The appended bits are if the MSB of the LAP equals 0. If the MSB of the LAP is 1 the appended bits are . The LAP MSB together with the appended bits constitute a length-seven Barker sequence. The purpose of including a Barker sequence is to further improve the auto correlation properties. In step 2 the information is pre-scrambled by XORing it with the bits of the PN sequence (defined in Section 6.3.3.2). After generating the codeword (step 3), the complete PN sequence is XORed to the codeword (step 4). This step de-scrambles the information part of the codeword. At the same time the parity bits of the codeword are scrambled. Consequently, the original LAP and Barker sequence are ensured a role as a part of the access code sync word, and the cyclic properties of the underlying code is removed. The principle is depicted in Figure 6.5.
In the following discussion, binary sequences will be denoted by their corresponding D-transform (in which Di represents a delay of i time units). Let be the 63 bit PN sequence, where is the first bit (LSB) leaving the PRNG (see Figure 6.6), and, is the last bit (MSB). To obtain 64 bits, an extra zero is appended at the end of this sequence (thus, is unchanged). For notational convenience, the reciprocal of this extended polynomial, , will be used in the following discussion. This is the sequence in reverse order. We denote the 24 bit lower address part (LAP) of the Bluetooth Device Address by ( is the LSB of the Bluetooth Device Address).
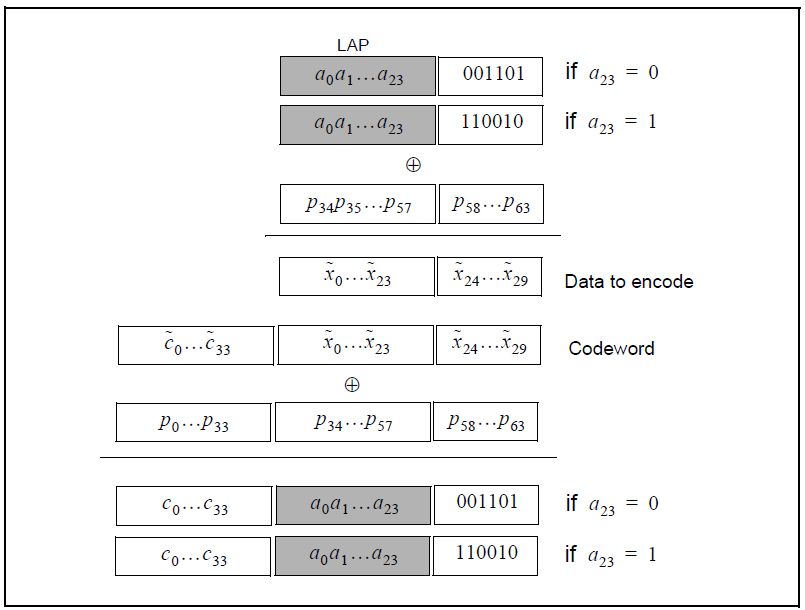
The (64,30) block code generator polynomial is denoted , where is the generator polynomial 157464165547 (octal notation) of a primitive binary (63,30) BCH code. Thus, in octal notation g(D) is
the left-most bit corresponds to the high-order (g34) coefficient. The DC-free four bit sequences 0101 and 1010 can be written
respectively. Furthermore,
which are used to create the length seven Barker sequences. Then, the access code shall be generated by the following procedure:
Format the 30 information bits to encode:
Add the information covering part of the PN overlay sequence:
Generate parity bits of the (64,30) expurgated block code:[1]
Create the codeword:
Add the PN sequence:
Append the (DC-free) preamble and trailer:
6.3.3.2. Pseudo-random noise sequence generation
To generate the PN sequence the primitive polynomial h(D) = 1 + D + D3 + D4 + D6 shall be used. The LFSR and its starting state are shown in Figure 6.6. The PN sequence generated (including the extra terminating zero) becomes (hexadecimal notation) 83848D96BBCC54FC. The LFSR output starts with the left-most bit of this PN sequence. This corresponds to of the previous section. Thus, using the reciprocal as overlay gives the 64 bit sequence:
where the left-most bit is p0 = 0 (there are two initial zeros in the binary representation of the hexadecimal digit 3), and p63 = 1 is the right-most bit.
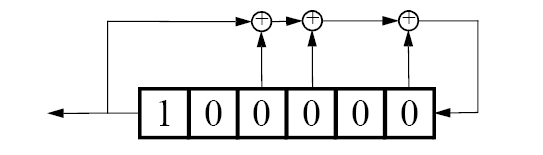
6.3.4. Trailer
The trailer is appended to the sync word as soon as the packet header follows the access code. This is typically the case with the CAC, but the trailer is also used in the DAC and IAC when these codes are used in FHS packets exchanged during page response and inquiry response.
The trailer is a fixed zero-one pattern of four symbols. The trailer together with the three MSBs of the syncword form a 7-bit pattern of alternating ones and zeroes which can be used for extended DC compensation. The trailer sequence is either ‘1010’ or ‘0101’ (in transmission order) depending on whether the MSB of the sync word is 0 or 1, respectively. The choice of trailer is illustrated in Figure 6.7.

6.4. Packet header
The header contains link control (LC) information and consists of 6 fields:
LT_ADDR: 3-bit logical transport address
TYPE: 4-bit type code
FLOW: 1-bit flow control
ARQN: 1-bit acknowledge indication
SEQN: 1-bit sequence number
HEC: 8-bit header error check
The total header, including the HEC, consists of 18 bits, see Figure 6.8, and is encoded with a rate 1/3 FEC (not shown but described in Section 7.4) resulting in a 54-bit header. The LT_ADDR and TYPE fields shall be sent LSB first.
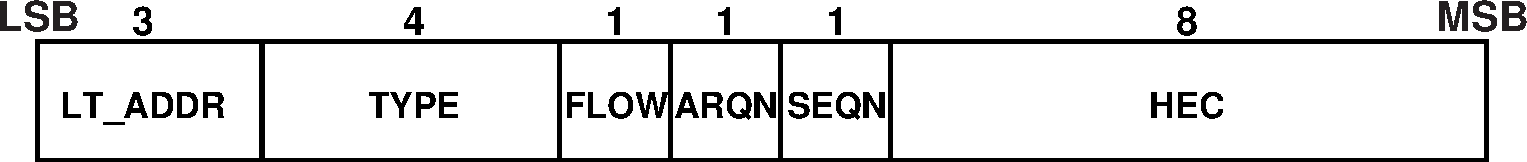
6.4.1. LT_ADDR
The 3-bit LT_ADDR field contains the logical transport address for the packet (see Section 4.2). This field indicates the destination Peripheral (or Peripherals in the case of a broadcast) for a packet in a Central-to-Peripheral transmission slot and indicates the source Peripheral for a Peripheral-to-Central transmission slot.
6.4.2. TYPE
Sixteen different types of packets can be distinguished. The 4-bit TYPE code specifies which packet type is used. The interpretation of the TYPE code depends on the logical transport address in the packet. First, it shall be determined whether the packet is sent on a SCO logical transport, an eSCO logical transport, an ACL logical transport, or a CPB logical transport. Second, it shall be determined whether Enhanced Data Rate has been enabled for the logical transport (ACL or eSCO) indicated by LT_ADDR. It can then be determined which type of SCO packet, eSCO packet, or ACL packet has been received. The TYPE code determines how many slots the current packet will occupy (see the slot occupancy column in Table 6.2). This allows the non-addressed receivers to refrain from listening to the channel for the duration of the remaining slots. In Section 6.5, each packet type is described in more detail.
6.4.3. FLOW
The FLOW bit is used for flow control of packets over the ACL logical transport. When the RX buffer for the ACL logical transport in the recipient is full, a STOP indication (FLOW=0) shall be returned to stop the other device from transmitting data temporarily. The STOP signal only affects ACL packets. Packets including only link control information (POLL and NULL packets), SCO packets or eSCO packets can still be received. When the RX buffer can accept data, a GO indication (FLOW=1) shall be returned. When no packet is received, or the received header is in error, a GO shall be assumed implicitly. In this case, the Peripheral can receive a new packet with CRC although its RX buffer is still not emptied. The Peripheral shall then return a NAK in response to this packet even if the packet passed the CRC check.
The FLOW bit is not used on the eSCO logical transport and shall be set to one on transmission and ignored upon receipt. The FLOW bit is reserved for future use on the CPB logical transport.
6.4.4. ARQN
The 1-bit acknowledgment indication ARQN is used to inform the source of a successful transfer of payload data with CRC, and can be positive acknowledge ACK or negative acknowledge NAK. See Section 7.6 for initialization and usage of this bit.
The ARQN bit is reserved for future use on the CPB logical transport.
6.4.5. SEQN
The SEQN bit provides a sequential numbering scheme to order the data packet stream. See Section 7.6.2 for initialization and usage of the SEQN bit. For Active Peripheral Broadcast packets, a modified sequencing method is used, see Section 7.6.5.
The SEQN bit is reserved for future use on the CPB logical transport.
6.4.6. HEC
Each header has a header-error-check to check the header integrity. The HEC is an 8-bit word (generation of the HEC is specified in Section 7.1.1). Before generating the HEC, the HEC generator is initialized with an 8-bit value. For FHS packets sent in Central Page Response substate, the Peripheral upper address part (UAP) shall be used. For FHS packets and extended inquiry response packets sent in Inquiry Response substate, the default check initialization (DCI, see Section 1.2.1) shall be used. In all other cases, the UAP of the Central shall be used.
After the initialization, a HEC shall be calculated for the 10 header bits. Before checking the HEC, the receiver shall initialize the HEC check circuitry with the proper 8-bit UAP (or DCI). If the HEC does not check, the entire packet shall be discarded. More information can be found in Section 7.1.
6.5. Packet types
The packets used on the piconet are related to the logical transports on which they are used. Four logical transports with distinct packet types are defined (see Section 4):
SCO logical transport
eSCO logical transport
ACL logical transport
CPB logical transport.
To indicate the different packets on a logical transport, the 4-bit TYPE code is used. The packet types are divided into four segments. The first segment is reserved for control packets. All control packets occupy a single time slot. The second segment is reserved for packets occupying a single time slot. The third segment is reserved for packets occupying three time slots. The fourth segment is reserved for packets occupying five time slots. The slot occupancy is reflected in the segmentation and can directly be derived from the type code. Table 6.2 summarizes the packets defined for the SCO, eSCO, ACL, and CPB logical transport types; a dash means the value is reserved for future use.
All packet types with a payload shall use GFSK modulation unless specified otherwise in the following sections.
ACL logical transports Enhanced Data Rate packet types are explicitly selected via LMP using the packet_type_table (ptt) parameter. eSCO Enhanced Data Rate packet types are selected when the eSCO logical transport is established. Enhanced Data Rate packet types for the CPB logical transport are selected when the CPB logical transport is established.
Segment | TYPE code b3b2b1b0 | Slot occu-pancy | SCO logical transport (1 Mb/s) | eSCO logical transport (1 Mb/s) | eSCO logical transport (2-3 Mb/s) | ACL logical transport (1 Mb/s) ptt=0 | ACL logical transport (2-3 Mb/s) ptt=1 | CPB logical transport (1 Mb/s) | CPB logical transport (2-3 Mb/s) |
|---|---|---|---|---|---|---|---|---|---|
1 | 0000 | 1 | NULL | NULL | NULL | NULL | NULL | NULL | NULL |
0001 | 1 | POLL | POLL | POLL | POLL | POLL | — | — | |
0010 | 1 | FHS | — | — | FHS | FHS | — | — | |
0011 | 1 | DM1 | — | — | DM1 | DM1 | DM1 | DM1 | |
2 | 0100 | 1 | — | — | — | DH1 | 2-DH1 | DH1 | 2-DH1 |
0101 | 1 | HV1 | — | — | — | — | — | — | |
0110 | 1 | HV2 | — | 2-EV3 | — | — | — | — | |
0111 | 1 | HV3 | EV3 | 3-EV3 | — | — | — | — | |
1000 | 1 | DV | — | — | — | 3-DH1 | — | 3-DH1 | |
1001 | 1 | — | — | — | AUX1 | AUX1 | — | — | |
3 | 1010 | 3 | — | — | — | DM3 | 2-DH3 | DM3 | 2-DH3 |
1011 | 3 | — | — | — | DH3 | 3-DH3 | DH3 | 3-DH3 | |
1100 | 3 | — | EV4 | 2-EV5 | — | — | — | — | |
1101 | 3 | — | EV5 | 3-EV5 | — | — | — | — | |
4 | 1110 | 5 | — | — | — | DM5 | 2-DH5 | DM5 | 2-DH5 |
1111 | 5 | — | — | — | DH5 | 3-DH5 | DH5 | 3-DH5 |
6.5.1. Common packet types
There are five common kinds of packets. In addition to the types listed in segment 1 of Table 6.2, the ID packet is also a common packet type but is not listed in segment 1 because it does not have a packet header.
6.5.1.1. ID packet
The identity or ID packet consists of the device access code (DAC) or inquiry access code (IAC). It has a fixed length of 68 bits. It is a very robust packet since the receiver uses a bit correlator to match the received packet to the known bit sequence of the ID packet.
The ID packet shall only be used where explicitly stated in paging (see Section 8.3), inquiry (see Section 8.4), and role switch (see Section 8.6.5). It shall not be used where any other packet type is permitted.
6.5.1.2. NULL packet
The NULL packet has no payload and consists of the channel access code and packet header only. Its total (fixed) length is 126 bits. The NULL packet may be used to return link information to the source regarding the success of the previous transmission (ARQN), or the status of the RX buffer (FLOW). The NULL packet does not require acknowledgment.
6.5.1.3. POLL packet
The POLL packet is very similar to the NULL packet. It does not have a payload. In contrast to the NULL packet, it requires a confirmation from the recipient. It is not a part of the ARQ scheme. The POLL packet does not affect the ARQN and SEQN fields. Upon reception of a POLL packet the Peripheral shall respond with a packet even when the Peripheral does not have any information to send unless the Peripheral has scatternet commitments in that timeslot. This return packet is an implicit acknowledgment of the POLL packet. This packet can be used by the Central in a piconet to poll the Peripherals. Peripherals shall not transmit the POLL packet. POLL packets shall not be sent on a Connectionless Peripheral Broadcast logical transport.
6.5.1.4. FHS packet
The FHS packet is a special control packet containing, among other things, the Bluetooth Device Address and the clock of the sender. The payload contains 144 information bits plus a 16-bit CRC code. The payload is coded with a rate 2/3 FEC with a gross payload length of 240 bits.
Figure 6.9 illustrates the format and contents of the FHS payload. The FHS packet is used in Central page response, inquiry response and in role switch.
The FHS packet is not encrypted. No payload header or MIC is present.
The FHS packet contains real-time clock information. This clock information shall be updated before each retransmission. The retransmission of the FHS payload is different than retransmissions of ordinary data payloads where the same payload is used for each retransmission. The FHS packet is used for frequency hop synchronization before the piconet channel has been established, or when an existing piconet changes to a new piconet. However, the FHS packet is not used by Connectionless Peripheral Broadcast Receivers for frequency hop synchronization with Connectionless Peripheral Broadcast Transmitters.

Each field is described in more detail below:
Parity bits | This 34-bit field contains the parity bits that form the first part of the sync word of the access code of the device that sends the FHS packet. These bits are derived from the LAP as described in Section 1.2. |
LAP | This 24-bit field shall contain the lower address part of the device that sends the FHS packet. |
EIR | This bit shall indicate that an extended inquiry response packet may follow. See Section 8.4.3. |
Reserved | This 1-bit field is reserved for future use. |
SR | This 2-bit field is the page scan repetition mode field and indicates the interval between two consecutive page scan windows, see also Table 6.4 and Table 8.1 |
SP | This 2-bit field shall be set to 0b10. |
UAP | This 8-bit field shall contain the upper address part of the device that sends the FHS packet. |
NAP | This 16-bit field shall contain the non-significant address part of the device that sends the FHS packet (see also Section 1.2 for LAP, UAP, and NAP). |
Class of Device | This 24-bit field shall contain the Class of Device of the device that sends the FHS packet. The field is defined in Assigned Numbers. |
LT_ADDR | This 3-bit field shall contain the logical transport address the recipient shall use if the FHS packet is used at connection setup or role switch. A Peripheral responding to a Central or a device responding to an inquiry request message shall include an all-zero LT_ADDR field if it sends the FHS packet. |
CLK27-2 | This 26-bit field shall contain the value of the native clock of the device that sends the FHS packet, sampled at the beginning of the transmission of the access code of this FHS packet. This clock value has a resolution of 1.25 ms (two-slot interval). For each new transmission, this field is updated so that it accurately reflects the real-time clock value. |
The device sending the FHS shall set the SR bits according to Table 6.4.
SR bit format b1b0 | SR (page scan repetition) mode |
|---|---|
00 | R0 |
01 | R1 |
10 | R2 |
11 | Reserved for future use |
The LAP, UAP, and NAP together form the 48-bit Bluetooth Device Address of the device that sends the FHS packet. Using the parity bits and the LAP, the recipient can directly construct the channel access code of the sender of the FHS packet.
When initializing the HEC and CRC for the FHS packet of inquiry response, the UAP shall be the DCI.
6.5.1.5. DM1 packet
DM1 is part of segment 1 in order to support control messages in any logical transport that allows the DM1 packet (see Table 6.2). However, it may also carry regular user data. Since the DM1 packet can be regarded as an ACL packet, it will be discussed in Section 6.5.4.
6.5.2. SCO packets
HV and DV packets are used on the synchronous SCO logical transport. The HV packets do not include a MIC or CRC and shall not be retransmitted. DV packets include a CRC on the data section, but not on the synchronous data section. DV packets do not include a MIC. The data section of DV packets shall be retransmitted. SCO packets may be routed to the synchronous I/O port. Four packets are allowed on the SCO logical transport: HV1, HV2, HV3 and DV. These packets are typically used for 64 kb/s speech transmission but may be used for transparent synchronous data.
SCO packets shall only be encrypted with E0 when E0 is enabled. SCO packets shall not be sent when AES-CCM Encryption is enabled.
6.5.2.1. HV1 packet
The HV1 packet has 10 information bytes. The bytes are protected with a rate 1/3 FEC. No MIC is present. No CRC is present. The payload length is fixed at 240 bits. There is no payload header present.
6.5.2.2. HV2 packet
The HV2 packet has 20 information bytes. The bytes are protected with a rate 2/3 FEC. No MIC is present. No CRC is present. The payload length is fixed at 240 bits. There is no payload header present.
6.5.2.3. HV3 packet
The HV3 packet has 30 information bytes. The bytes are not protected by FEC. No MIC is present. No CRC is present. The payload length is fixed at 240 bits. There is no payload header present.
6.5.2.4. DV packet
The DV packet is a combined data - voice packet. The DV packet shall only be used in place of an HV1 packet. The payload is divided into a voice field of 80 bits and a data field containing up to 150 bits, see Figure 6.10. The voice field is not protected by FEC. The data field has between 1 and 10 information bytes (including the 1-byte payload header) plus a 16-bit CRC code. No MIC is present. The data field (including the CRC) is encoded with a rate 2/3 FEC. Since the DV packet has to be sent at regular intervals due to its synchronous contents, it is listed under the SCO packet types. The voice and data fields shall be treated separately. The voice field shall be handled in the same way as normal SCO data and shall never be retransmitted; that is, the voice field is always new. The data field is checked for errors and shall be retransmitted if necessary. When the asynchronous data field in the DV packet has not been acknowledged before the SCO logical transport is terminated, the asynchronous data field shall be retransmitted in a DM1 packet.
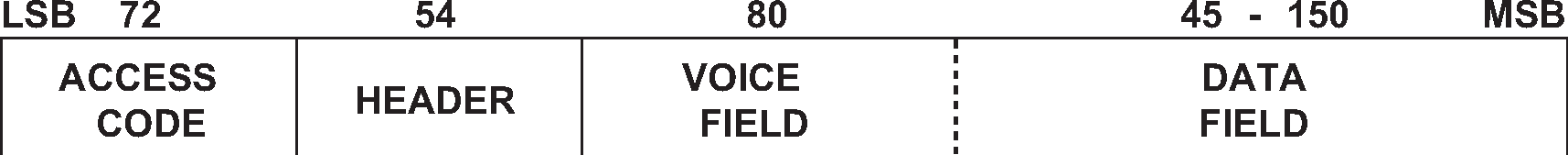
6.5.3. eSCO packets
EV packets are used on the synchronous eSCO logical transport. The packets include a CRC and retransmission may be applied if no acknowledgment of proper reception is received within the retransmission window. No MIC is present. eSCO packets may be routed to the synchronous I/O port. Three eSCO packet types (EV3, EV4, EV5) are defined for Basic Rate operation and four additional eSCO packet types (2-EV3, 3-EV3, 2-EV5, 3-EV5) for Enhanced Data Rate operation. The eSCO packets may be used for 64 kb/s speech transmission as well as transparent data at 64 kb/s and other rates.
6.5.3.1. EV3 packet
The EV3 packet has between 1 and 30 information bytes plus a 16-bit CRC code. No MIC is present. The bytes are not protected by FEC. The EV3 packet may cover up to a single time slot. There is no payload header present. The payload length is set during the LMP eSCO setup and remains fixed until the link is removed or re-negotiated.
6.5.3.2. EV4 packet
The EV4 packet has between 1 and 120 information bytes plus a 16-bit CRC code. No MIC is present. The EV4 packet may cover to up three time slots. The information plus CRC bits are coded with a rate 2/3 FEC. There is no payload header present. The payload length is set during the LMP eSCO setup and remains fixed until the link is removed or re-negotiated.
6.5.3.3. EV5 packet
The EV5 packet has between 1 and 180 information bytes plus a 16-bit CRC code. No MIC is present. The bytes are not protected by FEC. The EV5 packet may cover up to three time slots. There is no payload header present. The payload length is set during the LMP eSCO setup and remains fixed until the link is removed or re-negotiated.
6.5.3.4. 2-EV3 packet
The 2-EV3 packet is similar to the EV3 packet except that the payload is modulated using π/4-DQPSK. It has between 1 and 60 information bytes plus a 16-bit CRC code. No MIC is present. The bytes are not protected by FEC. The 2-EV3 packet covers a single time slot. There is no payload header present. The payload length is set during the LMP eSCO setup and remains fixed until the link is removed or re-negotiated.
6.5.3.5. 2-EV5 packet
The 2-EV5 packet is similar to the EV5 packet except that the payload is modulated using π/4-DQPSK. It has between 1 and 360 information bytes plus a 16-bit CRC code. No MIC is present. The bytes are not protected by FEC. The 2-EV5 packet may cover up to three time slots. There is no payload header present. The payload length is set during the LMP eSCO setup and remains fixed until the link is removed or re-negotiated.
6.5.3.6. 3-EV3 packet
The 3-EV3 packet is similar to the EV3 packet except that the payload is modulated using 8DPSK. It has between 1 and 90 information bytes plus a 16-bit CRC code. No MIC is present. The bytes are not protected by FEC. The 3-EV3 packet covers a single time slot. There is no payload header present. The payload length is set during the LMP eSCO setup and remains fixed until the link is removed or re-negotiated.
6.5.3.7. 3-EV5 packet
The 3-EV5 packet is similar to the EV5 packet except that the payload is modulated using 8DPSK. It has between 1 and 540 information bytes plus a 16-bit CRC code. No MIC is present. The bytes are not protected by FEC. The 3-EV5 packet may cover up to three time slots. There is no payload header present. The payload length is set during the LMP eSCO setup and remains fixed until the link is removed or re-negotiated.
6.5.4. ACL packets
ACL packets are used on the asynchronous logical transport and the CPB logical transport. The information carried may be user data for either logical transport or control data for the asynchronous logical transport.
Six packet types are defined for Basic Rate operation: DM1, DH1, DM3, DH3, DM5, and DH5. Six additional packets are defined for Enhanced Data Rate operation: 2-DH1, 3-DH1, 2-DH3, 3-DH3, 2-DH5 and 3-DH5. The AUX1 packet is also defined for test purposes.
The length indicator in the payload header specifies the number of user bytes (excluding payload header, MIC and the CRC code).
6.5.4.1. DM1 packet
The DM1 packet carries data information only. The payload has between 1 and 18 information bytes (including the 1-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The DM1 packet occupies a single time slot. The information bits, MIC bits (when present), plus CRC bits are coded with a rate 2/3 FEC. The payload header in the DM1 packet is 1 byte long, see Figure 6.12.
6.5.4.2. DH1 packet
This packet is similar to the DM1 packet, except that the information in the payload is not FEC encoded. As a result, the DH1 packet has between 1 and 28 information bytes (including the 1-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The DH1 packet occupies a single time slot.
6.5.4.3. DM3 packet
The DM3 packet may occupy up to three time slots. The payload has between 2 and 123 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The information bits, MIC bits (when present), plus CRC bits are coded with a rate 2/3 FEC. The payload header in the DM3 packet is 2 bytes long, see Figure 6.13.
6.5.4.4. DH3 packet
This packet is similar to the DM3 packet, except that the information in the payload is not FEC encoded. As a result, the DH3 packet has between 2 and 185 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The DH3 packet may occupy up to three time slots.
6.5.4.5. DM5 packet
The DM5 packet may occupy up to five time slots. The payload has between 2 and 226 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The payload header in the DM5 packet is 2 bytes long. The information bits, MIC bits (when present), plus CRC bits are coded with a rate 2/3 FEC.
6.5.4.6. DH5 packet
This packet is similar to the DM5 packet, except that the information in the payload is not FEC encoded. As a result, the DH5 packet has between 2 and 341 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The DH5 packet may occupy up to five time slots.
6.5.4.7. AUX1 packet
This packet resembles a DH1 packet but has no MIC or CRC code. The AUX1 packet has between 1 and 30 information bytes (including the 1-byte payload header). The AUX1 packet occupies a single time slot. The AUX1 packet shall only be used in test mode (see [Vol 3] Part D). The Link Controller shall discard any AUX1 packet received in any other circumstances.
6.5.4.8. 2-DH1 packet
This packet is similar to the DH1 packet except that the payload is modulated using π/4-DQPSK. The 2-DH1 packet has between 2 and 56 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled.The 2-DH1 packet occupies a single time slot.
6.5.4.9. 2-DH3 packet
This packet is similar to the DH3 packet except that the payload is modulated using π/4-DQPSK. The 2-DH3 packet has between 2 and 369 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The 2-DH3 packet may occupy up to three time slots.
6.5.4.10. 2-DH5 packet
This packet is similar to the DH5 packet except that the payload is modulated using π/4-DQPSK. The 2-DH5 packet has between 2 and 681 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The 2-DH5 packet may occupy up to five time slots.
6.5.4.11. 3-DH1 packet
This packet is similar to the DH1 packet except that the payload is modulated using 8DPSK. The 3-DH1 packet has between 2 and 85 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The 3-DH1 packet occupies a single time slot.
6.5.4.12. 3-DH3 packet
This packet is similar to the DH3 packet except that the payload is modulated using 8DPSK. The 3-DH3 packet has between 2 and 554 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The 3-DH3 packet may occupy up to three time slots.
6.5.4.13. 3-DH5 packet
This packet is similar to the DH5 packet except that the payload is modulated using 8DPSK. The 3-DH5 packet has between 2 and 1023 information bytes (including the 2-byte payload header) plus a 16-bit CRC code. A 32-bit MIC is present only when encryption with AES-CCM is enabled. The 3-DH5 packet may occupy up to five time slots.
6.6. Payload format
In the payload, two fields are distinguished: the synchronous data field and the asynchronous data field. The ACL packets only have the asynchronous data field and the SCO and eSCO packets only have the synchronous data field – with the exception of the DV packets which have both.
6.6.1. Synchronous data field
In SCO, which is only supported in Basic Rate mode, the synchronous data field has a fixed length and consists only of the synchronous data body portion. No payload header is present.
In Basic Rate eSCO, the synchronous data field consists of two segments: a synchronous data body and a CRC code. No payload header is present.
In Enhanced Data Rate eSCO, the synchronous data field consists of five segments: a guard time, a synchronization sequence, a synchronous data body, a CRC code and a trailer. No payload header is present.
Enhanced Data Rate guard time
For Enhanced Data Rate packets the guard time is defined as the period starting at the end of the last GFSK symbol of the header and ending at the start of the reference symbol of the synchronization sequence. The length of the guard time shall be between 4.75 µs and 5.25 µs.
Enhanced Data Rate synchronization sequence
For Enhanced Data Rate packets the symbol timing at the start of the synchronization sequence shall be within ±¼ µs of the symbol timing of the last GFSK symbol of the packet header. The length of the synchronization sequence is 11 µs (11 DPSK symbols) and consists of a reference symbol (with arbitrary phase) followed by ten DPSK symbols.
The phase changes between the DPSK symbols (shown in Figure 6.11) shall be
Equation 13. Figure 6.11: Synchronization sequence
Figure 6.11: Synchronization sequenceSref is the reference symbol. 1 is the phase change between the reference symbol and the first DPSK symbol S1. k is the phase change between the k-1th symbol Sk-1 and the kth symbol Sk
Note
Note: The synchronization sequence may be generated using the modulator by pre-pending the data with bits that generate the synchronization sequence.
For π/4-DQPSK, the bit sequence used to generate the synchronization sequence is 0,1,1,1,0,1,1,1,0,1,1,1,1,1,0,1,0,1,0,1.
For 8DPSK, the bit sequence used to generate the synchronization sequence is 0,1,0,1,1,1,0,1,0,1,1,1,0,1,0,1,1,1,1,1,1,0,1,0,0,1,0,0,1,0.
Synchronous data body
For HV and DV packets, the synchronous data body length is fixed. For EV packets, the synchronous data body length is negotiated during the LMP eSCO setup. Once negotiated, the synchronous data body length remains constant unless re-negotiated. The synchronous data body length may be different for each direction of the eSCO logical transport.
CRC code
The 16-bit CRC in the payload is generated as specified in Section 7.1. The 8-bit UAP of the Central is used to initialize the CRC generator.
Only the Synchronous data body segment is used to generate the CRC code.
Enhanced Data Rate trailer
For Enhanced Data Rate packets, two trailer symbols shall be added to the end of the payload. The trailer bits shall be all zero, i.e. {00, 00} for the π/4-DQPSK and {000, 000} for the 8DPSK.
6.6.2. Asynchronous data field
Basic rate ACL packets have an asynchronous data field consisting of two, three or four segments: a payload header, a payload body, possibly a MIC, and possibly a CRC code.
Enhanced Data Rate ACL packets have an asynchronous data field consisting of six or seven segments: a guard time, a synchronization sequence, a payload header, a payload body, possibly a MIC, a CRC and a trailer.
Enhanced Data Rate guard time
This is the same as defined for the Synchronous data field in Section 6.6.1.
Enhanced Data Rate synchronization sequence
This is the same as defined for the Synchronous data field in Section 6.6.1.
Payload header
The payload header is one or two bytes long. Basic rate packets in segments one and two have a 1-byte payload header; Basic Rate packets in segments three and four and all Enhanced Data Rate packets have a 2-byte payload header. The payload header specifies the logical link (2-bit LLID indication), controls the flow on the logical channels (1-bit FLOW indication), and has a payload length indicator (5 bits and 10 bits for 1-byte and 2-byte payload headers, respectively). In the case of a 2-byte payload header, the length indicator is extended by five bits into the next byte. The remaining three bits of the second byte are reserved for future use. The formats of the 1-byte and 2-byte payload headers are shown in Figure 6.12 and Figure 6.13.
 Figure 6.12: Payload header format for Basic Rate single-slot ACL packets
Figure 6.12: Payload header format for Basic Rate single-slot ACL packets Figure 6.13: Payload header format for multi-slot ACL packets and all EDR ACL packets
Figure 6.13: Payload header format for multi-slot ACL packets and all EDR ACL packetsThe LLID field shall be transmitted first, the length field last. In Table 6.5, more details about the contents of the LLID field are listed.
LLID
Logical Link
Information
0b00
Reserved for future use
0b01
ACL‑U and APB‑U
Continuation fragment of an L2CAP message
0b10
ACL‑U and APB‑U
Start of an L2CAP message or no fragmentation
PBD
Profile broadcast data, no fragmentation
0b11
ACL‑C and APB‑C
LMP message
Table 6.5: Logical Link LLID field contentsAn L2CAP message may be fragmented into several packets. Code 0b10 shall be used for an ACL-U or APB-U packet carrying the first fragment of such a message; code 0b01 shall be used for continuing fragments. The first fragment of an L2CAP message sent over HCI is identified by having a Packet_Boundary_Flag value of 0b00 or 0b10 both of which are mapped to LLID code 0b10. If there is no fragmentation, code 0b10 shall be used for every packet. ACL packets used over the PBD logical link do not use fragmentation. For ACL packets used over the PBD logical link, LLID code 0b10 shall be used by the transmitter. Any ACL packet used over the PBD logical link with LLID not equal to 0b10 shall be ignored by the receiver. Code 0b11 shall be used for LMP messages. Code 0b00 is reserved for future use.
The flow indicator in the payload is used to control the flow at the L2CAP level. It is used to control the flow per logical link. FLOW=1 means flow-on (GO) and FLOW=0 means flow-off (STOP). After a new connection has been established the flow indicator shall be set to GO. When a device receives a payload header with the flow bit set to STOP, it shall stop the transmission of ACL-U packets before an additional amount of payload data is sent. This amount is defined as the flow control lag, expressed as a number of bytes. The shorter the flow control lag, the less buffering the other device must dedicate to this function. The flow control lag shall not exceed 1792 bytes (7 × 256 bytes). In order to allow devices to optimize the selection of packet length and buffer space, the flow control lag of a given implementation shall be provided in the LMP_FEATURES_RES message.
If a packet containing the payload flow bit of STOP is received, with a valid packet header but bad payload, the payload flow control bit shall be ignored. The Baseband acknowledgment contained in the packet header will be received and a further ACL packet may be transmitted. Each occurrence of this situation allows a further ACL packet to be sent in spite of the flow control request being sent via the payload header flow control bit. It is recommended that devices that use the payload header flow bit should ensure that no further ACL packets are sent until the payload flow bit has been correctly received. This can be accomplished by simultaneously turning on the flow bit in the packet header and keeping it on until an ACK is received back (ARQN=1). This will typically be only one round trip time.
The Baseband Resource Manager is responsible for setting and processing the flow bit in the payload header. Real-time flow control shall be carried out at the packet level by the Link Controller via the flow bit in the packet header (see Section 6.4.3). With the payload flow bit, traffic from the remote end can be controlled. It is allowed to generate and send an ACL packet with payload length zero irrespective of flow status. L2CAP start-fragment and continue-fragment indications (LLID=10 and LLID=01) also retain their meaning when the payload length is equal to zero (i.e. an empty start-fragment shall not be sent in the middle of an on-going ACL-U or APB-U packet transmission). It is always allowed to send an ACL packet with length=0 and LLID=01. The payload flow bit has its own meaning for each logical link, see Table 6.6. On the ACL-C, APB-C, and APB-U logical links, no flow control is applied and the payload FLOW bit shall always be set to one. On the PBD logical link, no flow control is applied and the payload FLOW bit shall always be set to zero.
LLID code
b1b0
Logical Link
Usage and semantics of the ACL payload header FLOW bit
00
Reserved for future use.
01
ACL-U
Flow control of the ACL-U channel (L2CAP messages).
APB-U
Always set FLOW=1 on transmission and ignore the bit on reception.
PBD
Reserved for future use.
10
ACL-U
Flow control of the ACL-U channel (L2CAP messages).
APB-U
Always set FLOW=1 on transmission and ignore the bit on reception.
PBD
Always set FLOW=0 on transmission and ignore the bit on reception.
11
ACL-C and APB-C
Always set FLOW=1 on transmission and ignore the bit on reception.
Table 6.6: Use of payload header flow bit on the Logical LinksThe length indicator shall be set to the number of bytes (i.e. 8-bit words) in the payload excluding the payload header, MIC, and the CRC code; i.e. the payload body only. With reference to Figure 6.12 and Figure 6.13, the MSB of the length field in a 1-byte header is the last (right-most) bit in the payload header; the MSB of the length field in a 2-byte header is the fourth bit to the left from the right-most end of the second byte in the payload header.
Payload body
The payload body includes the user information and determines the effective user throughput. The length of the payload body is indicated in the length field of the payload header.
Message Integrity Check
The 32-bit Message Integrity Check (MIC) in the payload is generated as specified in [Vol 2] Part H, Section 9.2.
CRC code generation
The 16-bit cyclic redundancy check code in the payload is generated as specified in Section 7.1. Before determining the CRC code, an 8-bit value is used to initialize the CRC generator. For the CRC code in the FHS packets sent in Central Page Response substate, the UAP of the Peripheral is used. For the FHS packet and the extended inquiry response packet sent in Inquiry Response substate, the DCI (see Section 1.2.1) is used. For all other packets, the UAP of the Central is used.
Only the Payload header, Payload body, and MIC segments (if present) are used to generate the CRC code.
Enhanced Data Rate trailer
This is the same as defined for the Synchronous data field in Section 6.6.1.
6.7. Packet summary
A summary of the packets and their characteristics is shown in Table 6.7, Table 6.8, and Table 6.9. The payload represents the packet payload excluding FEC, CRC, and payload header.
Type | Payload (bytes) | FEC | MIC | CRC | Symmetric Max. Rate | Asymmetric Max. Rate |
|---|---|---|---|---|---|---|
ID | N/A | N/A | N/A | N/A | N/A | N/A |
NULL | N/A | N/A | N/A | N/A | N/A | N/A |
POLL | N/A | N/A | N/A | N/A | N/A | N/A |
FHS | 18 | 2/3 | N/A | Yes | N/A | N/A |
Type | Payload Header (bytes) | User Payload (bytes) | FEC | MIC | CRC | Symmetric Max. Rate (kb/s) | Asymmetric Max. Rate (kb/s) | |
|---|---|---|---|---|---|---|---|---|
Forward | Reverse | |||||||
DM1 | 1 | 0-17 | 2/3 | C.1 | Yes | 108.8 | 108.8 | 108.8 |
DH1 | 1 | 0-27 | No | C.1 | Yes | 172.8 | 172.8 | 172.8 |
DM3 | 2 | 0-121 | 2/3 | C.1 | Yes | 258.1 | 387.2 | 54.4 |
DH3 | 2 | 0-183 | No | C.1 | Yes | 390.4 | 585.6 | 86.4 |
DM5 | 2 | 0-224 | 2/3 | C.1 | Yes | 286.7 | 477.8 | 36.3 |
DH5 | 2 | 0-339 | No | C.1 | Yes | 433.9 | 723.2 | 57.6 |
2-DH1 | 2 | 0-54 | No | C.1 | Yes | 345.6 | 345.6 | 345.6 |
2-DH3 | 2 | 0-367 | No | C.1 | Yes | 782.9 | 1174.4 | 172.8 |
2-DH5 | 2 | 0-679 | No | C.1 | Yes | 869.1 | 1448.5 | 115.2 |
3-DH1 | 2 | 0-83 | No | C.1 | Yes | 531.2 | 531.2 | 531.2 |
3-DH3 | 2 | 0-552 | No | C.1 | Yes | 1177.6 | 1766.4 | 265.6 |
3-DH5 | 2 | 0-1021 | No | C.1 | Yes | 1306.9 | 2178.1 | 177.1 |
- C.1:
Mandatory when encryption with AES-CCM enabled, else excluded
Type | Payload Header (bytes) | User Payload (bytes) | FEC | MIC | CRC | Symmetric Max. Rate (kb/s) | |||||||||||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
HV1 | N/A | 10 | 1/3 | No | No | 64.0 | |||||||||||||||||||||||||||||||||||||||||||
HV2 | N/A | 20 | 2/3 | No | No | 64.0 | |||||||||||||||||||||||||||||||||||||||||||
HV3 | N/A | 30 | no | No | No | 64.0 | |||||||||||||||||||||||||||||||||||||||||||
DV[1] | 1 D | 10+(0-9) D | 2/3 D | No | Yes D | 64.0+57.6 D | |||||||||||||||||||||||||||||||||||||||||||
EV3 | N/A | 1-30 | No | No | Yes | 96 | |||||||||||||||||||||||||||||||||||||||||||
EV4 | N/A | 1-120 | 2/3 | No | Yes | 192 | |||||||||||||||||||||||||||||||||||||||||||
EV5 | N/A | 1-180 | No | No | Yes | 288 | |||||||||||||||||||||||||||||||||||||||||||
2-EV3 | N/A | 1-60 | No | No | Yes | 192 | |||||||||||||||||||||||||||||||||||||||||||
2-EV5 | N/A | 1-360 | No | No | Yes | 576 | |||||||||||||||||||||||||||||||||||||||||||
3-EV3 | N/A | 1-90 | No | No | Yes | 288 | |||||||||||||||||||||||||||||||||||||||||||
3-EV5 | N/A | 1-540 | No | No | Yes | 864 | |||||||||||||||||||||||||||||||||||||||||||
[1] Items followed by ‘D’ relate to data field only. | |||||||||||||||||||||||||||||||||||||||||||||||||
7. Bit stream processing
Bluetooth devices shall use the bit stream processing schemes as defined in the following sections.
Before the payload is sent over the air interface, several bit manipulations are performed in the transmitter to increase reliability and security. An HEC is added to the packet header, the header bits are scrambled with a whitening word, and FEC coding is applied. In the receiver, the inverse processes are carried out. Figure 7.1 shows the processes carried out for the packet header both at the transmit and the receive side. All header bit processes are mandatory except that whitening and de-whitening shall not be performed on synchronization train packets. In Figure 7.1 processes not performed on all packet types are indicated by dashed blocks.

Figure 7.2 shows the processes that may be carried out on the payload. In addition to the processes defined for the packet header, encryption can be applied on the payload. Whitening and de-whitening, as explained in Section 7.2, are mandatory for every payload except synchronization train payloads, where they are forbidden.All other processes are optional and depend on the packet type (see Section 6.6) and whether encryption is enabled. In Figure 7.2, optional processes are indicated by dashed blocks. When E0 encryption is used, the entire payload shall be encrypted. When AES-CCM encryption is used, only the payload body and MIC shall be encrypted; the payload header and CRC shall not be encrypted..

7.1. Error checking
The packet can be checked for errors or wrong delivery using the channel access code, the HEC in the header, and the CRC in the payload. At packet reception, the access code is checked first. Since the 64-bit sync word in the channel access code is derived from the 24-bit Central’s LAP, this checks if the LAP is correct, and prevents the receiver from accepting a packet of another piconet (provided the LAP field of the Central's BD_ADDR is different).
The HEC and CRC computations are initialized as follows:
In the Inquiry Response substate, the DCI value shall be used for the FHS and Extended Inquiry Response packet.
In the Central Page Response substate, the UAP of the Peripheral shall be used in the FHS packet.
In the Connection state, the UAP of the Central shall be used. Even though the access code may be the same for two piconets the different UAP values will typically cause the HEC and CRC to fail.
During Role Switch starting from the TDD switch, the UAP of the new Peripheral shall be used for the FHS packet.
The generation and check of the HEC and CRC are summarized in Figure 7.5 and Figure 7.8. Before calculating the HEC or CRC, the shift registers in the HEC/CRC generators shall be initialized with the 8-bit UAP (or DCI) value. Then the header and payload information shall be shifted into the HEC and CRC generators, respectively (with the LSB first).
A packet has a valid header if the access code is correct for the piconet and the HEC has the correct value, irrespective of the values of the other header fields.
7.1.1. HEC generation
The HEC generating LFSR is depicted in Figure 7.3. The generator polynomial is g(D) = (D + 1)(D7 + D4 + D3 + D2 + 1) = D8 + D7 + D5 + D2 + D + 1. Initially this circuit shall be pre-loaded with the 8-bit UAP such that the LSB of the UAP (denoted UAP0) goes to the left-most shift register element, and, UAP7 goes to the right-most element. The initial state of the HEC LFSR is depicted in Figure 7.4. Then the data shall be shifted in with the switch S set in position 1. When the last data bit has been clocked into the LFSR, the switch S shall be set in position 2, and, the HEC can be read out from the register. The LFSR bits shall be read out from right to left (i.e., the bit in position 7 is the first to be transmitted, followed by the bit in position 6, etc.).
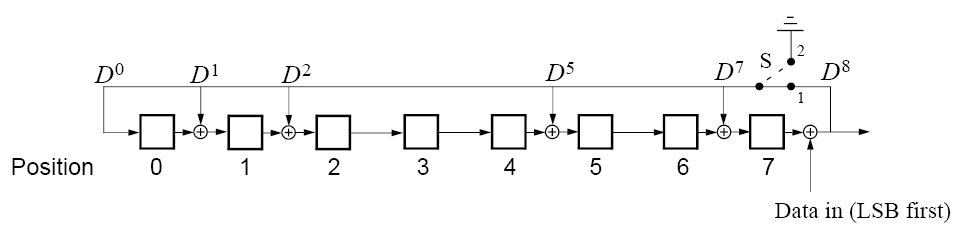
 |
 |
7.1.2. CRC generation
The 16 bit LFSR for the CRC is constructed similarly to the HEC using the CRC-CCITT generator polynomial g(D) = D16 + D12 + D5 + 1 (i.e. 210041 in octal representation) (see Figure 7.6). For this case, the 8 left-most bits shall be initially loaded with the 8-bit UAP (UAP0 to the left and UAP7 to the right) while the 8 right-most bits shall be reset to zero. The initial state of the 16 bit LFSR is specified in Figure 7.7. The switch S shall be set in position 1 while the data is shifted in. After the last bit has entered the LFSR, the switch shall be set in position 2, and, the register’s contents shall be transmitted, from right to left (i.e., starting with position 15, then position 14, etc.).
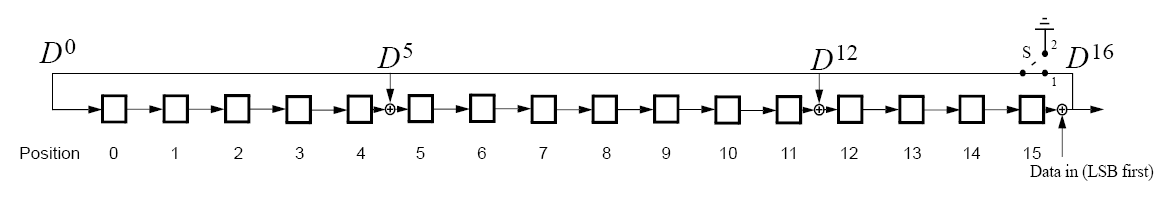
 |
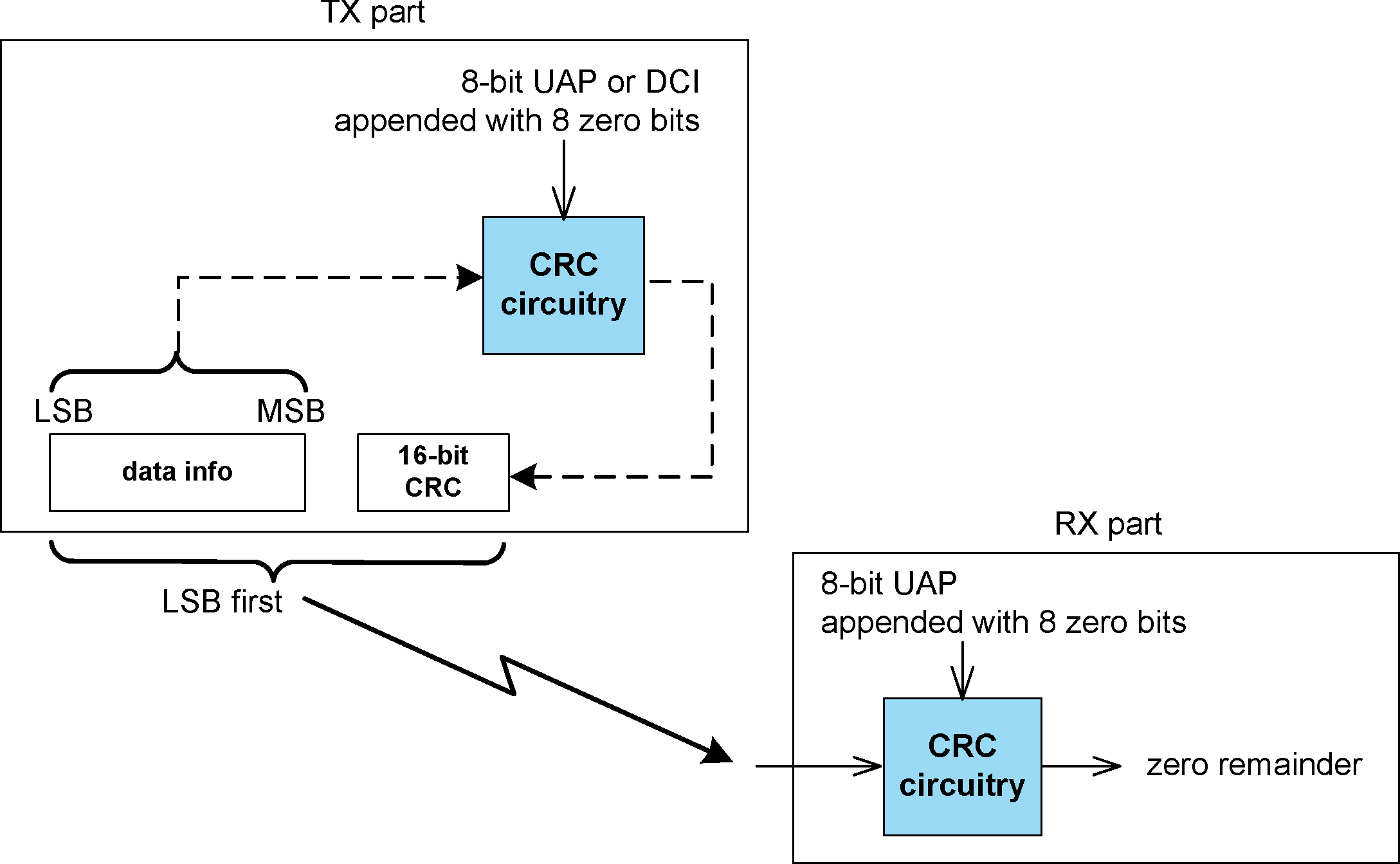 |
7.2. Data whitening
Before transmission of all packets both the header and the payload shall be scrambled with a data whitening word in order to randomize the data from highly redundant patterns and to minimize DC bias in the packet. The scrambling shall be performed prior to the FEC encoding. As an exception, Synchronization train packets shall not be scrambled with a data whitening word.
At the receiver, the received data of scrambled packets shall be descrambled using the same whitening word generated in the recipient. The descrambling shall be performed after FEC decoding.
The whitening word is generated with the polynomial g(D) = D7 + D4 + 1 (i.e., 221 in octal representation) and shall be subsequently XORed with the header and the payload. The whitening word is generated with the linear feedback shift register shown in Figure 7.9. Before each transmission, the shift register shall be initialized with a portion of the Central's clock, CLK6-1, extended with an MSB of value one. This initialization shall be carried out with CLK1 written to position 0, CLK2 written to position 1, etc. Exceptions are the FHS packet sent during inquiry response or Central page response, and the extended inquiry response packet sent during inquiry response, where initialization of the whitening register shall be carried out differently. Instead of the Central's clock, the X-input used in the inquiry or page response (depending on current state) routine shall be used, see Table 2.2. The 5-bit value shall be extended with two MSBs of value 1. During register initialization, the LSB of X (i.e., X0) shall be written to position 0, X1 shall be written to position 1, etc.
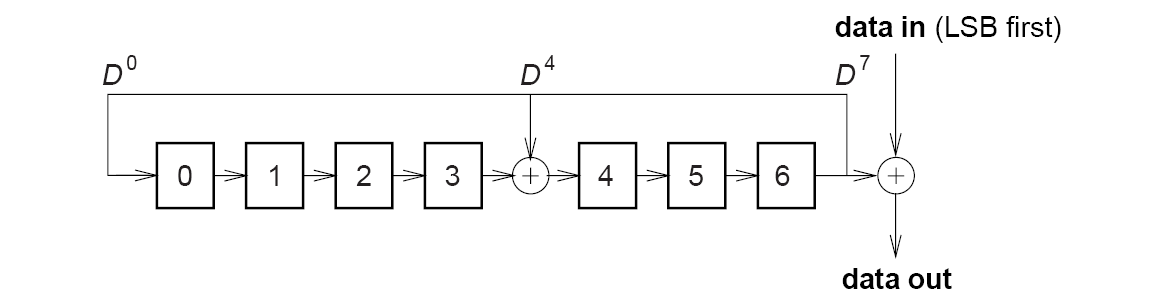
After initialization, the packet header and the payload (including the CRC) are whitened. The payload whitening shall continue from the state the whitening LFSR had at the end of HEC. There shall be no re-initialization of the shift register between packet header and payload. The first bit of the “data in” sequence shall be the LSB of the packet header.
For Enhanced Data Rate packets, whitening shall not be applied to the guard, synchronization and trailer portions of the Enhanced Data Rate packets. During the periods where whitening is not applied the LFSR shall be paused.
7.3. Error correction
There are three error correction schemes defined for Bluetooth:
1/3 rate FEC
2/3 rate FEC
ARQ scheme for the data
The purpose of the FEC scheme on the data payload is to reduce the number of retransmissions. However, in a reasonably error-free environment, FEC gives unnecessary overhead that reduces the throughput. Therefore, the packet definitions given in Section 6 have been kept flexible to use FEC in the payload or not, resulting in the DM and DH packets for the ACL logical transport, HV packets for the SCO logical transport, and EV packets for the eSCO logical transport. The packet header is always protected by a 1/3 rate FEC since it contains valuable link information and is designed to withstand more bit errors.
Correction measures to mask errors in the voice decoder are not included in this section. This matter is discussed in Section 9.3.
7.4. FEC code: rate 1/3
A simple 3-times repetition FEC code is used for the header. The repetition code is implemented by repeating each bit three times, see the illustration in Figure 7.10. The 3-times repetition code is used for the entire header, as well as for the synchronous data field in the HV1 packet.
7.5. FEC code: rate 2/3
The other FEC scheme is a (15,10) shortened Hamming code. The generator polynomial is g(D) = (D + 1)(D4 + D +1) . This corresponds to 65 in octal notation. The LFSR generating this code is depicted in Figure 7.11. Initially all register elements are set to zero. The 10 information bits are sequentially fed into the LFSR with the switches S1 and S2 set in position 1. Then, after the final input bit, the switches S1 and S2 are set in position 2, and the five parity bits are shifted out. The parity bits are appended to the information bits. Subsequently, each block of 10 information bits is encoded into a 15 bit codeword. This code can correct all single errors and detect all double errors in each codeword. This 2/3 rate FEC is used in the DM packets, in the data field of the DV packet, in the FHS packet, in the HV2 packet, and in the EV4 packet. Since the encoder operates with information segments of length 10, tail bits with value zero shall be appended after the CRC bits to bring the total number of bits equal to a multiple of 10. The number of tail bits to append shall be the least possible that achieves this (i.e., in the interval 0...9). These tail bits are not included in the payload length indicator for ACL packets or in the payload length field of the eSCO setup LMP command.
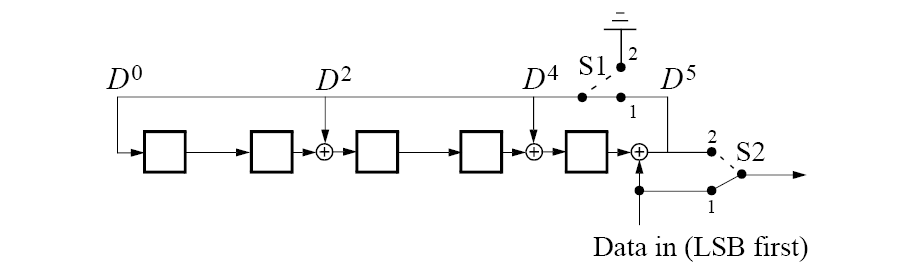
7.6. ARQ scheme
With an automatic repeat request scheme, DM packets, DH packets, the data field of DV packets, and EV packets shall be transmitted until acknowledgment of a successful reception is returned by the destination (or timeout is exceeded). The acknowledgment information shall be included in the header of the return packet. The ARQ scheme is only used on the payload in the packet and only on packets that have a CRC. The packet header and the synchronous data payload of HV and DV packets are not protected by the ARQ scheme.
7.6.1. Unnumbered ARQ
Bluetooth uses a fast, unnumbered acknowledgment scheme. An ACK (ARQN=1) or a NAK (ARQN=0) is returned in response to the receipt of a previously received packet. The Peripheral shall respond in the Peripheral-to-Central slot directly following the Central-to-Peripheral slot unless the Peripheral has scatternet commitments in that timeslot; the Central shall respond at the next event addressing the same Peripheral (the Central may have addressed other Peripherals between the last received packet from the considered Peripheral and the Central’s response to this packet). A packet reception is successful if the HEC passes and, when present, the MIC and CRC pass.
In the first POLL packet at the start of a new connection (as a result of a page, page scan, or role switch) the Central shall initialize the ARQN bit to NAK. The response packet sent by the Peripheral shall also have the ARQN bit set to NAK. The subsequent packets shall use the following rules. The initial value of the Central’s eSCO ARQN at link set-up shall be NAK.
The ARQN bit shall only be affected by data packets containing CRC and empty slots. As shown in Figure 7.12, Figure 7.13, and Figure 7.14, upon successful reception of a CRC packet, the ARQN bit shall be set to ACK. If, in any receive slot in the Peripheral, or, in a receive slot in the Central following transmission of a packet, one of these events applies:
no access code is detected
the HEC fails
the CRC fails
the MIC fails.
then the ARQN bit shall be set to NAK except in the conditions below:
In eSCO the ARQN bit may be set to ACK even when the CRC on an EV packet has failed thus enabling delivery of erroneous packets.
For ACL packets, if a CRC packet with a correct header has the same SEQN as the previously received CRC packet, the ARQN bit shall be set to ACK and the payload shall be ignored without checking the CRC.
Packets that have correct HEC but that are addressed to other Peripherals, or packets other than DH, DM, DV or EV packets, shall not affect the ARQN bit, except as noted in Section 7.6.2.2. In these cases the ARQN bit shall be left as it was prior to reception of the packet. For eSCO packets, the SEQN shall not be used when determining the ARQN. If an eSCO packet has been received successfully within the eSCO window subsequent receptions within the eSCO window shall be ignored. At the end of the eSCO window, the Central’s ARQN shall be retained for the first Central-to-Peripheral transmission in the next eSCO window.
The ARQN bit in the FHS packet is not meaningful. Contents of the ARQN bit in the FHS packet shall not be checked.
The ARQN bit in the extended inquiry response packet is reserved for future use.
Broadcast packets shall be checked on errors using the CRC, but no ARQ scheme shall be applied. Broadcast packets shall never be acknowledged.
In Figure 7.12, TX refers to the next transmission that the device makes, which might not be in the next slot. NO TX indicates that the device is not allowed to transmit in the next slot.
In Figure 7.14, "Packet OK" means that the packet has an allowed TYPE for the connection and the CRC is valid.

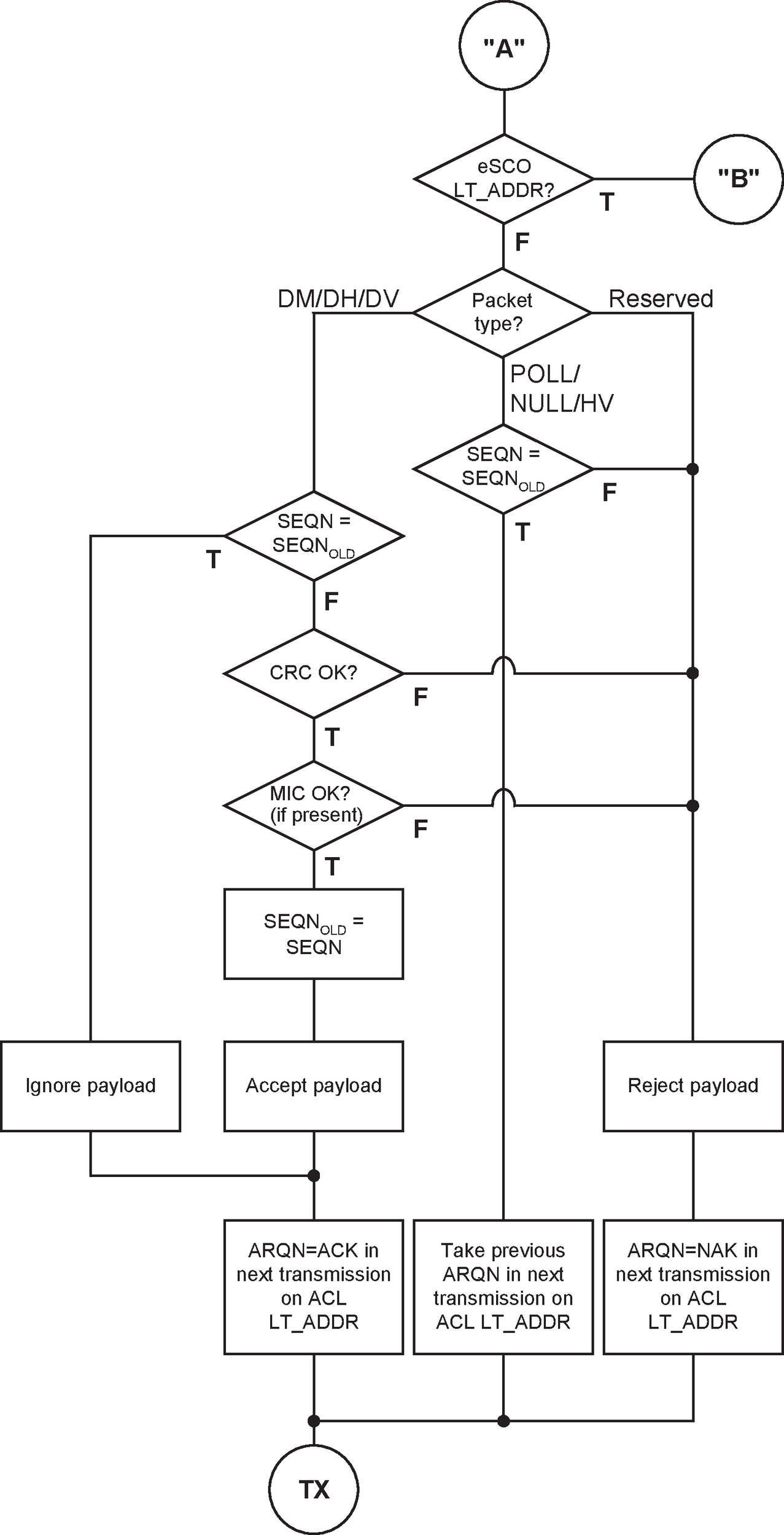
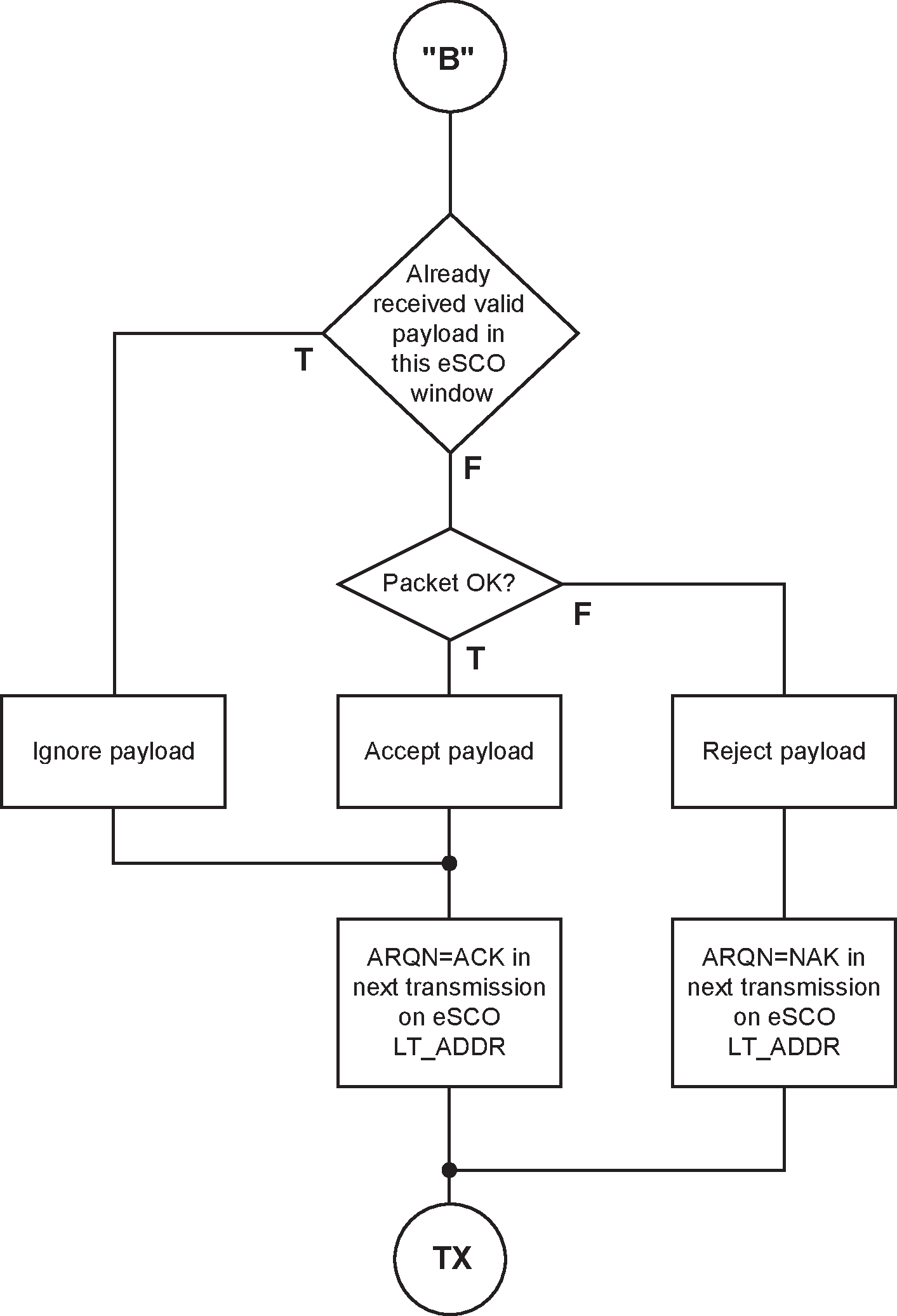
7.6.2. Retransmit filtering
The data payload shall be transmitted until a positive acknowledgment is received or a timeout is exceeded. A retransmission shall be carried out either because the packet transmission itself failed, or because the acknowledgment transmitted in the return packet failed (which has a lower failure probability since the header is more heavily coded). In the latter case, the destination keeps receiving the same payload over and over again. In order to filter out the retransmissions in the destination, the SEQN bit is present in the header. Normally, this bit is alternated for every new CRC data payload transmission. In case of a retransmission, this bit shall not be changed so the destination can compare the SEQN bit with the previous SEQN value. If different, a new data payload has arrived; otherwise it is the same data payload and may be ignored. Only new data payloads shall be transferred to the Baseband Resource Manager.
Note
Note: CRC data payloads can be carried only by DM, DH, DV or EV packets.
7.6.2.1. Initialization of SEQN at start of new connection
The SEQN bit of the first CRC data packet at the start of a connection (as a result of page, page scan, or role switch) on both the Central and the Peripheral sides shall be set to 1. The subsequent packets shall use the rules in the following sections.
7.6.2.2. ACL and SCO retransmit filtering
The SEQN bit shall only be affected by the CRC data packets as shown in Figure 7.15. It shall be inverted every time a new CRC data packet is sent. The CRC data packet shall be retransmitted with the same SEQN number until an ACK is received or the packet is flushed. When an ACK is received, a new payload may be sent and on that transmission the SEQN bit shall be inverted. If a device decides to flush (see Section 7.6.3), and it has not received an acknowledgment for the current packet, it shall replace the current packet with an ACL-U continuation packet with the same sequence number as the current packet and length zero. If it replaces the current packet in this way it shall not move on to transmit the next packet until it has received an ACK.
If the Peripheral receives a packet other than DH, DM, DV or EV with the SEQN bit inverted from that in the last header successfully received on the same LT_ADDR, it shall set the ARQN bit to NAK until a DH, DM, DV or EV packet is successfully received.

7.6.2.3. eSCO retransmit filtering
In eSCO, the SEQN bit shall be toggled every eSCO window. The value shall be constant for the duration of the eSCO window. The initial value of SEQN shall be zero.
For a given eSCO window the SEQN value shall be constant.
7.6.2.4. FHS retransmit filtering
The SEQN bit in the FHS packet is not meaningful. This bit may be set to any value. Contents of the SEQN bit in the FHS packet shall not be checked.
7.6.2.5. Extended inquiry response retransmit filtering
The SEQN bit in the extended inquiry response packet is reserved for future use.
7.6.2.6. Packets without CRC retransmit filtering
During transmission of packets without a CRC the SEQN bit shall remain the same as it was in the previous packet.
7.6.3. Flushing payloads
On ACL logical transports, the ARQ scheme can cause variable delay in the traffic flow since retransmissions are inserted to assure error-free data transfer. For certain communication links, only a limited amount of delay is allowed: retransmissions are allowed up to a certain limit at which the current payload shall be ignored. This data transfer is indicated as isochronous traffic. This means that the retransmit process must be overruled in order to continue with the next data payload. Aborting the retransmit scheme is accomplished by flushing the old data and forcing the Link Controller to take the next data instead.
Flushing results in loss of remaining portions of an L2CAP message. Therefore, the packet following the flush shall have a start packet indication of LLID = 10 in the payload header for the next L2CAP message. This informs the destination of the flush (see Section 6.6). Flushing will not necessarily result in a change in the SEQN bit value, see the previous section.
The Flush Timeout defines a maximum period after which all segments of the ACL-U packet with a Packet_Boundary_Flag value of 10 are flushed from the Controller buffer. The Flush Timeout shall start when the First segment of the ACL-U packet is stored in the Controller buffer. If the First segment of an ACL-U packet has a Packet_Boundary_Flag value of 00, it is non-automatically-flushable and shall not cause the Flush Timeout to start. After the Flush timeout has expired the Link Controller may continue transmissions according to the procedure described in Section 7.6.2.2, however the Baseband Resource Manager shall not continue the transmission of the ACL-U packet to the Link Controller. If the Baseband Resource Manager has further segments of the packet queued for transmission to the Link Controller it shall delete the remaining segments of the ACL-U packet from the queue. In case the complete ACL-U packet was not stored in the Controller buffer yet, any Continuation segments, received for the ACL logical transport, shall be flushed, until a First segment is received. When the complete ACL-U packet has been flushed, the Link Manager shall continue transmission of the next ACL-U packet for the ACL logical transport. The default Flush Timeout shall be infinite, i.e. re-transmissions are carried out until physical link loss occurs. This is also referred to as a 'reliable channel.' All devices shall support the default Flush Timeout. Reliable data shall be sent over a channel with a finite flush timeout by marking reliable packets as non-automatically-flushable.
On eSCO logical transports, packets shall be automatically flushed at the end of the eSCO window.
Connectionless Peripheral Broadcast packets are transmitted at each scheduled Connectionless Peripheral Broadcast Instant. If no new data is available, the Connectionless Peripheral Broadcast Transmitter shall transmit a packet with the last available data in the payload.
7.6.4. Multi-Peripheral considerations
In a piconet with multiple logical transports, the Central shall carry out the ARQ protocol independently on each logical transport.
7.6.5. Active Peripheral Broadcast packets
APB broadcast packets are packets transmitted by the Central to all the Peripherals simultaneously (see Section 8.6.4) If multiple hop sequences are being used each transmission may only be received by some of the Peripherals. In this case the Central shall repeat the transmission on each hop sequence. An APB broadcast packet shall be indicated by the all-zero LT_ADDR.
Note
Note: The FHS packet and the extended inquiry response packet are the only packets which may have an all-zero LT_ADDR but are not broadcast packets.
Broadcast packets shall not be acknowledged (at least not at the LC level), hence each broadcast packet is transmitted at least a fixed number of times. An APB broadcast packet should be transmitted NBC times before the next broadcast packet of the same broadcast message is transmitted, see Figure 7.16. Optionally, an APB broadcast packet may be transmitted NBC + 1 times, so NBC=1 means that each broadcast packet should be sent only once but may be sent twice. However, time-critical broadcast information may abort the ongoing broadcast train. In addition, an LMP packet sent on the APB-C logical link is always a complete message for these purposes and is always sent exactly once; the LMP specification may provide requirements for whether and when to send another message with the same or related contents.
If multiple hop sequences are being used then the Central may transmit on the different hop sequences in any order, providing that transmission of a new broadcast packet shall not be started until all transmissions of any previous broadcast packet have completed on all hop sequences. The transmission of a single broadcast packet may be interleaved among the hop sequences to minimize the total time to broadcast a packet. The Central has the option of transmitting only NBC times on channels common to all hop sequences.
APB broadcast packets with a CRC shall have their own sequence number. The SEQN of the first broadcast packet with a CRC shall be set to SEQN = 1 by the Central and shall be inverted for each new broadcast packet with CRC thereafter. APB broadcast packets without a CRC have no influence on the sequence number. The Peripheral shall accept the SEQN of the first broadcast packet it receives in a connection and shall check for change in SEQN for subsequent broadcast packets. Since there is no acknowledgment of broadcast messages and there is no end packet indication, it is important to receive the start packets correctly. To ensure this, repetitions of the broadcast packets that are L2CAP start packets and LMP packets shall not be filtered out. These packets shall be indicated by LLID=1X in the payload header as explained in Table 6.5. Only repetitions of the L2CAP continuation packets shall be filtered out.
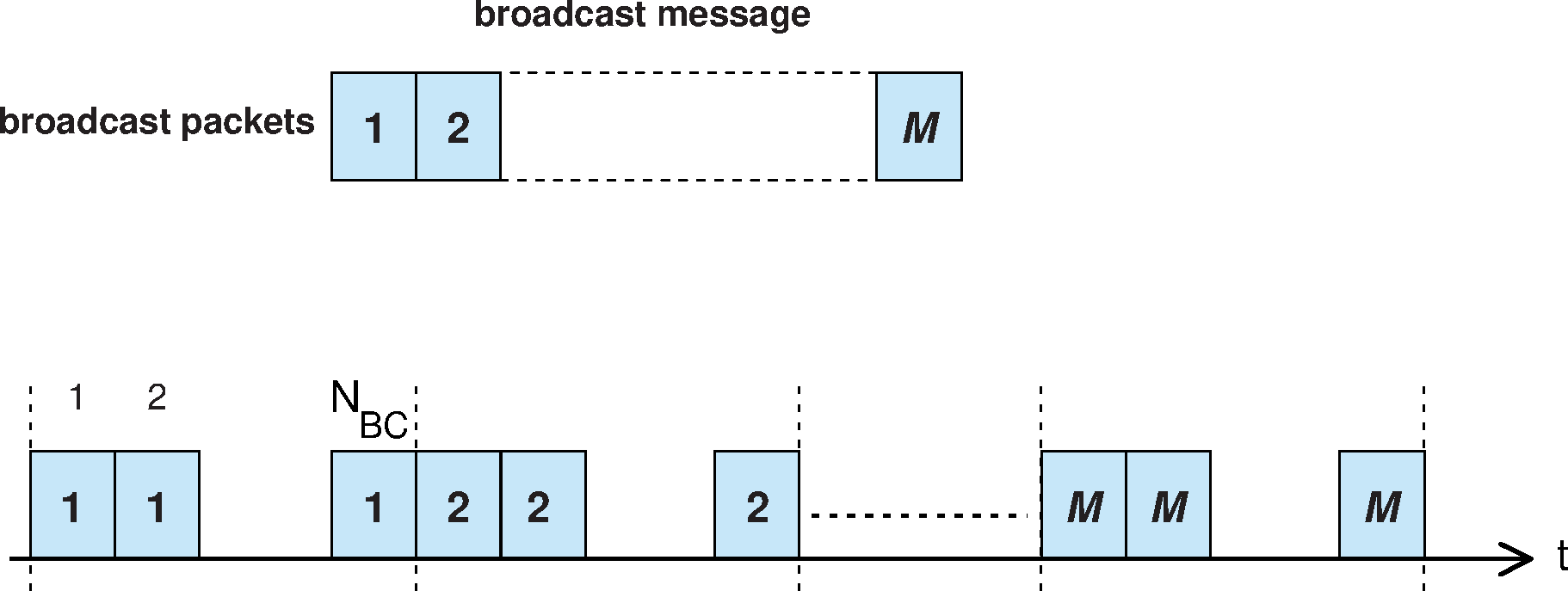
7.7. Erroneous synchronous data reporting
Erroneous data reporting may be enabled for synchronous links. When enabled, synchronous data shall be processed as follows:
If, during an (e)SCO interval, an eSCO packet was received with valid HEC, an allowed TYPE for the connection, and valid CRC, or a SCO packet was received with valid HEC, the received payload data shall be sent to the upper-edge of the Controller with a "good data" indication.
If, during an eSCO interval, eSCO packets with valid HEC were received, but none of them had an allowed TYPE for the connection and a valid CRC, the best known data available (e.g., data derived from the received data or the actual payload data that was received with a CRC error) shall be sent to the upper-edge of the Controller with a "data with possible errors" indication.
If, during an (e)SCO interval, no SCO or eSCO packet with valid HEC has been received, a "lost data" indication shall be sent to the upper-edge of the Controller.
7.8. Message Integrity Check
When encryption with AES-CCM is enabled, a Message Integrity Check (MIC) is added to the payload before the CRC for packets that are defined to include the MIC. The MIC is sent Most Significant Octet (MSO) first.
8. Link Controller operation
This section describes how a piconet is established and how devices can be added to and released from the piconet. Several states of operation of the devices are defined to support these functions. In addition, the operation of several piconets with one or more common members, the scatternet, is discussed.
8.1. Overview of states
Figure 8.1 shows a state diagram illustrating the different states used in the Link Controller. There are two major states: Standby and Connection; in addition, there are nine substates, Page, Page Scan, Inquiry, Inquiry Scan, Synchronization Train, Synchronization Scan, Central Page Response, Peripheral Page Response, and Inquiry Response (the Central Page Response, Peripheral Page Response, and Inquiry Response substates are not shown in the simplified figure below). The substates are interim states that are used to establish connections and enable device discovery. To move from one state or substate to another, either commands from the link manager are used, or internal signals in the Link Controller are used (such as the trigger signal from the correlator and the timeout signals).

8.2. Standby state
The Standby state is the default state in the device. In this state, the device may be in a low-power mode. Only the native clock is running with a worst case accuracy of ±250 ppm.
The Controller may leave the Standby state to scan for page or inquiry messages, or to page or inquiry itself.
8.3. Connection establishment substates
In order to establish new connections the paging procedure or the synchronization scan procedure is used. Only the Bluetooth Device Address is required to set up a connection using the paging procedure. Knowledge about the clock, obtained from the inquiry procedure (see Section 8.4) or from a previous connection with this device, and the page scanning mode of the other device will accelerate the paging procedure. A device that establishes a connection using a page procedure will automatically become the Central of the connection. A device that establishes a connection using a synchronization scan procedure does so in two steps. First, from within the Synchronization Scan substate, the BR/EDR Controller follows the synchronization scan procedure to collect clock, packet timing, and AFH channel map information from the Central and then transitions to the Standby state. Second, as commanded by the Host, the BR/EDR Controller transitions from the Standby state to the Connectionless Peripheral Broadcast mode of the Connection state.
The truncated page procedure is a modification of the paging procedure and is used to deliberately generate a page response timeout on the Peripheral.
8.3.1. Page Scan substate
In the Page Scan substate, a device may be configured to use either the standard or generalized interlaced scanning procedure. During a standard scan, a device listens for the duration of the scan window Tw_page_scan (11.25 ms default, see HCI [Vol 4] Part E, Section 7.3.20), while the generalized interlaced scan is performed as two back to back scans of Tw_page_scan. If the scan interval is not at least twice the scan window, then generalized interlaced scan shall not be used. During each scan window, the device shall listen at a single hop frequency, its correlator matched to its device access code (DAC). The scan window shall be long enough to completely scan 16 page frequencies.
When a device enters the Page Scan substate, it shall select the scan frequency according to the page hopping sequence determined by the device's Bluetooth Device Address, see Section 2.6.4.1. The phase in the sequence shall be determined by CLKN16-12 of the device’s native clock; that is, every 1.28 s a different frequency is selected.
In the case of a standard scan, if the correlator exceeds the trigger threshold during the page scan, the device shall enter the Peripheral Page Response substate described in Section 8.3.3.1. The scanning device may also use generalized interlaced scan. In this case, if the correlator does not exceed the trigger threshold during the first scan it shall scan a second time using the phase in the sequence determined by [CLKN16-12 + interlace_offset] mod 32. If on this second scan the correlator exceeds the trigger threshold the device shall enter the Peripheral Page Response substate using [CLKN16-12 + interlace_offset] mod 32 as the frozen CLKN* in the calculation for Xprp (see Section 2.6.4.3 for details). If the correlator does not exceed the trigger threshold during a scan in normal mode or during the second scan in interlaced scan mode it shall return to either the Standby or Connection state.
The interlace_offset value ranges from 0 to 31. The value 16 should be used unless the pattern of slots that are not available for scanning implies a different value should be used.
The Page Scan substate can be entered from the Standby state or the Connection state. In the Standby state, no connection has been established and the device can use all the capacity to carry out the page scan. Before entering the Page Scan substate from the Connection state, the device should reserve as much capacity as possible for scanning. If desired, the device may place ACL connections in Hold mode (see Section 8.8) or Sniff mode (see Section 8.7). Synchronous connections should not be interrupted by the page scan, although eSCO retransmissions should be paused during the scan. The page scan may be interrupted by the reserved synchronous slots which should have higher priority than the page scan. SCO packets should be used requiring the least amount of capacity (HV3 packets). The scan window shall be increased to minimize the setup delay. If one SCO logical transport is present using HV3 packets and TSCO=6 slots or one eSCO logical transport is present using EV3 packets and TeSCO=6 slots, a total scan window Tw_page_scan of at least 36 slots (22.5 ms) is recommended; if two SCO links are present using HV3 packets and TSCO=6 slots or two eSCO links are present using EV3 packets and TeSCO=6 slots, a total scan window of at least 54 slots (33.75 ms) is recommended.
The scan interval Tpage_scan is defined as the interval between the beginnings of two consecutive page scans. A distinction is made between the case where the scan interval is equal to the scan window Tw_page_scan (continuous scan), the scan interval is maximal 1.28 s, or the scan interval is maximal 2.56 s. These three cases shall determine the behavior of the paging device; that is, whether the paging device shall use R0, R1 or R2, see also Section 8.3.2. Table 8.1 illustrates the relationship between Tpage_scan and modes R0, R1 and R2. Although scanning in the R0 mode is continuous, the scanning may be interrupted for example by reserved synchronous slots. The scan interval information (also known as the page scan repetition mode) is included in the SR field in the FHS packet.
SR mode | Tpage_scan |
|---|---|
R0 | ≤ 1.28 s and = Tw_page_scan |
R1 | ≤ 1.28 s |
R2 | ≤ 2.56 s |
8.3.2. Page substate
The Page substate is used by the Central (source) to activate and connect to a Peripheral (destination) in the Page Scan substate. The Central tries to coincide with the Peripheral's scan activity by repeatedly transmitting the paging message consisting of the Peripheral’s device access code (DAC) in different hop channels. Since the Bluetooth clocks of the Central and the Peripheral are not synchronized, the Central does not know exactly when the Peripheral wakes up and on which hop frequency. Therefore, it transmits a train of identical page messages at different hop frequencies and listens in between the transmit intervals until it receives a response from the Peripheral.
The page procedure in the Central consists of a number of steps. First, the Host communicates the BD_ADDR of the Peripheral to the Controller. This BD_ADDR shall be used by the Central to determine the page hopping sequence; see Section 2.6.4.2. If the BD_ADDR of the Peripheral is identical to the BD_ADDR of the Central, then the Central's Controller should reject the page procedure. For the phase in the sequence, the Central shall use an estimate of the Peripheral’s clock. For example, this estimate can be derived from timing information that was exchanged during the last encounter with this particular device (which could have acted as a Central at that time), or from an inquiry procedure. With this estimate CLKE of the Peripheral’s Bluetooth clock, the Central can predict on which hop channel the Peripheral starts page scanning.
The estimate of the Bluetooth clock in the Peripheral can be completely wrong. Although the Central and the Peripheral use the same hopping sequence, they use different phases in the sequence and might never select the same frequency. To compensate for the clock drifts, the Central shall send its page message during a short time interval on a number of wake-up frequencies. It shall transmit also on hop frequencies just before and after the current, predicted hop frequency. During each TX slot, the Central shall sequentially transmit on two different hop frequencies. In the following RX slot, the receiver shall listen sequentially to two corresponding RX hops for an ID packet. The RX hops shall be selected according to the page response hopping sequence. The page response hopping sequence is strictly related to the page hopping sequence: for each page hop there is a corresponding page response hop. The RX/TX timing in the Page substate is described in Section 2.2.5, see also Figure 2.7. In the next TX slot, the Central shall transmit on two hop frequencies different from the former ones.
Note
Note: The hop rate is increased to 3200 hops per second.
With the increased hopping rate as described above, the transmitter can cover 16 different hop frequencies in 16 slots or 10 ms. The page hopping sequence is divided over two paging trains A and B of 16 frequencies. Train A includes the 16 hop frequencies surrounding the current, predicted hop frequency f(k), where k is determined by the clock estimate CLKE16-12. The first train consists of hops
f(k-8), f(k-7),...,f(k),...,f(k+7)
When the difference between the Bluetooth clocks of the Central and the Peripheral is between -8x1.28 s and +7x1.28 s, one of the frequencies used by the Central will be the hop frequency the Peripheral will listen to. Since the Central does not know when the Peripheral will enter the Page Scan substate, the Central has to repeat this train A Npage times or until a response is obtained, whichever is shorter. If the Peripheral scan interval corresponds to R1, the repetition number is at least 128; if the Peripheral scan interval corresponds to R2 or if the Central has not previously read the Peripheral's SR (page scan repetition) mode, the repetition number is at least 256. If the Central has not previously read the Peripheral's SR mode it shall use Npage >= 256.
Note
Note: CLKE16-12 changes every 1.28 s; therefore, every 1.28 s, the trains will include different frequencies of the page hopping set.
When the difference between the Bluetooth clocks of the Central and the Peripheral is less than -8x1.28 s or larger than +7x1.28 s, the remaining 16 hops are used to form the new 10 ms train B. The second train consists of hops
f(k-16), f(k-15),...,f(k-9),f(k+8)...,f(k+15)
Train B shall be repeated for Npage times. If no response is obtained, knudge may be updated in the case where slots to receive are periodically not available and train A shall be tried again Npage times. Alternate use of train A and train B and updates of knudge shall be continued until a response is received or the timeout pageTO + extended_pageTO is exceeded. If a response is returned by the Peripheral, the Central enters the Central Page Response substate.
The Page substate may be entered from the Standby state or the Connection state. In the Standby state, no connection has been established and the device can use all the capacity to carry out the page. Before entering the Page substate from the Connection state, the device should free as much capacity as possible for paging. To ensure this, it is recommended that the ACL connections are put on hold. However, the synchronous connections shall not be disturbed by the page. This means that the page will be interrupted by the reserved SCO and eSCO slots which have higher priority than the page. In order to obtain as much capacity for paging, it is recommended to use the SCO packets which use the least amount of capacity (HV3 packets). If SCO or eSCO links are present, the repetition number Npage of a single train shall be increased, see Table 8.2. Here it has been assumed that the HV3 packet are used with an interval TSCO=6 slots or EV3 packets are used with an interval of TeSCO=6 slots, which would correspond to a 64 kb/s synchronous link.
SR mode | no synchronous link | one synchronous link (HV3) | two synchronous links (HV3) |
|---|---|---|---|
R0 | Npage≥1 | Npage≥2 | Npage≥3 |
R1 | N page≥128 | Npage≥256 | Npage≥384 |
R2 | Npage≥256 | Npage≥512 | Npage≥768 |
The construction of the page train shall be independent of the presence of synchronous links; that is, synchronous packets are sent on the reserved slots but shall not affect the hop frequencies used in the unreserved slots, see Figure 8.2.

8.3.3. Page response substates
When a page message is successfully received by the Peripheral, there is a coarse FH synchronization between the Central and the Peripheral. Both the Central and the Peripheral enter a response substate to exchange vital information to continue the connection setup. It is important for the piconet connection that both devices shall use the same channel access code, use the same channel hopping sequence, and their clocks are synchronized. These parameters shall be derived from the Central. The device that initializes the connection (starts paging) is defined as the Central (which is thus only valid during the time the piconet exists). The channel access code and channel hopping sequence shall be derived from the Bluetooth Device Address (BD_ADDR) of the Central. The timing shall be determined by the Central's clock. An offset shall be added to the Peripheral’s native clock to temporarily synchronize the Peripheral's clock to the Central's clock. At start-up, the Central's parameters are transmitted from the Central to the Peripheral. The messaging between the Central and the Peripheral at start-up is specified in this section.
If Central and Peripheral are already connected (irrespective of roles) then the Peripheral shall either ignore the page or shall immediately close the existing connection without sending any further packets relating to that connection and then continue with the page response procedure.
If the BD_ADDR of the Central is identical to the BD_ADDR of the Peripheral, then the Peripheral's Controller should ignore the page.
The initial messaging between Central and Peripheral is shown in Table 8.3 and in Figure 8.3 and Figure 8.4. In those two figures frequencies f (k), f(k+1), etc. are the frequencies of the page hopping sequence determined by the Peripheral’s BD_ADDR. The frequencies f’(k), f’(k+1), etc. are the corresponding page_response frequencies (Peripheral-to-Central). The frequencies g(m) belong to the basic channel hopping sequence.
Step | Message | Packet Type | Direction | Hopping Sequence | Access Code and Clock |
|---|---|---|---|---|---|
1 | Page | ID | Central to Peripheral | Page | Peripheral |
2 | First Peripheral page response | ID | Peripheral to Central | Page response | Peripheral |
3 | Central page response | FHS | Central to Peripheral | Page | Peripheral |
4 | Second Peripheral page response | ID | Peripheral to Central | Page response | Peripheral |
5 | 1st packet Central | POLL | Central to Peripheral | Channel | Central |
6 | 1st packet Peripheral | NULL/DM1/DH1 | Peripheral to Central | Channel | Central |
In step 1 (see Table 8.3), the Central is in Page substate and the Peripheral in the Page Scan substate. Assume in this step that the page message sent by the Central reaches the Peripheral. On receiving the page message, the Peripheral enters the Peripheral Page Response substate in step 2. The Central waits for a reply from the Peripheral and when this arrives in step 2, it shall enter the Central Page Response substate in step 3.
Note
Note: During the initial message exchange, all parameters are derived from the Peripheral’s device address, and that only the page hopping and page response hopping sequences are used (are also derived from the Peripheral’s device address). When the Central and Peripheral enter the response states, their clock input to the page and page response hop selection is frozen as is described in Section 2.6.4.3.

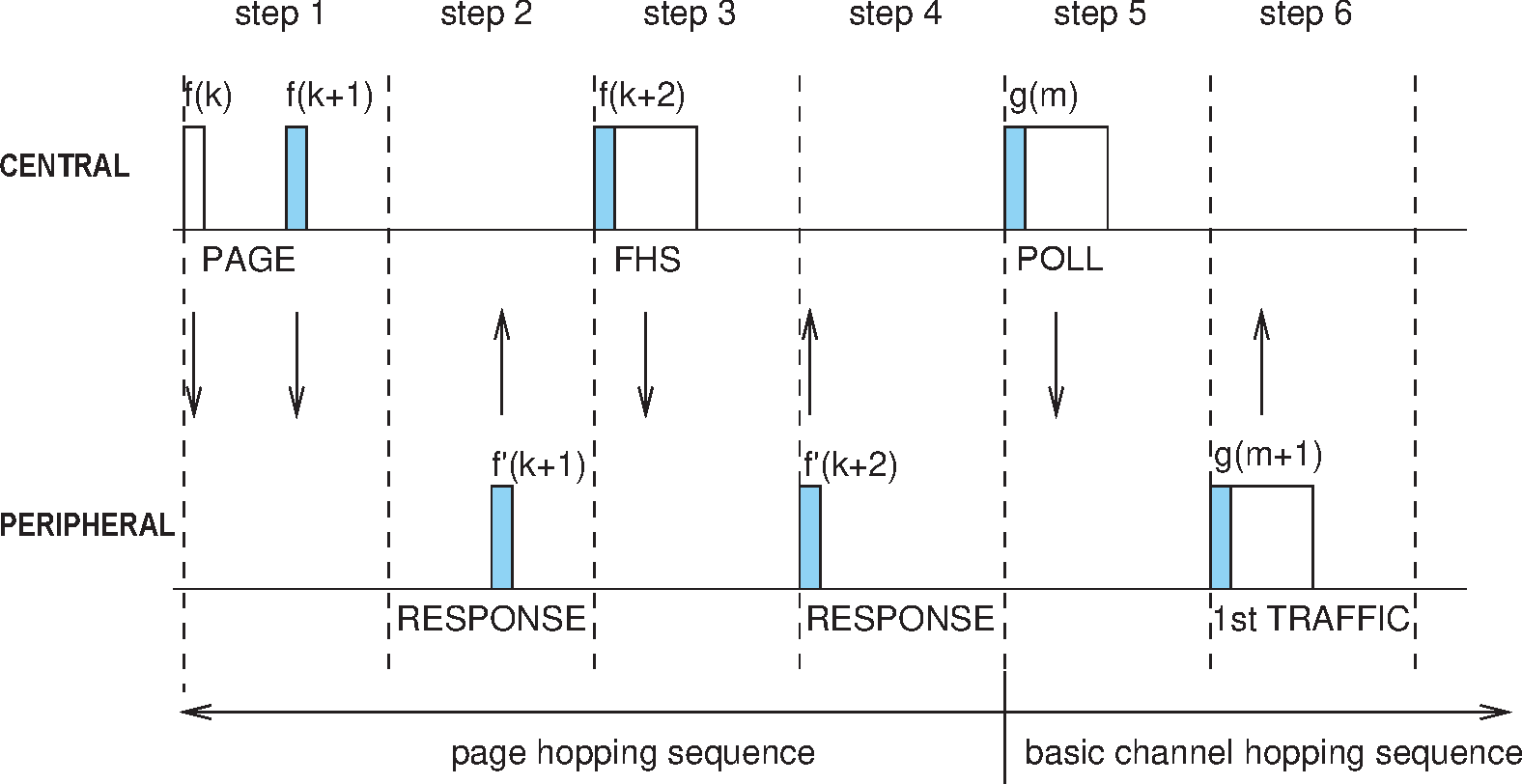
In the case of the truncated page procedure, the messaging stops after step 2 in the sequence shown in Table 8.3. This procedure is illustrated in Figure 8.5 and Figure 8.6.


8.3.3.1. Peripheral Page Response substate
After having received the page message in step 1, the Peripheral shall transmit a Peripheral page response message (the Peripheral's device access code) in step 2. This response message shall be the Peripheral’s device access code. The Peripheral shall transmit this response 625 μs after the beginning of the received page message and at the response hop frequency that corresponds to the hop frequency in which the page message was received. The Peripheral’s transmission is therefore time aligned to the Central’s transmission. During initial messaging, the Peripheral shall still use the page response hopping sequence to return information to the Central. The clock input CLKN16-12 shall be frozen at the value it had at the time the page message was received.
After having sent the response message, the Peripheral’s receiver shall be activated 312.5 μs after the start of the response message and shall await the arrival of an FHS packet.
Note
Note: An FHS packet can arrive 312.5 μs after the arrival of the page message as shown in Figure 8.4, and not after 625 μs as is usually the case in the piconet physical channel RX/TX timing (more details about the timing can be found in Section 2.4.4).
If the setup fails before the Connection state has been reached, the following procedure shall be carried out. The Peripheral shall listen as long as no FHS packet is received until pagerespTO is exceeded. Every 1.25 ms, however, it shall select the next Central-to-Peripheral hop frequency according to the page hop sequence. If nothing is received after pagerespTO, the Peripheral shall return back to the Page Scan substate for one scan period. Length of the scan period depends on the synchronous reserved slots present. If no page message is received during this additional scan period, the Peripheral shall resume scanning at its regular scan interval and return to the state it was in prior to the first page scan state.
If an FHS packet is received by the Peripheral in the Peripheral Page Response substate, the Peripheral shall return a Peripheral page response message in step 4 to acknowledge reception of the FHS packet. This response shall use the page response hopping sequence. The transmission of the Peripheral page response packet is based on the reception of the FHS packet. Then the Peripheral shall change to the Central's channel access code and clock as received from the FHS packet. Only the 26 MSBs of the Central's clock are transferred: the timing shall be such that CLK1 and CLK0 are both zero at the time the FHS packet was received as the Central transmits in even slots only. The offset between the Central’s clock and the Peripheral’s clock shall be determined from the Central’s clock in the FHS packet and reported to the Peripheral’s Baseband Resource Manager.
Finally, the Peripheral enters the Connection state in step 5. From then on, the Peripheral shall use the Central’s clock and the Central's BD_ADDR to determine the basic channel hopping sequence and the channel access code. The Peripheral shall use the LT_ADDR in the FHS payload as the primary LT_ADDR in the Connection state. The connection mode shall start with a POLL packet transmitted by the Central. The Peripheral may respond with a NULL, DM1, or DH1 packet. If the POLL packet is not received by the Peripheral, or the response packet is not received by the Central, within newconnectionTO number of slots after FHS packet acknowledgment, the Central and the Peripheral shall return to Page and Page Scan substates, respectively. See Section 8.5.
8.3.3.2. Central Page Response substate
When the Central has received a Peripheral page response message in step 2, and the Central is not executing the truncated page procedure, it shall enter the Central Response substate. It shall freeze the current clock input to the page hop selection scheme. The Central shall then transmit an FHS packet in step 3 containing the Central’s real-time Bluetooth clock, the Central’s BD_ADDR, the BCH parity bits, and the Class of Device. The FHS packet contains all information to construct the channel access code without requiring a mathematical derivation from the Central's Bluetooth Device Address. The LT_ADDR field in the packet header of FHS packets in the Central Page Response substate shall be set to all-zeros. The FHS packet shall be transmitted at the beginning of the Central-to-Peripheral slot following the slot in which the Peripheral responded. The FHS packet shall carry the all-zero LT_ADDR. The TX timing of the FHS is not based on the reception of the response packet from the Peripheral. The FHS packet may therefore be sent 312.5 μs after the reception of the response packet like shown in Figure 8.4 and not 625 μs after the received packet as is usual in the piconet physical channel RX/TX timing, see also Section 2.4.4.
After the Central has sent its FHS packet, it shall wait for a second Peripheral page response message in step 4 acknowledging the reception of the FHS packet. This response shall be the Peripheral’s device access code. If no response is received, the Central shall retransmit the FHS packet with an updated clock and still using the Peripheral’s parameters. It shall retransmit the FHS packet with the clock updated each time until a second Peripheral page response message is received, or the timeout of pagerespTO is exceeded. In the latter case, the Central shall return to the Page substate and send an error message to the Baseband Resource Manager. During the retransmissions of the FHS packet, the Central shall use the page hopping sequence.
If the Peripheral’s response is received, the Central shall change to using the Central’s parameters, so it shall use the channel access code and the Central's clock. The lower clock bits CLK0 and CLK1 shall be reset to zero at the start of the FHS packet transmission and are not included in the FHS packet. Finally, the Central enters the Connection state in step 5. The Central BD_ADDR shall be used to change to a new hopping sequence, the basic channel hopping sequence. The basic channel hopping sequence uses all 79 hop channels in a pseudo-random fashion, see also Section 2.6.4.7. The Central shall now send its first traffic packet in a hop determined with the new (Central) parameters. This first packet shall be a POLL packet. See Section 8.5. This packet shall be sent within newconnectionTO number of slots after reception of the FHS packet acknowledgment. The Peripheral may respond with a NULL, DM1, or DH1 packet. If the POLL packet is not received by the Peripheral or the POLL packet response is not received by the Central within newconnectionTO number of slots, the Central and the Peripheral shall return to Page and Page Scan substates, respectively.
8.4. Device discovery substates
In order to discover other devices a device shall enter Inquiry substate. In this substate, it shall repeatedly transmit the inquiry message (ID packet, see Section 6.5.1.1) at different hop frequencies. The inquiry hop sequence is derived from the LAP of the GIAC. Thus, even when DIACs are used, the applied hopping sequence is generated from the GIAC LAP. A device that allows itself to be discovered, shall regularly enter the Inquiry Scan substate to respond to inquiry messages. The following sections describe the message exchange and contention resolution during inquiry response. The inquiry response is optional: a device is not forced to respond to an inquiry message.
During the Inquiry substate, the discovering device collects the Bluetooth Device Addresses and clocks of all devices that respond to the inquiry message. In addition, the discovering device also collects extended information (e.g. local name and supported services) from devices that respond with an extended inquiry response packet. It can then, if desired, make a connection to any one of the discovered devices by means of the previously described page procedure.
The inquiry message broadcast by the source does not contain any information about the source. However, it may indicate which class of devices should respond. There is one general inquiry access code (GIAC) to inquire for any device, and a number of dedicated inquiry access codes (DIAC) that only inquire for a certain type of device. The inquiry access codes are derived from reserved Bluetooth Device Addresses and are further described in Section 6.3.1.
8.4.1. Inquiry Scan substate
The Inquiry Scan substate is very similar to the Page Scan substate. However, instead of scanning for the device's device access code, the receiver shall scan for the inquiry access code long enough to completely scan for 16 inquiry frequencies. Two types of scans are defined: standard and generalized interlaced. In the case of a standard scan the length of this scan period is denoted Tw_inquiry_scan (11.25 ms default, see HCI [Vol 4] Part E, Section 7.3.22). The standard scan is performed at a single hop frequency as defined by Xir4-0 (see Section 2.6.4.6). The generalized interlaced scan is performed as two back to back scans of Tw_inquiry_scan where the first scan is on the normal hop frequency and the second scan is defined by [Xir4-0 + interlace_offset] mod 32. If the scan interval is not at least twice the scan window then generalized interlaced scan shall not be used. The inquiry procedure uses 32 dedicated inquiry hop frequencies according to the inquiry hopping sequence. These frequencies are determined by the general inquiry address. The phase is determined by the native clock of the device carrying out the inquiry scan; the phase changes every 1.28 s.
The interlace_offset value ranges from 0 to 31. The value 16 should be used unless the pattern of slots that are not available for scanning implies a different value should be used.
Instead of, or in addition to, the general inquiry access code, the device may scan for one or more dedicated inquiry access codes. However, the scanning shall follow the inquiry scan hopping sequence determined by the general inquiry address. If an inquiry message is received during an inquiry wake-up period, the device shall enter the Inquiry Response substate.
The Inquiry Scan substate can be entered from the Standby state or the Connection state. In the Standby state, no connection has been established and the device can use all the capacity to carry out the inquiry scan. Before entering the Inquiry Scan substate from the Connection state, the device should reserve as much capacity as possible for scanning. If desired, the device may place ACL logical transports in Sniff mode or Hold mode. Synchronous logical transports are preferably not interrupted by the inquiry scan, although eSCO retransmissions should be paused during the scan. In this case, the inquiry scan may be interrupted by the reserved synchronous slots. SCO packets should be used requiring the least amount of capacity (HV3 packets). The scan window, Tw inquiry scan, shall be increased to increase the probability to respond to an inquiry message. If one SCO logical transport is present using HV3 packets and TSCO=6 slots or one eSCO logical transport is present using EV3 packets and TeSCO=6 slots, a total scan window of at least 36 slots (22.5 ms) is recommended; if two SCO links are present using HV3 packets and TSCO=6 slots or two eSCO links are present using EV3 packets and TeSCO=6 slots, a total scan window of at least 54 slots (33.75 ms) is recommended.
The scan interval Tinquiry scan is defined as the interval between two consecutive inquiry scans. The inquiry scan interval shall be less than or equal to 2.56 s.
8.4.2. Inquiry substate
The Inquiry substate is used to discover new devices. This substate is very similar to the Page substate; the TX/RX timing shall be the same as in paging, see Section 2.4.4 and Figure 2.7. The TX and RX frequencies shall follow the inquiry hopping sequence and the inquiry response hopping sequence, and are determined by the general inquiry access code and the native clock of the discovering device. In between inquiry transmissions, the receiver shall scan for inquiry response messages. When a response is received, the entire packet (an FHS packet) shall be read. If the EIR bit in the FHS packet is set to one, the device should try to receive the extended inquiry response packet 1250 μs after the start of the FHS packet. After this, the device shall continue with inquiry transmissions. The device in an Inquiry substate shall not acknowledge the inquiry response messages. If enabled by the Host (see HCI [Vol 4] Part E, Section 7.3.50), the RSSI value of the inquiry response message shall be measured. It shall keep probing at different hop channels and in between listening for response packets. As in the Page substate, two 10 ms trains A and B are defined, splitting the 32 frequencies of the inquiry hopping sequence into two 16-hop parts. A single train shall be repeated for at least Ninquiry=256 times before a new train is used. In order to collect all responses in an error-free environment, at least three train switches must have taken place. As a result, the Inquiry substate may have to last for 10.24 s unless the inquirer collects enough responses and aborts the Inquiry substate earlier. If desired, the inquirer may also prolong the Inquiry substate to increase the probability of receiving all responses in an error-prone environment. When some receive slots are periodically not available, it may require up to 31 train switches to collect all responses in an error-free environment, depending on the pattern of the available receive slots. Before each switch to train A, knudge may be updated. As a result, the Inquiry substate may have to last for 40.96 s. If an inquiry procedure is automatically initiated periodically (say a 10 s period every minute), then the interval between two inquiry instances shall be determined randomly. This is done to avoid two devices synchronizing their inquiry procedures.
The Inquiry substate is continued until stopped by the Baseband Resource Manager (when it decides that it has sufficient number of responses), when a timeout has been reached (Inquiry_Length + Extended_Inquiry_Length), or by a command from the Host to cancel the inquiry procedure.
The Inquiry substate can be entered from the Standby state or the Connection state. In the Standby state, no connection has been established and the device can use all the capacity to carry out the inquiry. Before entering the Inquiry substate from the Connection state, the device should free as much capacity as possible for inquiry. To ensure this, it is recommended that the ACL logical transports are placed in Sniff mode or Hold mode. However, the reserved slots of synchronous logical transports shall not be disturbed by the inquiry. This means that the inquiry will be interrupted by the reserved SCO and eSCO slots which have higher priority than the inquiry. In order to obtain as much capacity as possible for inquiry, it is recommended to use the SCO packets which use the least amount of capacity (HV3 packets). If SCO or eSCO links are present, the repetition number Ninquiry shall be increased, see Table 8.4.
Here it has been assumed that HV3 packets are used with an interval TSCO=6 slots or EV3 packets are used with an interval of TeSCO=6 slots, which would correspond to a 64 kb/s synchronous link.
No synchronous links | One synchronous link (HV3) | Two synchronous links (HV3) | |
|---|---|---|---|
Ninquiry | ≥ 256 | ≥ 512 | ≥ 768 |
If an extended inquiry response packet could not be received because of higher priority traffic, the reception failed due to HEC or CRC failure, or because the packet type is not supported by the device, the inquiry response shall be reported to higher layers as an extended inquiry response with all-zero data.
8.4.3. Inquiry Response substate
The response substate for inquiries differs completely from the Peripheral Page Response substate applied for pages. When the inquiry message is received in the Inquiry Scan substate, the recipient shall return an inquiry response (FHS) packet containing the recipient's device address (BD_ADDR) and other parameters. If the recipient has non-zero extended inquiry response data to send it shall return an extended inquiry response packet after the FHS packet.
The following protocol in the Peripheral's inquiry response shall be used. On the first inquiry message received in the Inquiry Scan substate the Peripheral shall enter the Inquiry Response substate. If the Peripheral has non-zero extended inquiry response data to send it shall return an FHS packet with the EIR bit set to one to the Central 625 μs after the inquiry message was received. It shall then return an extended inquiry response packet 1250 μs after the start of the FHS packet. If the Peripheral's extended inquiry response data is all zeroes the Peripheral shall only return an FHS packet with the EIR bit set to zero. A contention problem could arise when several devices are in close proximity to the inquiring device and all respond to an inquiry message at the same time. However, because every device has a free running clock it is highly unlikely that they all use the same phase of the inquiry hopping sequence. In order to avoid repeated collisions between devices that wake up in the same inquiry hop channel simultaneously, a device shall back-off for a random period of time. Thus, if the device receives an inquiry message and returns an FHS packet, it shall generate a random number, RAND, between 0 and MAX_RAND. For scanning intervals ≥ 1.28 s MAX_RAND shall be 1023, however, for scanning intervals < 1.28 s MAX_RAND may be as small as 127. A profile that uses a special DIAC may choose to use a smaller MAX_RAND than 1023 even when the scanning interval is ≥ 1.28 s. The Peripheral shall return to the Connection or Standby state for the duration of at least RAND time slots. Before returning to the Connection and Standby state, the device may go through the Page Scan substate. After at least RAND slots, the device shall add an offset of 1 to the phase in the inquiry hop sequence (the phase has a 1.28 s resolution) and return to the Inquiry Scan substate again. If the Peripheral is triggered again, it shall repeat the procedure using a new RAND. The offset to the clock accumulates each time an FHS packet is returned. During a probing window, a Peripheral may respond multiple times, but on different frequencies and at different times. Reserved synchronous slots should have priority over response packets; that is, if a response packet overlaps with a reserved synchronous slot, it shall not be sent but the next inquiry message is awaited. If a device has extended inquiry response data to send but the extended inquiry response packet overlaps with a reserved synchronous slot the FHS packet may be sent with the EIR bit set to zero.
The messaging during the inquiry routines is summarized in Table 8.5. In step 1, the Central transmits an inquiry message using the inquiry access code and its own clock. The Peripheral responds with the FHS packet containing the Peripheral’s Bluetooth Device Address, native clock and other Peripheral information. This FHS packet is returned at times that tend to be random. The FHS packet is not acknowledged in the inquiry routine, but it is retransmitted at other times and frequencies as long as the Central is probing with inquiry messages. If the Peripheral has non-zero extended inquiry response data it sends an extended inquiry response packet to the Central in step 3.
The extended inquiry response packet is an ACL packet with type DM1, DM3, DM5, DH1, DH3 or DH5. To minimize interference it is recommended to use the shortest packet that fits the data. The packet shall be sent on the same frequency as the FHS packet, 1250 µs after the start of the FHS packet. In the packet header, LT_ADDR shall be set to zero. TYPE shall be one of DM1, DM3, DM5, DH1, DH3 or DH5. FLOW, ARQN and SEQN shall all be set to zero and ignored during receipt. The HEC LFSR shall be initialized with the same DCI (default check initialization) as for the FHS packet. In the payload header, LLID shall contain the value 10 (start of an L2CAP message or no fragmentation). FLOW shall be set to zero and ignored upon receipt. The length of the payload body (LENGTH) shall be smaller than or equal to 240 bytes. The CRC LFSR shall be initialized with the same DCI as for the FHS packet. The data whitening LFSR shall be initialized with the same value as for the FHS packet.
The payload data has two parts, a significant part followed by a non-significant part. The significant part contains a sequence of data structures as defined in [Vol 3] Part C, Section 8. The non-significant part contains all-zero octets.
The Baseband shall not change any octets in the significant part. When transmitting data, the non-significant part octets may be omitted from the payload.
A device shall store a single extended inquiry response packet. This packet shall be used with all IACs.
Step | Message | Packet Type | Direction | Hopping Sequence | Access Code and Clock |
|---|---|---|---|---|---|
1 | Inquiry | ID | Central to Peripheral | inquiry | inquiry |
2 | Inquiry response | FHS | Peripheral to Central | inquiry response | inquiry |
3 | Extended Inquiry Response | DM1, DM3, DM5, DH1, DH3, DH5 | Peripheral to Central | inquiry response * | inquiry |
* The extended inquiry response packet is sent on the same frequency as the inquiry response (FHS) packet.
8.5. Connection state
In the Connection state, the connection has been established and packets can be sent back and forth, with the exception of Connectionless Peripheral Broadcast mode, in which case packets are only sent from the Central. In both devices, the channel access code (derived from the Central's BD_ADDR), the Central's Bluetooth clock, and the AFH_channel_map are used. Connection state uses the basic or adapted channel hopping sequence.
There are two ways to enter the Connection state. A device can transition from the Page or Page Scan substates to the Connection state or directly from the Standby state to the Connectionless Peripheral Broadcast mode of the Connection state.
If a device enters from the Page or Page Scan substates, the Connection state starts with a POLL packet sent by the Central to verify the switch to the Central’s timing and channel frequency hopping. The Peripheral may respond with a NULL, DM1, or DH1 packet. If the Peripheral does not receive the POLL packet or the Central does not receive the response packet for newconnectionTO number of slots, both devices shall return to Page or Page Scan substate.
The first information packets in the Connection state contain control messages that characterize the link and give more details regarding the devices. These messages are exchanged between the link managers of the devices. For example, they may define the SCO logical transport and the sniff parameters. Then the transfer of user information can start by alternately transmitting and receiving packets.
The Connection state is left through a Detach or Reset command. The Detach command is used if the link has been disconnected in the normal way; all configuration data in the Link Controller shall remain valid. The Reset command is a soft reset of the Link Controller. The functionality of the soft reset is described in [Vol 4] Part E, Section 7.3.2.
In the Connection state, if a device is not going to be nominally present on the channel at all times it may describe its unavailability by using Sniff mode or Hold mode (see Figure 8.7).
If a device enters the Connectionless Peripheral Broadcast mode of the Connection state, the Transmitter (Central) starts by sending packets on the CPB logical transport and the Receiver (Peripheral) starts by receiving packets sent on the CPB logical transport.
 |
8.6. Active mode
In the Active mode, both Central and Peripheral actively participate on the channel. Up to seven Peripherals may be in the Active mode at any given time in a piconet. The Central schedules the transmission based on traffic demands to and from the different Peripherals. In addition, it supports regular transmissions to keep Peripherals synchronized to the channel. Peripherals in the Active mode listen in the Central-to-Peripheral slots for packets. These devices are known as active Peripherals. If an active Peripheral is not addressed, it may sleep until the next new Central transmission. Peripherals can derive the number of slots the Central has reserved for transmission from the TYPE field in the packet header; during this time, the non-addressed Peripherals do not have to listen on the Central-to-Peripheral slots. When a device is participating in multiple piconets it should listen in the Central-to-Peripheral slot for the current piconet. It is recommended that a device not be away from each piconet in which it is participating for more than Tpoll slots. A periodic Central transmission is required to keep the Peripherals synchronized to the channel. Since the Peripherals only need the channel access code to synchronize, any packet type can be used for this purpose.
Only the Peripheral that is addressed by one of its LT_ADDRs (primary or secondary) may return a packet in the next Peripheral-to-Central slot. If no valid packet header is received, the Peripheral may only respond in its reserved SCO or eSCO Peripheral-to-Central slot. In the case of a broadcast message, no Peripheral shall return a packet.
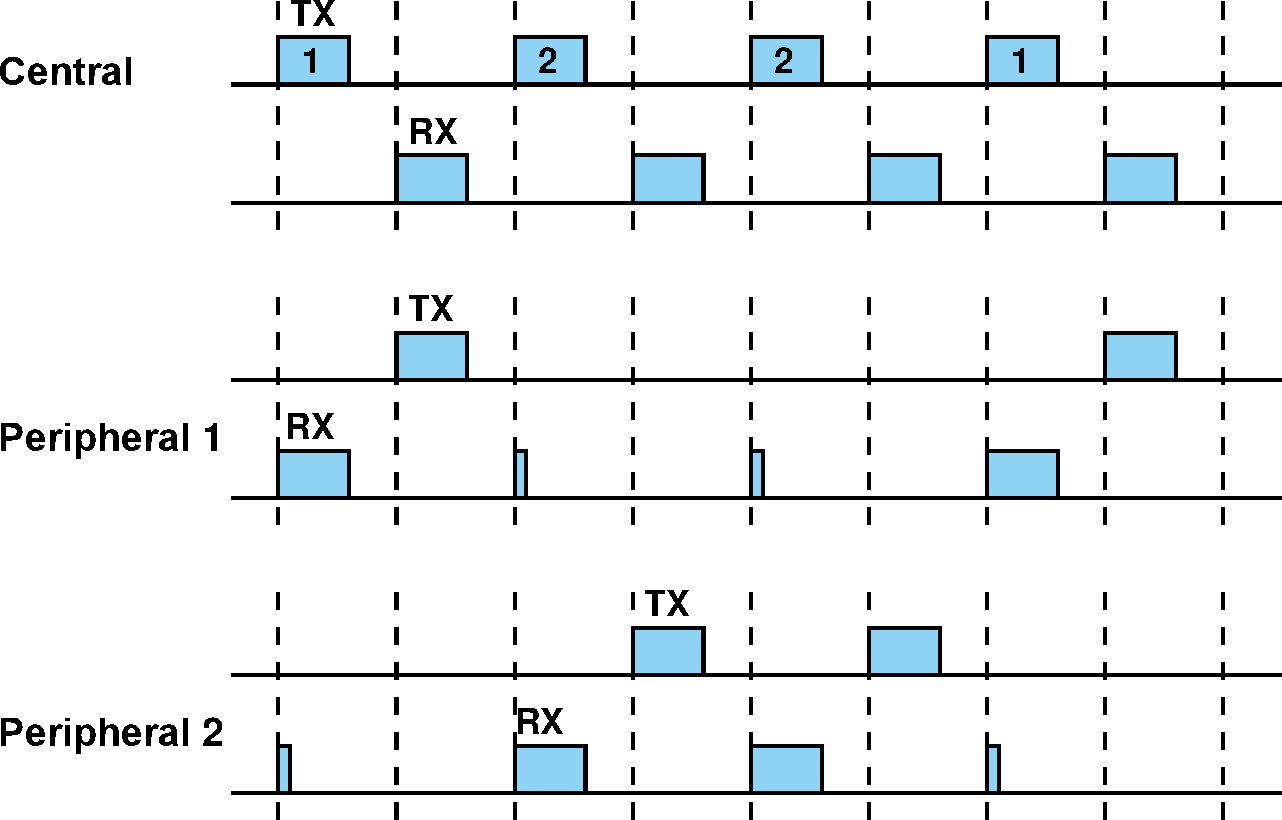
For ACL logical transports the mode selection may be left to real time packet type selections. The packet type table (ptt) in Section 6.5 allows the selection of Basic Rate or Enhanced Data Rate for each of the packet type codes, however; the DM1 packet is available in all packet type tables. ACL traffic over this given physical or logical link shall utilize the packet types in the given column of Table 6.2.
8.6.1. Polling in the Active mode
The Central always has full control over the piconet. Due to the TDD scheme, Peripherals can only communicate with the Central and not other Peripherals. In order to avoid collisions on the ACL logical transport, a Peripheral is only allowed to transmit in the Peripheral-to-Central slot when addressed by the LT_ADDR in the packet header in the preceding Central-to-Peripheral slot. If the LT_ADDR in the preceding slot does not match, or a valid packet header was not received, the Peripheral shall not transmit.
The Central normally attempts to poll a Peripheral's ACL logical transport no less often than once every Tpoll slots. Tpoll is set by the Link Manager (see [Vol 2] Part C, Section 4.1.8).
The Peripheral's ACL logical transport may be polled with any packet type except for FHS and ID. For example, polling during SCO may use HV packets, since the Peripheral may respond to an HV packet with a DM1 packet (see Section 8.6.2).
8.6.2. SCO
The SCO logical transport shall be established by the Central sending a SCO setup message via the LM protocol. This message contains timing parameters including the SCO interval TSCO and the offset DSCO to specify the reserved slots.
In order to prevent clock wrap-around problems, an initialization flag in the SCO setup message indicates whether initialization procedure 1 or 2 is being used. The Peripheral shall apply the initialization method as indicated by the initialization flag. The Central shall use initialization 1 when the MSB of the Central's current clock (CLK27) is 0; it shall use initialization 2 when the MSB of the Central's current clock (CLK27) is 1. The Central-to-Peripheral SCO slots reserved by the Central and the Peripheral shall be initialized on the slots for which the clock satisfies the applicable equation:
The Peripheral-to-Central SCO slots shall directly follow the reserved Central-to-Peripheral SCO slots. After initialization, the clock value CLK(k+1) for the next Central-to-Peripheral SCO slot shall be derived by adding the fixed interval TSCO to the clock value of the current Central-to-Peripheral SCO slot:
The Central will send SCO packets to the Peripheral at regular intervals (the SCO interval TSCO counted in slots) in the reserved Central-to-Peripheral slots. An HV1 packet can carry 1.25 ms of speech at a 64 kb/s rate. An HV1 packet shall therefore be sent every two time slots (TSCO=2). An HV2 packet can carry 2.5 ms of speech at a 64 kb/s rate. An HV2 packet shall therefore be sent every four time slots (TSCO=4). An HV3 packet can carry 3.75 ms of speech at a 64 kb/s rate. An HV3 packet shall therefore be sent every six time slots (TSCO=6).
The Peripheral is allowed to transmit in the slot reserved for its SCO logical transport unless a packet with the correct access code was received in the preceding slot and the LT_ADDR did not address this Peripheral (irrespective of whether or not the HEC was correct). If the correct LT_ADDR was received in the preceding slot but the HEC was incorrect, the Peripheral should not transmit in the reserved SCO slot.
Since the DM1 packet is recognized on the SCO logical transport, it may be sent during the SCO reserved slots if a valid packet header with the primary LT_ADDR is received in the preceding slot. DM1 packets sent during SCO reserved slots shall only be used to send ACL-C data.
The Peripheral shall not transmit anything other than an HV packet in a reserved SCO slot unless it decodes its own Peripheral address in the packet header of the packet in the preceding Central-to-Peripheral transmission slot.
8.6.3. eSCO
The eSCO logical transport is established by sending an eSCO setup message via the LM protocol. This message contains timing parameters including the eSCO interval TeSCO and the offset DeSCO to specify the reserved slots.
To enter eSCO, the Central or Peripheral shall send an eSCO setup message via the LM protocol. This message shall contain the eSCO interval TeSCO and an offset DeSCO. In order to prevent clock wrap-around problems, an initialization flag in the eSCO setup message indicates whether initialization procedure 1 or 2 shall be used. The device sending the eSCO setup message shall use initialization 1 when the MSB of the Central's current clock (CLK27) is 0; it shall use initialization 2 when the MSB of the Central's current clock (CLK27) is 1. The device that receives the eSCO setup message shall apply the initialization method as indicated by the initialization flag. The Central-to-Peripheral eSCO slots reserved by the Central and the Peripheral shall be initialized on the slots for which the clock satisfies the applicable equation:
The Peripheral-to-Central eSCO slots shall directly follow the reserved Central-to-Peripheral eSCO slots. After initialization, the clock value CLK(k+1) for the next Central-to-Peripheral eSCO slot shall be found by adding the fixed interval TeSCO to the clock value of the current Central-to-Peripheral eSCO slot:
When an eSCO logical transport is established, the Central shall assign an additional LT_ADDR to the Peripheral. This provides the eSCO logical transport with an ARQ scheme that is separate from that of the ACL logical transport. All traffic on a particular eSCO logical transport, and only that eSCO traffic, is carried on the eSCO LT_ADDR. The eSCO ARQ scheme uses the ARQN bit in the packet header, and operates similarly to the ARQ scheme on ACL links.
The Central may send a packet in the reserved Central-to-Peripheral slot. The Peripheral may transmit on the eSCO LT_ADDR in the following slot either if it received a packet on the eSCO LT_ADDR in the previous slot, or if it did not receive a valid packet header in the previous slot. When the Central-to-Peripheral packet type is a three-slot packet, the Peripheral’s transmit slot is the fourth slot of the eSCO reserved slots.
A Central shall transmit in an eSCO retransmission window on a given eSCO LT_ADDR only if it addressed that eSCO LT_ADDR or did not transmit any packet in the immediately preceding eSCO reserved slots. A Peripheral shall transmit in an eSCO retransmission window on a given eSCO LT_ADDR only if it received a valid packet header and that LT_ADDR on the eSCO channel in the previous Central-to-Peripheral transmission slot. The Central may transmit on any non-eSCO LT_ADDR in any Central-to-Peripheral transmission slot inside the eSCO retransmission window; if it addresses a Peripheral, that Peripheral may respond on the ACL channel as usual.
The Central shall only transmit on an eSCO LT_ADDR in the retransmission window if there are enough slots left for both the Central and Peripheral packets to complete in the retransmission window. If the Central is transmitting a NULL packet (with ARQN=ACK), then this requires one slot, otherwise it requires enough slots for the Central’s negotiated eSCO packet type plus:
if the Central’s packet has ARQN=NAK, then enough slots for the Peripheral’s negotiated eSCO packet type;
if the Central’s packet has ARQN=ACK, then one slot.
The Central may refrain from transmitting in any slot during the eSCO retransmission window. When there is no data to transmit from Central to Peripheral, either due to the traffic being unidirectional or due to the Central-to-Peripheral packet having been ACK’ed, the Central shall use the POLL packet. When the Central-to-Peripheral packet has been ACK’ed, and the Peripheral-to-Central packet has been correctly received, the Central shall not address the Peripheral on the eSCO LT_ADDR until the next eSCO reserved slot, with the exception that the Central may transmit a NULL packet with ARQN=ACK on the eSCO LT_ADDR. If the Central is transmitting on the eSCO LT_ADDR during a retransmission slot and there is no data to transmit from Peripheral to Central, either due to the traffic being unidirectional or due to the Peripheral-to-Central packet having been ACK'ed, the Peripheral shall use NULL packets. eSCO traffic should be given priority over ACL traffic in the retransmission window.
Figure 8.9 shows the eSCO window when single slot packets are used.
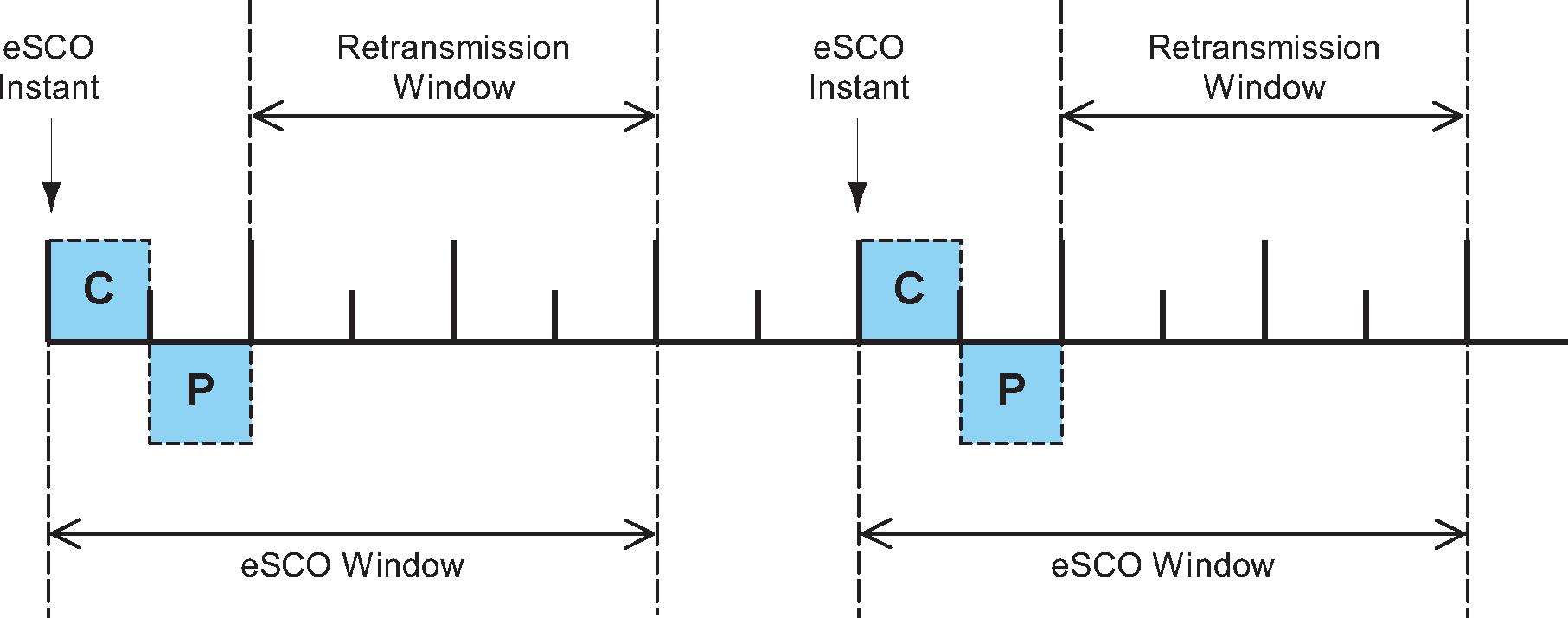
When multi-slot packets are used in either direction of the eSCO logical transport, the first transmission continues into the following slots. The retransmission window in this case starts the slot after the end of the Peripheral-to-Central packet, i.e. two, four or six slots immediately following the eSCO instant are reserved and should not be used for other traffic. Figure 8.10 shows the eSCO window when multi-slot packets are used in one direction and single-slot packets are used in the other direction.
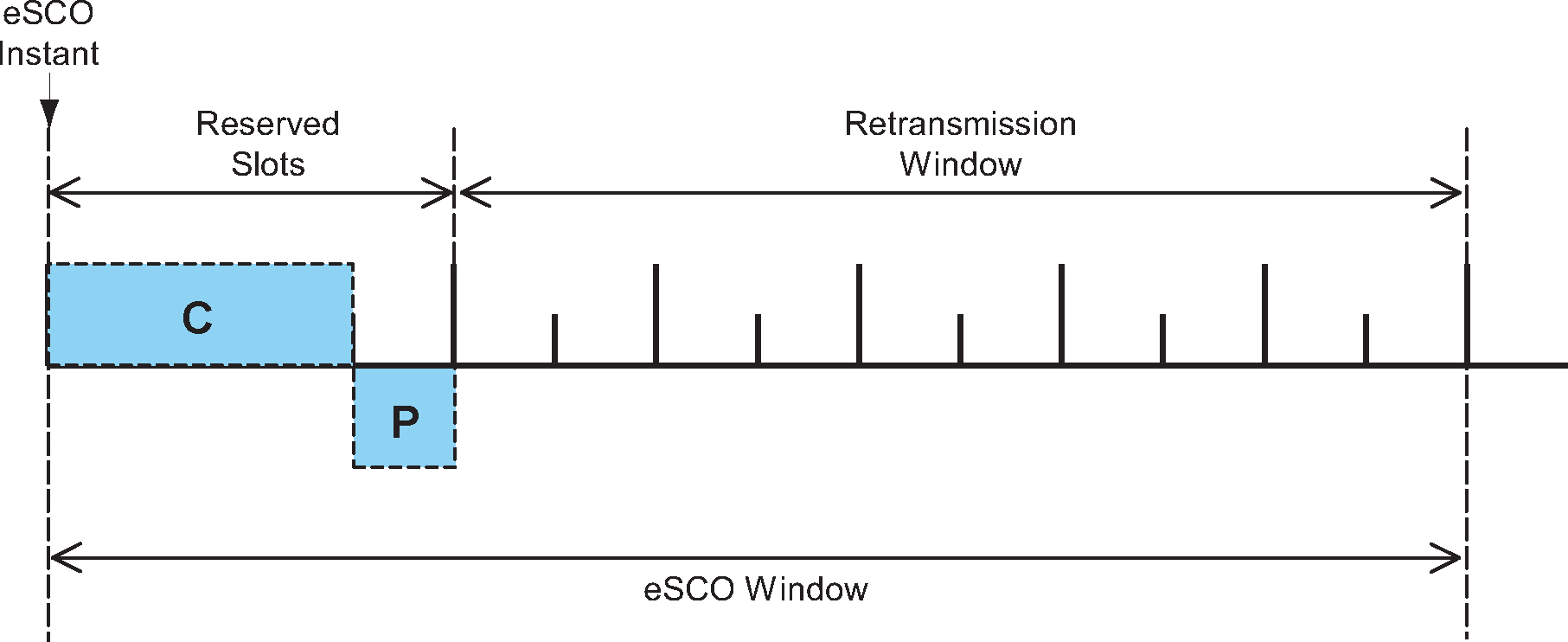
eSCO windows may overlap on the Central, but shall not overlap on an individual Peripheral.
In the reserved slots both Central and Peripheral shall only listen and transmit at their allocated slots at the first transmission time of each eSCO window. Intermittent lapses due to, for instance, time-critical signaling during connection establishment are allowed. Both Central and Peripheral may refrain from sending data and may use instead POLL and NULL packets respectively. When the Central transmits a POLL packet instead of an eSCO 3-slot packet, or the Peripheral does not receive anything in the reserved Central-to-Peripheral transmission slot, it shall start any transmission in the same slot as if the Central had transmitted the negotiated packet type. For example, if the Central had negotiated an EV5 packet the Peripheral would transmit three slots later. If the Central does not receive a Peripheral transmission in response to an eSCO packet it causes an implicit NAK of the packet in question. The listening requirements for the Peripheral during the retransmission window are the same as for an active ACL logical transport.
8.6.4. Broadcast scheme
The Central of the piconet can broadcast messages to all Peripherals on the APB logical transport. An APB broadcast packet shall have an LT_ADDR set to all zero. If a new broadcast message carries APB-U data, it may be fragmented in the same way as ACL packets. Therefore it shall start with a packet carrying the start of L2CAP message indication (LLID=0b10) and may be followed by packets carrying the continuation of L2CAP message indication (LLID=0b01). If a new broadcast message carries APB-C data, it shall not be fragmented and shall consist of a single packet carrying the LMP message indication (LLID=0b11). In either case, the Central may carry out a number of retransmissions of each of these packets to increase the probability for error-free delivery; see also Section 7.6.5.
A broadcast packet shall never be acknowledged by the Baseband.
The Broadcast LT_ADDR shall use a ptt=0.
8.6.5. Role switch
There are several occasions when a role switch is used:
A role switch is necessary in order to make a paging device a Peripheral when joining an existing piconet, since by definition the paging device is initially Central of a piconet involving the pager (Central) and the paged (Peripheral) device.
A role switch is necessary in order for a Peripheral in an existing piconet to set up a new piconet with itself as Central and the original piconet Central as Peripheral. If the original piconet had more than one Peripheral, then this implies a double role for the original piconet Central; it becomes a Peripheral in the new piconet while still maintaining the original piconet as Central.
Prior to the role switch, encryption if present, shall be paused or disabled in the old piconet. A role switch shall not be performed if the physical link is in Sniff or Hold mode, or has any synchronous logical transports.
For the Central and Peripheral involved in the role switch, the switch results in a reversal of their TX and RX timing: a TDD switch. Additionally, since the piconet parameters are derived from the Bluetooth Device Address and clock of the Central, a role switch inherently involves a redefinition of the piconet as well: a piconet switch. The new piconet's parameters shall be derived from the former Peripheral's device address and clock.
Assume device A is to become Central; device B was the former Central. Then there are two alternatives: either the Peripheral initiates the role switch or the Central initiates the role switch. These alternatives are described in Link Manager Protocol, [Vol 2] Part C, Section 4.4.2. The Baseband procedure is the same regardless of which alternative is used.
To begin the role switch, A and B shall perform a TDD switch using the former hopping scheme (still using the Bluetooth Device Address and clock of device B), so there is no piconet switch yet. The slot offset information sent by A shall not be used yet; it is used when both devices have switched to the new piconet and device B is positioning its correlation window. Device A now becomes the Central, device B the Peripheral.
At the moment of the TDD switch, both devices A and B shall start a timer with a time out of newconnectionTO. The timer shall be stopped in B as soon as it receives an FHS packet from A on the TDD-switched channel. The timer shall be stopped in A as soon as it receives an ID packet from B. If the newconnectionTO expires, A and B shall return to the old piconet timing and AFH state, taking their old roles of Peripheral and Central respectively. The FHS packet shall be sent by A using the "old" piconet parameters. The LT_ADDR in the FHS packet header shall be the former LT_ADDR used by device A. The LT_ADDR carried in the FHS payload shall be the new LT_ADDR intended for device B when operating on the new piconet. After the FHS acknowledgment, which is the ID packet and shall be sent by B on the old hopping sequence, both A and B shall use the new channel parameters of the new piconet as indicated by the FHS with the sequence selection set to basic channel hopping sequence. If the new Central A has physical links that are AFH enabled, following the piconet switch the new Central is responsible for controlling the AFH operational mode of its new Peripheral B.
Since the old and new Centrals' clocks are synchronized, the clock information sent in the FHS payload shall indicate the new Central's clock at the beginning of the FHS packet transmission. Furthermore, the 1.25 ms resolution of the clock information given in the FHS packet is not sufficient for aligning the slot boundaries of the two piconets. The slot-offset information in the LMP message previously sent by device A shall be used to provide more accurate timing information. The slot offset indicates the delay between the start of the Central-to-Peripheral slots of the old and new piconet channels. This timing information ranges from 0 to 1249 μs with a resolution of 1 μs. It shall be used together with the clock information in the FHS packet to accurately position the correlation window when switching to the new Central's timing after acknowledgment of the FHS packet.
After reception of the FHS packet acknowledgment, the new Central A shall switch to its own timing with the sequence selection set to the basic channel hopping sequence and shall send a POLL packet to verify the switch. Both A and B shall start a new timer with a time out of newconnectionTO on FHS packet acknowledgment. The start of this timer shall be aligned with the beginning of the first Central TX slot boundary of the new piconet, following the FHS packet acknowledgment. B shall stop the timer when the POLL packet is received; A shall stop the timer when the POLL packet is acknowledged. The Peripheral B shall respond with a NULL, DM1, or DH1 packet to acknowledge the POLL. Any pending AFH_Instant shall be cancelled once the POLL packet has been received by the Peripheral. If no response is received, A shall re-send the POLL packet until newconnectionTO is reached. If this timer expires, both A and B shall return to the old piconet timing with the old roles: B as Central and A as Peripheral. Expiry of the timer shall also restore the state associated with AFH (including any pending AFH_Instant), Channel Quality Driven Data Rate (CQDDR, Link Manager Protocol [Vol 2] Part C, Section 4.1.7) and power control (Link Manager Protocol [Vol 2] Part C, Section 4.1.3). The role switch procedure may then restart from the TDD switch. Aligning the timer with TX boundaries of the new piconet ensures that no device returns to the old piconet timing in the middle of a Central RX slot.
The messaging during a successful role switch is summarized in Table 8.6.
Step | Message or Packet Type | Direction | Central |
|---|---|---|---|
1 | LMP_ACCEPTED | Responder → Initiator | B |
2 | FHS | A → B | B |
3 | ID | B → A | B |
4 | POLL | A → B | A |
5 | NULL/DM1/DH1 | B → A | A |
After the role switch the ACL logical transport is reinitialized as if it were a new connection. For example, the SEQN of the first data packet containing a CRC on the new piconet channel shall be set according to the rules in Section 7.6.2.
8.6.6. Scatternet
Multiple piconets can cover the same area. Since each piconet has a different Central, the piconets hop independently, each with their own hopping sequence and phase as determined by the respective Central. In addition, the packets carried on the channels are preceded by different channel access codes as determined by the Centrals’ device addresses. As more piconets are added, the probability of collisions increases; a graceful degradation of performance results as is common in frequency-hopping spread spectrum systems.
If multiple piconets cover the same area, a device can participate in two or more overlaying piconets by applying time multiplexing. To participate on the proper channel, it shall use the associated Central’s device address and proper clock offset to obtain the correct phase. A device can act as a Peripheral in several piconets, but only as a Central in a single piconet: since two piconets with the same Central are synchronized and use the same hopping sequence, they are one and the same piconet. A group of piconets in which connections exist between different piconets is called a scatternet.
A Central or Peripheral can become a Peripheral in another piconet by being paged by the Central of this other piconet. On the other hand, a device participating in one piconet can page the Central or Peripheral of another piconet. Since the paging device always starts out as Central, a role switch is required if a Peripheral role is desired. This is described in Section 8.6.5.
8.6.6.1. Inter-piconet communications
Time multiplexing must be used to switch between piconets. Devices may achieve the time multiplexing necessary to implement scatternet by using Sniff mode or by remaining in an active ACL connection. For an ACL connection in piconets where the device is a Peripheral in the Connection state, it may choose not to listen in every Central slot. In this case it should be recognized that the quality of service on this link can degrade abruptly if the Peripheral is not present enough to match up with the Central polling that Peripheral. Similarly, in piconets where the device is Central it may choose not to transmit in every Central slot. In this case it is important to honor Tpoll as much as possible. Devices in Sniff mode could have sufficient time to visit another piconet in between sniff slots. When the device is a Peripheral using Sniff mode and there are not sufficient idle slots, the device may choose to not listen to all Central transmission slots in the sniff_attempts period or during the subsequent sniff_timeout period. A Central is not required to transmit during sniff slots and therefore has flexibility for scatternet. If SCO or eSCO links are established, other piconets shall only be visited in the non-reserved slots in between reserved slots. This is only possible if there is a single SCO logical transport using HV3 packets or eSCO links where at least four slots remain in between the reserved slots. Since the multiple piconets are not synchronized, guard time must be left to account for misalignment. This means that only 2 slots can effectively be used to visit another piconet in between the HV3 packets.
Since the clocks of two Centrals of different piconets are not synchronized, a Peripheral participating in two piconets shall maintain two offsets that, added to its own native clock, create the two Centrals' clocks. Since the two Centrals' clocks drift independently, the Peripheral must regularly update the offsets in order to keep synchronization to both Centrals.
8.6.7. Hop sequence switching
Hop sequence adaptation is controlled by the Central and can be set to either enabled or disabled. Once enabled, hop sequence adaptation shall apply to all logical transports on a physical link. Once enabled, the Central may periodically update the set of used and unused channels as well as disable hop sequence adaptation on a physical link. When a Central has multiple physical links the state of each link is independent of all other physical links.
When hop sequence adaptation is enabled, the sequence selection hop selection kernel input is set to adapted channel hopping sequence and the AFH_channel_map input is set to the appropriate set of used and unused channels. Additionally, the same channel mechanism shall be used. When hop sequence adaptation is enabled with all channels used this is known as AHS(79).
When hop sequence adaptation is disabled, the sequence selection input of the hop selection kernel is set to basic channel hopping sequence (the AFH_channel_map input is unused in this case) and the same channel mechanism shall not be used.
The hop sequence adaptation state shall be changed when the Central sends the LMP_SET_AFH PDU and a Baseband acknowledgment is received. When the Baseband acknowledgment is received prior to the hop sequence switch instant, AFH_Instant, (See Link Manager Protocol [Vol 2] Part C, Section 4.1.4) the hop sequence proceeds as shown in Figure 8.11.
 |
When the Baseband acknowledgment is not received prior to the AFH_Instant the Central shall use a recovery hop sequence for the Peripheral(s) that did not respond with an acknowledgment (this may be because the Peripheral did not hear the Central’s transmission or the Central did not hear the Peripheral’s transmission). When hop sequence adaptation is being enabled or disabled the recovery sequence shall be the AFH_channel_map specified in the LMP_SET_AFH PDU. When the AFH_channel_map is being updated the Central shall choose a recovery sequence that includes all of the RF channels marked as used in either the old or new AFH_channel_map, e.g. AHS(79). Once the Baseband acknowledgment is received the Central shall use the AFH_channel_map in the LMP_SET_AFH PDU starting with the next transmission to the Peripheral. See Figure 8.12.
 |
When the AFH_Instant occurs during a multi-slot packet transmitted by the Central, the Peripheral shall use the same hopping sequence parameters as the Central used at the start of the multi-slot packet. An example of this is shown in Figure 8.13. In this figure the basic channel hopping sequence is designated f. The first adapted channel hopping sequence is designated with f', and the second adapted channel hopping sequence is designated f''.

8.6.8. Channel classification and channel map selection
RF channels are classified as being unknown, bad or good. These classifications are determined individually by the Central and Peripherals based on local information (e.g. active or passive channel assessment methods or from the Host via HCI). Information received from other devices via LMP (for example, an AFH_channel_map from a Central or a channel classification report from a Peripheral) shall not be included in a device’s channel classification.
The three possible channel classifications shall be as defined in Table 8.7.
Classification | Definition |
|---|---|
unknown | A channel shall be classified as unknown if the channel assessment measurements are insufficient to reliably classify the channel, and the channel is not marked as bad in the most recent HCI_ Set_AFH_Host_Channel_Classification command. |
bad | A channel may be classified as bad if an ACL or synchronous throughput failure measure associated with it has exceeded a threshold (defined by the particular channel assessment algorithm employed). A channel may also be classified as bad if an interference-level measure associated with it, determining the interference level that the link poses upon other systems in the vicinity, has exceeded a threshold (defined by the particular channel assessment algorithm employed). A channel shall be classified as bad when it is marked as bad in the most recent HCI_ Set_AFH_Host_Channel_Classification command. |
good | A channel shall be classified as good if it is not either unknown or bad. |
A Central with AFH enabled physical links shall determine an AFH_channel_map for each such link (two or more links may use the same map) based on any combination of the following information:
Channel classification from local measurements (e.g. active or passive channel assessment in the Controller), if supported and enabled. The Host may enable or disable local measurements using the HCI_ Write_AFH_Channel_Assessment_Mode command, defined in the HCI Functional Specification [Vol 4] Part E, Section 7.3.54 if HCI is present.
Channel classification information from the Host using the HCI_ Set_AFH_Host_Channel_Classification command, defined in the HCI Functional Specification [Vol 4] Part E, Section 7.3.46 if HCI is present. Channels classified as bad in the most recent AFH_Host_Channel_Classification shall be marked as unused in the AFH_channel_map.
Channel classification reports received from Peripherals in LMP_CHANNEL_CLASSIFICATION PDUs, defined in the LMP Specification [Vol 2] Part C, Section 4.1.5.
The algorithm used by the Central to combine these information sources and generate the AFH_channel_map is not defined in the specification and will be implementation specific. At no time shall the number of channels used be less than Nmin, defined in Section 2.3.1.
If a Central determines that all channels should be used, it may keep AFH operation enabled using an AFH_channel_map of 79 used channels, i.e., AHS(79).
For all devices that support the Synchronization Train substate (see Section 8.11.2), the RF channel indices used for the Synchronization Train (see Section 2.6.4.8) shall be marked as unused in the AFH_channel_map for all logical links.
8.6.9. Power management
Features are provided to allow low-power operation. These features are both at the microscopic level when handling the packets, and at the macroscopic level when using certain operation modes.
8.6.9.1. Packet handling
In order to minimize power consumption, packet handling is minimized both at TX and RX sides. At the TX side, power is minimized by only sending useful data. This means that if only link control information needs to be exchanged, NULL packets may be used. No transmission is required if there is no link control information to be sent, or if the transmission would only involve a NAK (NAK is implicit on no reply). If there is data to be sent, the payload length shall be adapted in order to send only the valid data bytes. At the RX side, packet processing takes place in different steps. If no valid access code is found in the search window, the transceiver may return to sleep. If an access code is found, the receiver device shall start to process the packet header. If the HEC fails, the device may return to sleep after the packet header. A valid header indicates if a payload will follow and how many slots are involved.
8.6.9.2. Slot occupancy
As was described in Section 6.5, the packet type indicates how many slots a packet may occupy. A Peripheral not addressed in the packet header may go to sleep for the remaining slots the packet occupies. This can be read from the TYPE code.
8.6.9.3. Recommendations for low-power operation
The most common and flexible method for reducing power consumption is the use of Sniff mode. Hold mode can also be used by repeated negotiation of hold periods.
8.6.9.4. Enhanced Data Rate
Enhanced Data Rate provides power saving because of the ability to send a given amount of data in either fewer packets or with the same (or similar) number of packets but with shorter payloads.
8.6.10. Piconet clock adjustment
A Central may adjust the piconet clock during the existence of a piconet using two mechanisms: Coarse Clock Adjustment and Clock Dragging. Both mechanisms may be used within the same piconet.
8.6.10.1. Coarse clock adjustment
The Central carries out a coarse clock adjustment by selecting an adjustment instant (clk_adj_instant), which shall be a Central-to-Peripheral slot, and the amount of the adjustment, and then broadcasting these parameters to all Peripherals by sending LMP_CLK_ADJ (see [Vol 2] Part C, Section 4.1.14.1). The amount of the adjustment is specified as two values: clk_adj_slots, which is the change in the value of CLK[27:1] at the clk_adj_instant, and clk_adj_us, which is the number of microseconds between the start of a Central slot in the old clock (CLKold) and in the new clock (CLKnew) domains.
The Central shall provide the opportunity for each Peripheral to acknowledge the adjustment with LMP_CLK_ADJ_ACK (see [Vol 2] Part C, Section 4.1.14.1). If the Central receives any other packet than LMP_CLK_ADJ_ACK with the current clk_adj_id, it should poll the Peripheral more times until the expected acknowledgment is received or the Peripheral responds with a NULL packet. If any Peripheral does not acknowledge the adjustment, the Central shall start the Coarse Clock Adjustment Recovery Mode (see Section 8.6.10.2).
When the clk_adj_instant occurs, the Central will add (clk_adj_slots * 625 + clk_adj_us) µs to time_base_offset and the Peripheral(s) will add the same amount to peripheral_clock_offset. If the clk_adj_instant occurs during a multi-slot packet the adjustment is delayed until the start of the following Central-to-Peripheral slot. If a role switch is successful prior to the clk_adj_instant, the pending coarse clock adjustment shall be discarded. The effect of the adjustment is that devices will use the new clock domain starting at clk_adj_instant.
Figure 8.14 shows an example of a positive clock adjustment. In this example the clk_adj_instant is set to slot 12 (which is in the old clock domain), clk_adj_slots is set to 6 and clk_adj_us is set to 400. Time is moved forward clk_adj_slots * 625 + clk_adj_us = 6 * 625 + 400 = 4150 µs. The initial slot in the new clock domain is at CLKnew[27:1] = clk_adj_instant + clk_adj_slots = 12 + 6 = 18. This is an even value so the first slot is a Central-to-Peripheral slot. A positive clk_adj_us means that the first slot is assumed to have started clk_adj_us before the clk_adj_instant, and hence only 625 – clk_adj_us = 225 µs remains after the instant. Since transmissions cannot be started part way through a slot, this partial slot is unusable. The first complete slot after the clk_adj_instant is a Peripheral-to-Central slot which can be used, for example, for eSCO. If clk_adj_slots had been an odd number, the first complete slot would have been a Central-to-Peripheral slot. The first complete Central-to-Peripheral slot in this example happens at CLKnew[27:1] = 20.

Figure 8.15 shows an example of a negative clock adjustment. In this example the clk_adj_instant is again set to slot 12, clk_adj_slots is set to 0 and clk_adj_us is set to –400. Time is moved by clk_adj_slots * 625 + clk_adj_us = 0 * 625 + (–400) = –400 µs, which is 400 µs backwards. The initial slot in the CLKnew domain is at CLKnew[27:1] = clk_adj_instant + clk_adj_slots = 12 + 0 = 12. This is an even value so the first slot is a Central-to-Peripheral slot. A negative clk_adj_us means that the first slot in the CLKnew domain starts clk_adj_us after clk_adj_instant. The time between the first slot in the CLKnew domain and clk_adj_instant (in this case 400 µs) is effectively a continuation of the previous slot, even if its number changes, and hence is unusable. (This is the case whenever clk_adj_us is negative, even when clk_adj_slots is non-zero.)
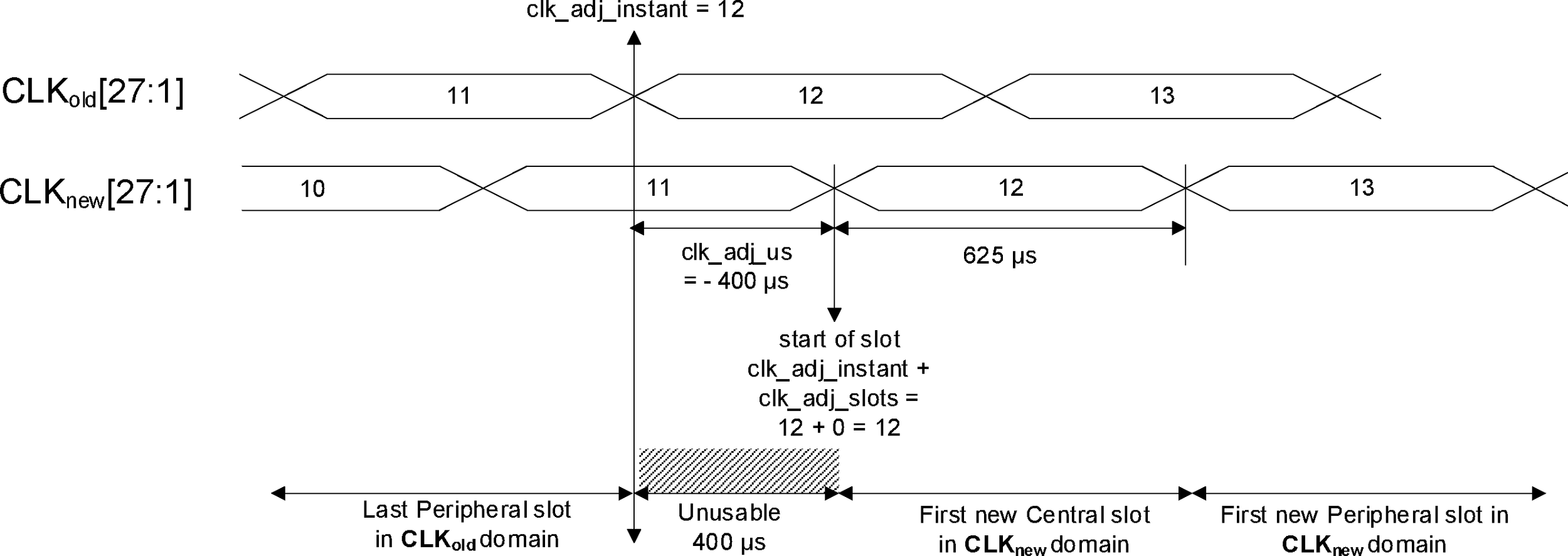
If clk_adj_us is zero then the adjustment alters the slot numbering but not the actual times at which slots start. Therefore all slots remain available for use, though if clk_adj_slots is odd then there will be two consecutive Peripheral-to-Central slots.
8.6.10.2. Coarse Clock Adjustment Recovery mode
In Coarse Clock Adjustment Recovery Mode, the Central enters the Synchronization Train substate (see Section 8.11.2). The Central should remain in this substate and transmit synchronization train packets until all Peripherals have acknowledged the adjustment with the LMP_CLK_ADJ_ACK PDU, or link supervision timeout has expired for the last unresponsive Peripheral. The Central may cancel Coarse Clock Adjustment Recovery Mode to initiate another coarse clock adjustment or for any other reason. During Coarse Clock Adjustment Recovery Mode the Central shall continue broadcasting LMP_CLK_ADJ PDUs (see [Vol 2] Part C, Section 4.1.14.1).
When a Peripheral does not detect any transmissions from its Central it may enter the Synchronization Scan substate (see Section 8.11.1) and scan for synchronization train packets as defined in Section 2.7. TSync_Scan_Window should be set large enough to enable reception of at least one synchronization train packet. A Peripheral that could have lost its connection to the Central due to coarse clock adjustment should prioritize synchronization scan.
A Peripheral that receives a Synchronization Train packet with the BD_ADDR of its Central shall change the value of peripheral_clock_offset to make CLK correspond to the contents of the packet and then exit the Synchronization Scan substate. If the new clock is in the range CLKOLD–LSTO to CLKOLD (where LSTO is the link supervision timeout period), then this shall be treated as a negative change. In this case, the Peripheral shall not transmit any packet and shall ignore all received directed packets until the value of CLK, after being changed, is strictly greater than the value of CLK the last time it transmitted or received (as appropriate) a packet. If the new clock is outside this range then this shall be treated as a positive change (and thus might involve a clock wrap).
8.6.10.3. Clock Dragging
Clock Dragging means that the Central periodically adjusts its time_base_offset (see Section 2.2.4) until a desired time adjustment has been accomplished.
Each single adjustment shall be performed by a directed packet from the Central to each Peripheral and a response (e.g., Baseband acknowledgment) from each Peripheral. If a Peripheral does not respond, the Central shall suspend its updating of time_base_offset (but should continue to poll that Peripheral) at least until each Peripheral has either responded or has failed to respond for at least CLK_adj_dragTO. In case several Peripherals fail to respond, the Central should ensure that each of the failing Peripherals gets at least one CLK_adj_dragTO to respond (these may be concurrent for multiple Peripherals). The Central need not allow more than one suspension of CLK_adj_dragTO for any given Peripheral during a link supervision timeout for that Peripheral.
A single adjustment shall be less than or equal to 3 µs. Within any period of 125 ms, the total adjustment in a single direction shall be less than or equal to 5 µs.
Note
Note: These requirements apply to the changes to time_base_offset and are applied irrespective of the accuracy of the Central's reference clock (see Section 1.1). This means that Peripherals may observe a change in CLK greater than 20ppm.
If a Central is performing Clock Dragging when it initiates a Coarse Clock Adjustment, a new Clock Dragging, or a sequence containing an instant or timing control flags, or receives a request from a Peripheral to initiate such a sequence, it shall abort the current Clock Dragging before processing the new request or carrying out the sequence. If the Central has suspended clock dragging during CLK_adj_dragTO, it shall reject new requests until the timeout period expires or the timeout is cancelled because all of the Peripherals have responded.
8.6.11. Slot Availability Mask (SAM)
Slot Availability Mask (SAM) allows two Bluetooth devices to indicate to each other the availability of their time slots for transmission and reception. From the Baseband point of view, SAM provides a map - the SAM slot map - which marks the availability of Bluetooth slots. The availability arises from either external conditions (e.g., MWS coexistence) or internal conditions (e.g., topology management for scatternets). The SAM slot map marks each slot using one of four type codes defined in [Vol 2] Part C, Section 5.2 and repeated for convenience in Table 8.8.
Slot type code | Meaning |
|---|---|
0 | The slot is not available for either transmission or reception |
1 | The slot is available for transmission but not reception |
2 | The slot is available for reception but not transmission |
3 | The slot is available for both transmission and reception |
Note
Note: A Central may mark Central-to-Peripheral slots available for reception and Peripheral-to-Central slots available for transmission, because such slots may be used in this way for multi-slot packets; similarly for a Peripheral. A SAM slot map with all slots set to type 3 is equivalent to not using SAM and simply performing normal scheduling.
Figure 8.16 shows an example of a SAM slot map. The Central-to-Peripheral slots are labeled with the letter 'C' and Peripheral-to-Central slots with the letter 'P'.

A SAM slot map has a finite length and is repeated indefinitely until changed by the associated LMP procedures. SAM anchor points are spaced regularly with an interval of TSAM, in units of slots. Between adjacent SAM anchor points, the slot map indicates when the device is able to transmit and receive. The SAM slot map is effectively repeated every TSAM until it is changed.
The SAM interval TSAM is further divided into NSAM_SM sub-intervals of equal length, TSAM_SM, such that TSAM = TSAM_SM * NSAM_SM. TSAM_SM shall be an even integer so as to contain TX/RX slot pairs.
The words "SAM submap" (or simply "submap" when there is no ambiguity from the context) will be used to denote a sub-interval of TSAM_SM slots. Each submap is assigned one of the four usage types defined in [Vol 2] Part C, Section 5.2 and repeated for convenience in Table 8.9.
Submaptype code | Meaning |
|---|---|
0 | Each slot is individually available or unavailable as configured. Slots may have different availabilities for transmission and reception. |
1 | All slots are available for transmission and reception. |
2 | All slots are unavailable for transmission and reception. |
3 | Reserved for future use |
The SAM facilities specify each SAM slot map at the submap granularity. Figure 8.17 shows an example of a SAM slot map in terms of submaps in the local device. Each box represents a sub-interval of TSAM_SM slots, with the label on the box indicating the type of the submap.
At the submap level of granularity, transmit and receive are handled identically; the difference will only appear inside submaps with type 0.
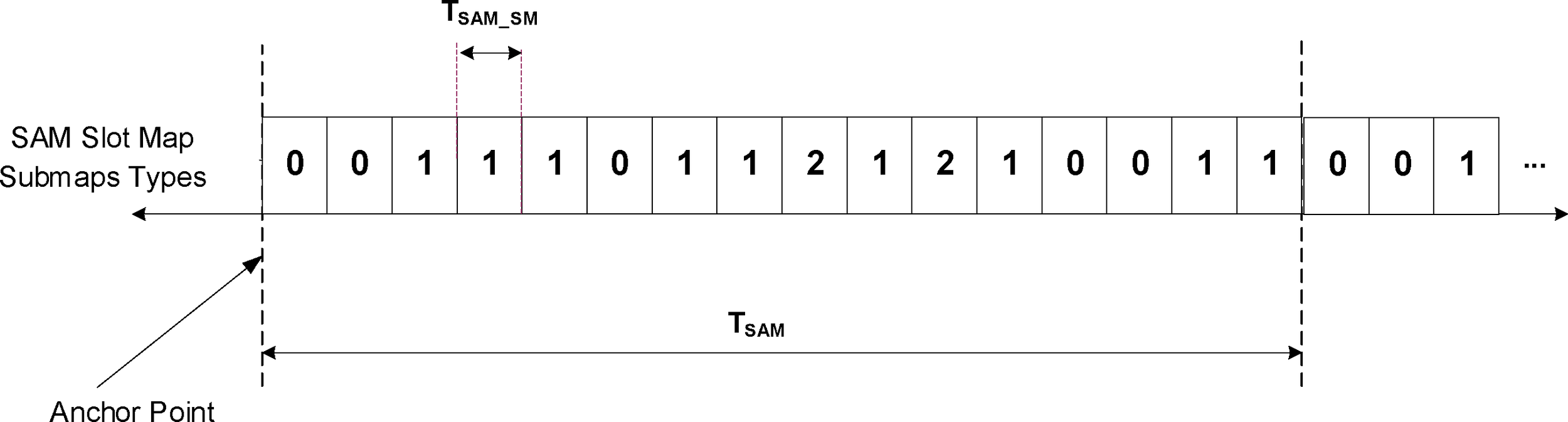
In addition to the SAM slot maps, the Controller also maintains a single "SAM type 0 submap" that is used to specify the availability of individual slots for those submaps shown as having type 0. The Controller then combines the SAM slot map at submap granularity with the first TSAM_SM entries of the type 0 submap to generate the effective maps. Figure 8.18 shows a SAM slot map and a SAM type 0 submap together with the resulting effective map.

Figure 8.19 shows an example of a SAM type 0 submap for a collocated MWS.
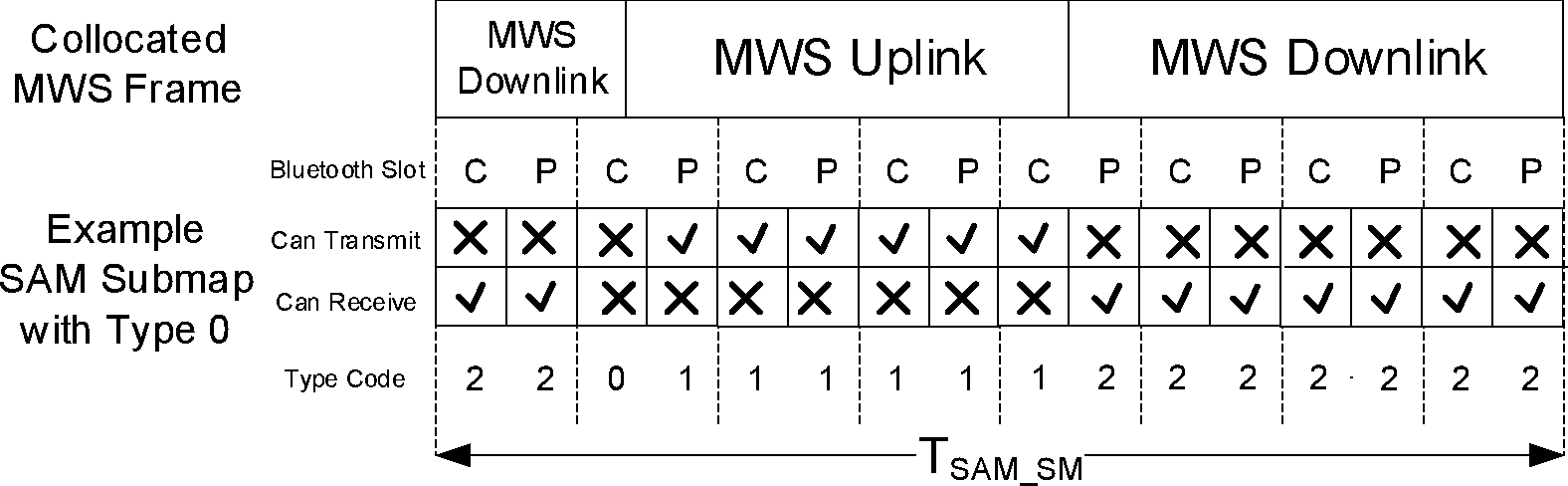
The assumption in the example is that, in order to prevent mutual interference between Bluetooth and MWS radios, Bluetooth transmissions are not available during MWS downlink durations and Bluetooth reception is not available during MWS uplink durations. The MWS frame is 10 ms long and the SAM type 0 submap needs to have the same length, so TSAM_SM is 16.
Figure 8.20 shows another example of a collocated Bluetooth device with a low traffic load in the MWS Uplink. In this case, the implementation chooses to mark the MWS Uplink portion available for both TX and RX, because there is a good chance that it can receive Central packets and respond to them without interference from MWS.
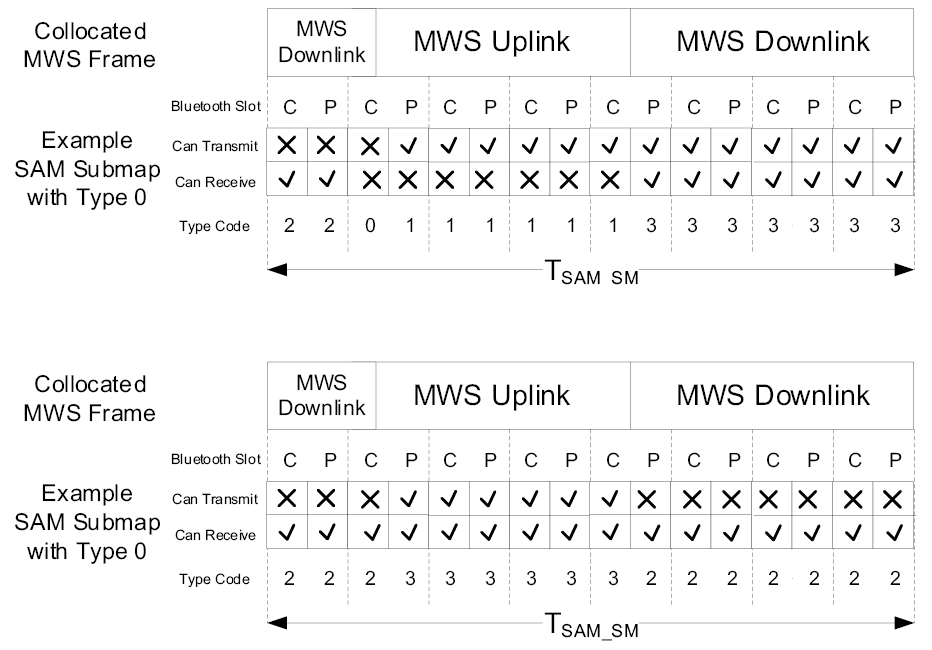
SAM allows each device to send its local slot availability to the other, in which case the availability of slots depends on the combined slot maps. The scheduling recommendations for such a SAM slot map are described in Section 8.6.11.2.
A device that supports the SAM feature shall be capable of storing three distinct SAM slot maps from each connected remote device. A remote device can only define one type 0 submap, which can be referenced by any of its defined SAM slot maps. The remote device may redefine its type 0 submap at any time.
8.6.11.1. SAM anchor point
SAM slot maps are periodic, defined by an interval TSAM and an offset DSAM. Figure 8.21 shows an example of SAM slot maps designed to correspond to periodic MWS active and inactivity cycles.
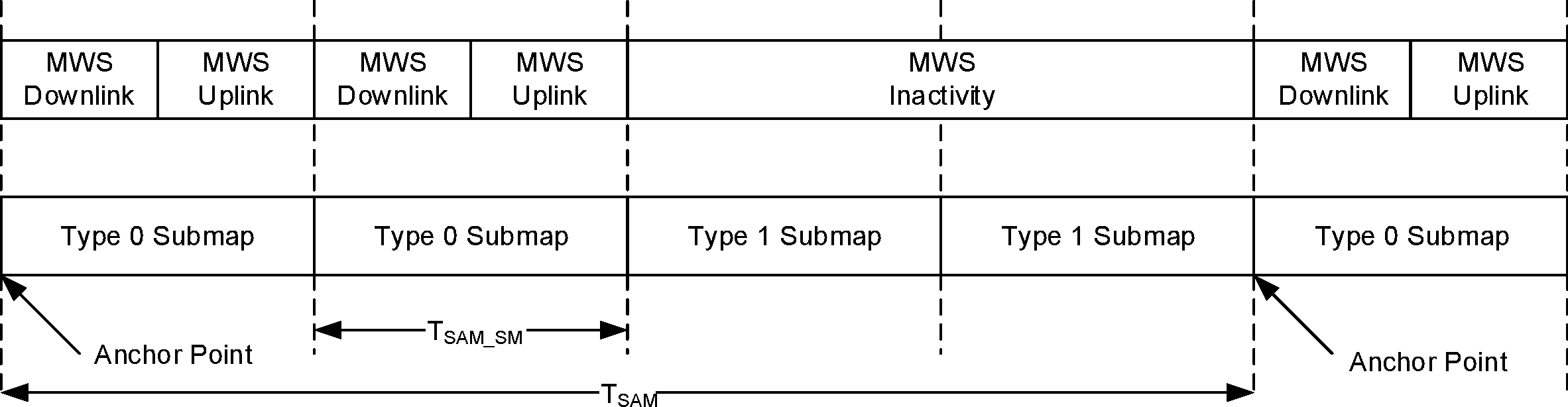
SAM anchor points are the start points of the first slot in the SAM slot maps. SAM anchor points are computed from TSAM and DSAM using the Central's current clock, which is known to both devices. The first SAM anchor point is indicated by SAM_Instant. In order to prevent problems caused by the clock wrap-around, the LMP message carries an additional timing control flag, which indicates whether initialization procedure 1 or 2 shall be used. The initiating device shall use initialization 1 when the MSB of the Central's current clock (CLK27) is 0; it shall use initialization 2 when the MSB of the Central's current clock (CLK27) is 1. The responding device shall apply the initialization method indicated by the initialization flag. The SAM anchor points shall be initialized on the slots for which the clock satisfies the applicable equations:
After initialization, the clock value CLK(k+1) for the next SAM anchor point can be found by adding the fixed interval TSAM to the clock value of the current anchor point:
The SAM anchor point shall be a Central-to-Peripheral slot. As a corollary, the first slot of every SAM submap is also a Central-to-Peripheral slot.
8.6.11.2. SAM scheduling
SAM enables each device to send its local slot availability to the other. The scheduler in the Bluetooth Controller should consider the SAM slot maps from both local and remote devices for packet scheduling. The only effect of using the SAM information is to restrict a device's transmission and reception opportunities.
For all ACL packets and for eSCO packets in the retransmission window:
The Central should only transmit a packet if the required Central-to-Peripheral slots are marked as available for transmission in the Central's SAM slot map and available for reception in the Peripheral's SAM slot map.
The Peripheral should only transmit a packet if the required slots are marked as available for reception in the Central's SAM slot map and available for transmission in the Peripheral's SAM slot map.
The Peripheral may choose not to listen to the Central in Central-to-Peripheral slots that are marked either unavailable for transmission in the Central’s SAM slot map or unavailable for reception in the Peripheral’s SAM slot map.
For all ACL packets, the Central should only transmit a packet if the slot immediately following the Central's packet is marked as available for transmission in the Peripheral's SAM slot map and available for reception in the Central's SAM slot map.
For eSCO packets in the retransmission window, the Central should only transmit a packet if either:
the slot immediately following the Central's packet is marked as available for transmission in the Peripheral's SAM slot map and available for reception in the Central's SAM slot map;
this is the last opportunity for the Central to transmit this packet in this retransmission window; or
for all subsequent Central-to-Peripheral slots in the same retransmission window that provide sufficient remaining slots for the Central to transmit the same packet, the rules in this section state that the Central should not transmit the packet.
In SCO and eSCO reserved slots, either the Central or the Peripheral may choose not to transmit a SCO or eSCO packet unless the required slots are marked both as available for transmission in the local SAM slot map and available for reception in the remote SAM slot map.
Figure 8.22 below illustrates possible scheduling results with combined SAM slot maps from Central and Peripheral.

8.7. Sniff mode
In Sniff mode, the duty cycle of the Peripheral’s activity in the piconet may be reduced. If a Peripheral is in Active mode on an ACL logical transport, it shall listen in every ACL slot to the Central’s traffic, unless that link is being treated as a scatternet link or is absent due to Hold mode. With Sniff mode, the time slots when a Peripheral is listening are reduced, so the Central shall only transmit to a Peripheral in specified time slots. The sniff anchor points are spaced regularly with an interval of Tsniff.
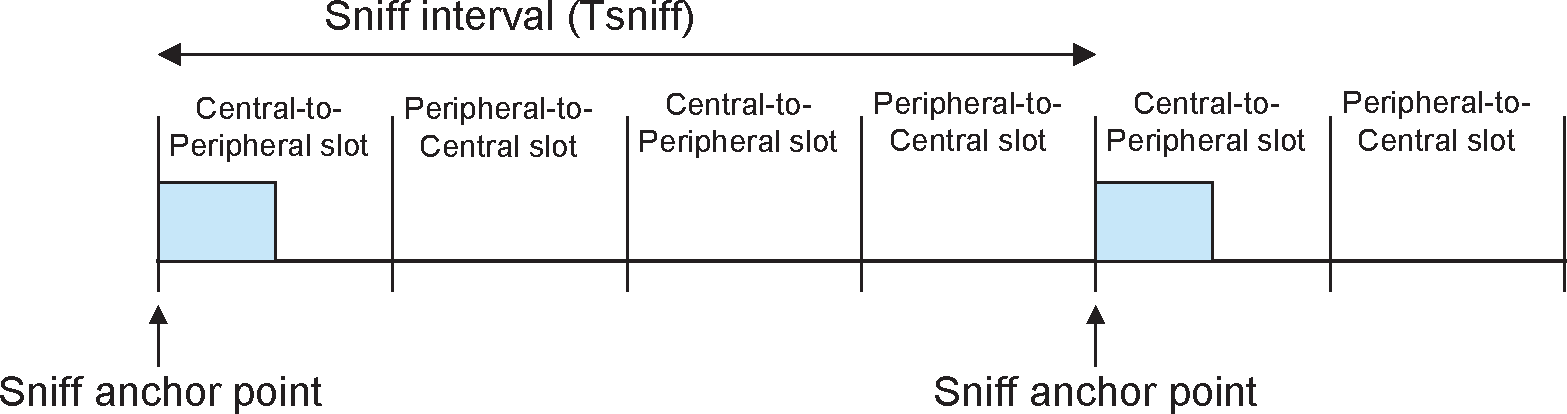
The Peripheral listens in Central-to-Peripheral transmission slots starting at the sniff anchor point. It shall use the following rules to determine whether to continue listening:
If fewer than Nsniff attempt Central-to-Peripheral transmission slots have elapsed since the sniff anchor point then the Peripheral shall continue listening.
If the Peripheral has received a packet with a matching LT_ADDR that contains ACL data (DM, DH, or DV packets) in the preceding Nsniff timeout Central-to-Peripheral transmission slots then it shall continue listening.
If the Peripheral has transmitted a packet containing ACL data (DM, DH, or DV packets) in the preceding Nsniff timeout Peripheral-to-Central transmission slots then it shall continue listening.
If the Peripheral has received any packet with a matching LT_ADDR in the preceding Nsniff timeout Central-to-Peripheral transmission slots then it may continue listening.
A device may override the rules above and stop listening prior to Nsniff timeout or the remaining Nsniff attempt slots if it has activity in another piconet.
It is possible that activity from one sniff timeout may extend to the next sniff anchor point. Any activity from a previous sniff timeout shall not affect activity after the next sniff anchor point. So in the above rules, only the slots since the last sniff anchor point are considered.
Note
Note: Nsniff attempt=1 and Nsniff timeout=0 cause the Peripheral to listen only at the slot beginning at the sniff anchor point, irrespective of packets received from the Central.
N sniff attempt =0 shall not be used.
Sniff mode only applies to asynchronous logical transports and their associated LT_ADDR. Sniff mode shall not apply to synchronous logical transports, therefore, both Centrals and Peripherals shall still respect the reserved slots and retransmission windows of synchronous links.
To enter Sniff mode, the Central or Peripheral shall issue a sniff setup message via the LM protocol. This message includes the sniff interval Tsniff and an offset Dsniff. In addition, an initialization flag indicates whether initialization procedure 1 or 2 shall be used. The device sending the sniff request shall use initialization 1 when the MSB of the Central's current clock (CLK27) is 0; it shall use initialization 2 when the MSB of the Central's current clock (CLK27) is 1. The device that receives the sniff request shall apply the initialization method as indicated by the initialization flag irrespective of its own CLK 27 value. The sniff anchor point determined by the Central and the Peripheral shall be initialized on the slots for which the clock satisfies the applicable equation:
this implies that Dsniff must be even
After initialization, the clock value CLK(k+1) for the next sniff anchor point shall be derived by adding the fixed interval Tsniff to the clock value of the current sniff anchor point:
8.7.1. Sniff Transition mode
Sniff Transition mode is a special mode which is used during the transition between Sniff mode and Active mode. It is required because during this transition it is unclear which mode (Sniff or Active) the Peripheral is in and it is necessary to ensure that the Peripheral is polled correctly regardless of which mode it is in.
In Sniff Transition mode the Central shall maintain the Active mode poll interval in case the Peripheral is in Active mode. In addition the Central shall poll the Peripheral at least once in the sniff attempt transmit slots starting at each sniff anchor point. This transmission counts for the Active mode polling as well. The Central shall use its high power accurate clock when in Sniff Transition mode.
The precise circumstances under which the Central enters Sniff Transition mode are defined in [Vol 2] Part C, Section 4.5.3.1.
8.7.2. Sniff subrating
When sniff subrating is enabled by the Link Manager a device alternates between Sniff mode and Sniff Subrating mode. Sniff Subrating mode allows a device to use a reduced number of sniff anchor points. A device shall transition from Sniff mode to Sniff Subrating mode based on the Sniff mode timeout value (see Section 8.7.2.1). A device shall transition from Sniff Subrating mode to Sniff mode whenever ACL-U, APB-U, ACL-C, or APB-C data is received from the remote device.
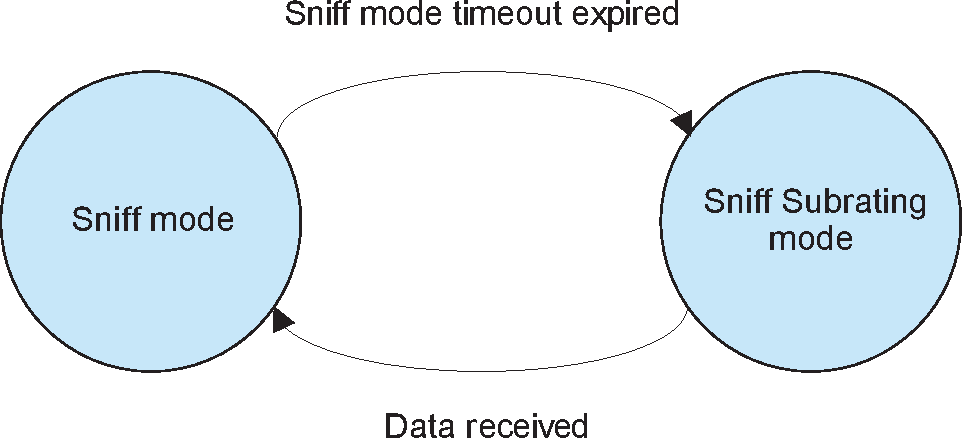
A Peripheral in Sniff Subrating mode shall also temporarily enter Sniff mode after transmitting a packet requiring acknowledgment until the Baseband acknowledgment is received.
Once sniff subrating is enabled the Central and Peripheral may be in Sniff mode or Sniff Subrating mode at different times. The rules defined in Section 8.7.2.2 describe how the two devices maintain synchronization and can reliably exchange data.
8.7.2.1. Sniff mode timeout
The Sniff mode timeout value Tsniff_mode_timeout used by a device shall be at least the greater of the value specified by the peer over LMP and any value specified by the Host.
Whenever a packet containing ACL-U, APB-U, ACL-C, or APB-C data is received by a device in Sniff Subrating mode it shall transition to Sniff mode, re-start the Sniff mode timeout timer, and shall then use all sniff anchor points until at least Tsniff_mode_timeout slots have expired. If ACL-U, APB-U, ACL-C, or APB-C data is received before Tsniff_mode_timeout slots have passed since the last ACL-U, APB-U, ACL-C, or APB-C data was received, the Sniff mode timeout timer shall be restarted. NULL and POLL packets do not contain ACL or APB data and shall not restart the Sniff mode timeout timer.
8.7.2.2. Sniff Subrating mode
When the Sniff mode timeout has expired a device shall enter sniff subrating mode. In Sniff Subrating mode the mandatory sniff subrating anchor points at which the Central shall transmit to the Peripheral and the Peripheral shall listen for the Central, are defined as follows (where M is the max subrate received by the Central, N is the max subrate received by the Peripheral, A is the sniff subrating instant, and k is any positive integer):
Note
Note: denotes the mathematical “floor” function, equivalent to rounding down to the nearest integer. Hence, yields the highest integer j for which Y • .
When sniff subrating is enabled, the rules specified in Section 8.7 for Nsniff attempt and Nsniff Timeout shall apply to sniff subrating anchor points.
Central | Peripheral | |
|---|---|---|
M=N | CLK M ( k ) = A + [ Tsniff • M • k ] | CLK N ( k ) = A + [ Tsniff • N • k ] |
M>N | At least once every j anchor points satisfying CLK N ( k ) = A + [ Tsniff • N • k ], where j = | CLK N ( k ) = A + [ Tsniff • N • k ] |
M<N | CLK M( k ) = A + [ Tsniff • M • k ] | At least once every j anchor points satisfying CLK M( k ) = A + [ Tsniff • M • k ], where j = |
8.8. Hold mode
During the Connection state, the ACL logical transport to a Peripheral can be put in a Hold mode. In Hold mode the Peripheral temporarily shall not support ACL packets on the channel. Any synchronous packet during reserved synchronous slots (from SCO and eSCO links) shall be supported. With the Hold mode, capacity can be made free to do other things like scanning, paging, inquiring, or attending another piconet. The device in Hold mode can also enter a low-power sleep mode. During Hold mode, the Peripheral keeps its logical transport address(es) (LT_ADDR).
Prior to entering Hold mode, Central and Peripheral agree on the time duration the Peripheral remains in Hold mode. A timer shall be initialized with the holdTO value. When the timer is expired, the Peripheral shall wake up, synchronize to the traffic on the channel and will wait for further Central transmissions.
8.9. [This section is no longer used]
8.10. Connectionless Peripheral Broadcast mode
In Connectionless Peripheral Broadcast mode, the Transmitter broadcasts packets to zero or more Receivers.
The Transmitter can broadcast messages to multiple Receivers in Connectionless Peripheral Broadcast mode. For this purpose, the Transmitter (Central) shall reserve an LT_ADDR for use only by Connectionless Peripheral Broadcast traffic. In Connectionless Peripheral Broadcast mode, the Transmitter transmits packets at specified intervals.
8.10.1. Connectionless Peripheral Broadcast transmit operation
In Connectionless Peripheral Broadcast mode, the Transmitter transmits packets on the CPB logical transport at intervals requested by the Host in Central-to-Peripheral transmission slots.
If the Host has not yet provided the BR/EDR Controller with any data packets to transmit since enabling the broadcast, or if the length of the data is zero, the BR/EDR Controller shall transmit NULL packets. This is different than the case where the Host has provided data since enabling the broadcast but has not provided new data since the previous broadcast packet. In that case, the BR/EDR Controller resends the most recent data.
The Host may provide Connectionless Peripheral Broadcast data through HCI commands. Because HCI commands are limited to 255 bytes, a single command cannot carry the maximum payloads allowed by larger packets, such as DH5. Therefore, HCI commands for Connectionless Peripheral Broadcast allow fragmentation of large payloads at the HCI level. The BR/EDR Controller shall assemble all HCI fragments of a packet before transmission and shall not transmit incomplete packets. Until such assembly is complete, the Controller shall continue to transmit the previous data (if any).
Figure 8.25 shows the timing of Connectionless Peripheral Broadcast packets.
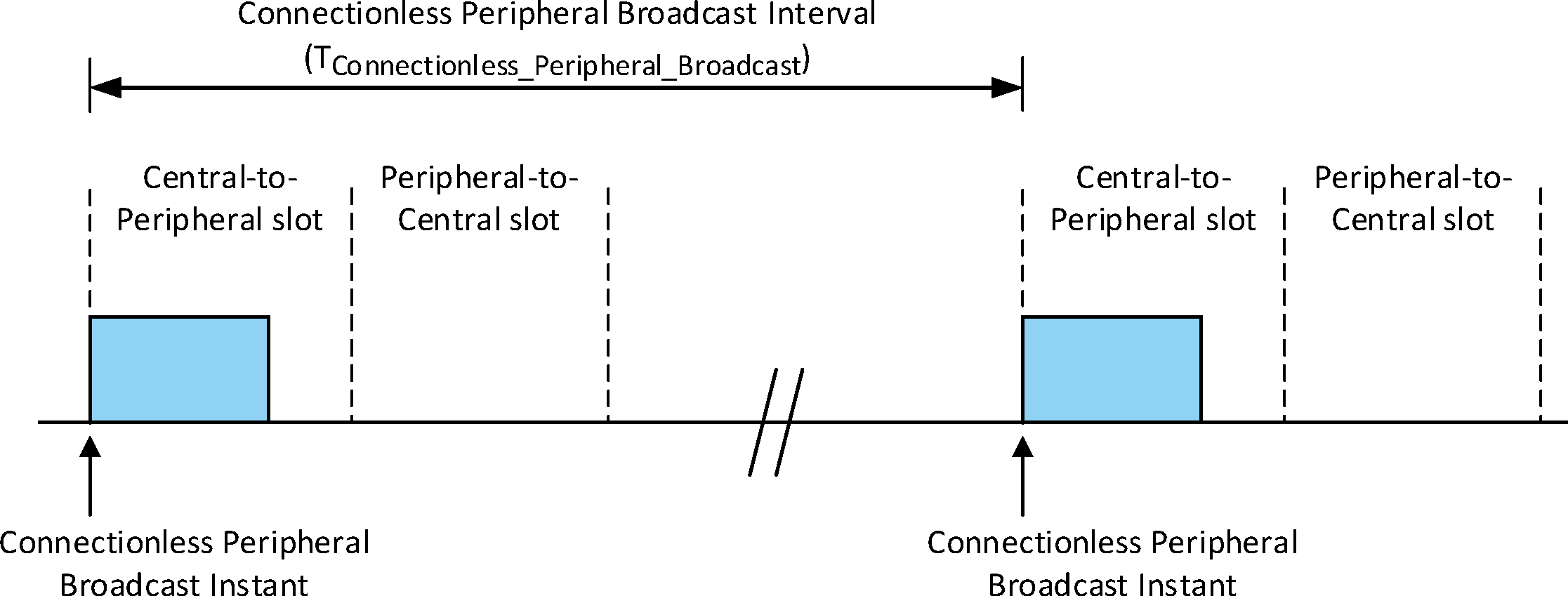
Connectionless Peripheral Broadcast Instants are separated by the Connectionless Peripheral Broadcast Interval (TConnectionless_Peripheral_Broadcast). The Connectionless Peripheral Broadcast interval can be any even value from 0x0002 to 0xFFFE slots and is negotiated between the BR/EDR Controller and the Host during CPB setup. At the start of each Connectionless Peripheral Broadcast Instant, the Connectionless Peripheral Broadcast packet is transmitted using the adapted piconet physical channel. Connectionless Peripheral Broadcast packets shall not be encrypted.
The Transmitter shall stop transmitting Connectionless Peripheral Broadcast packets after CPB_supervisionTO slots have passed without transmission of a Connectionless Peripheral Broadcast packet. CPB_supervisionTO may be any even value from 0x0002 to 0xFFFE slots. Connectionless Peripheral Broadcast packets can fail to transmit for a certain continuous period of time due to scheduling conflicts from higher priority traffic.
8.10.2. Connectionless Peripheral Broadcast receive operation
In Connectionless Peripheral Broadcast mode, the Receiver is synchronized to a Connectionless Peripheral Broadcast Transmitter and is receiving profile broadcast data on the LT_ADDR reserved by the Transmitter for the CPB logical transport.
When requesting synchronization establishment, the Host provides the Controller with the Transmitter’s clock offset and the next Connectionless Peripheral Broadcast Instant received from the synchronization train. Because of delays in the Host, it is possible that the Connectionless Peripheral Broadcast Instant occurs in the past. The BR/EDR Controller shall support Connectionless Peripheral Broadcast instants at least 1 second in the past. The Receiver should determine whether the Connectionless Peripheral Broadcast Instant is in the past or the future by using the Transmitter’s clock offset and its own clock to estimate the Transmitter's current clock and start listening from the next broadcast instant.
The Skip parameter is set by the Host and specifies the number of consecutive Connectionless Peripheral Broadcast instants which the receiver may skip after successfully receiving a Connectionless Peripheral Broadcast packet. If the Connectionless Peripheral Broadcast packet is received successfully, the payload data shall be forwarded to the Host. If no Connectionless Peripheral Broadcast packet is received by a Receiver during a Connectionless Peripheral Broadcast Instant, the Receiver shall ignore Skip and instead listen at every scheduled Connectionless Peripheral Broadcast Instant until it is able to successfully receive a Connectionless Peripheral Broadcast packet or until CPB_supervisionTO number of slots have passed.
The BR/EDR Controller shall stop listening for Connectionless Peripheral Broadcast packets after CPB_supervisionTO slots have passed without receiving a Connectionless Peripheral Broadcast packet.
The BR/EDR Controller may transfer Connectionless Peripheral Broadcast data to the Host through HCI events. Because HCI events are limited to 255 bytes a received packet will not necessarily fit into a single HCI event. The BR/EDR Controller shall fragment and transfer such packets using multiple HCI events.
8.10.3. AFH in Connectionless Peripheral Broadcast
Connectionless Peripheral Broadcast packets shall be transmitted on the adapted piconet channel and the synchronization train shall always contain the current AFH channel map for the PBD logical link.
8.11. Synchronization establishment substates
8.11.1. Synchronization Scan substate
The Synchronization Scan substate is used by Peripherals to receive synchronization train packets from the piconet Central. The Synchronization Scan substate can be entered from the Standby or Connection states. In the Synchronization Scan substate, a device uses the Synchronization Scan procedure (see Section 2.7.3). During each synchronization scan window, the device shall listen on a single frequency with its correlator matched to the Central’s channel access code (CAC).
If the correlator exceeds the trigger threshold during the Synchronization Scan procedure, the scanning device shall receive the synchronization train packet, whose contents are defined in Table 8.11. Upon reception of the synchronization train packet the device shall exit the Synchronization Scan substate and return to the Standby or Connection state as appropriate. If the packet is not received the device should stay in the Synchronization Scan substate. If the synchronization_scanTO expires before reception of a Synchronization Train packet, the device shall return to the Standby state. A device attempting to synchronize to a Connectionless Peripheral Broadcast transport shall ignore any synchronization train packet whose Connectionless Peripheral Broadcast LT_ADDR field in the payload is set to zero.
The synchronization scan may be interrupted by higher priority traffic. In particular, the reserved synchronous slots should have higher priority than the synchronization scan.
8.11.2. Synchronization Train substate
The Synchronization Train substate is used by the Central of the piconet to transmit synchronization train packets. The Synchronization Train substate can be entered from the Standby or Connection states. In the Synchronization Train substate, a device uses the Synchronization Train procedure (see Section 2.7.2). During the Synchronization Train procedure, the Central repeatedly transmits synchronization train packets on the channels specified in Section 2.6.4.8. While in the Synchronization Train substate:
if Connectionless Peripheral Broadcast mode is enabled, the Central shall continue to transmit Connectionless Peripheral Broadcast packets in addition to synchronization train packets;
if the Central is in Coarse Clock Adjustment Recovery Mode, it shall continue transmitting and receiving on all active logical transports to all Peripherals that have acknowledged the Coarse Clock Adjustment (see [Vol 2] Part C, Section 4.1.14.1).
Reserved SCO and eSCO slots should have higher priority than the synchronization train. Once the Central enters the Synchronization Train substate, it shall remain in the Synchronization Train substate until synchronization_trainTO expires or the Host directs otherwise. The Central shall transition to the Standby or Connection state when exiting the Synchronization Train substate.
The synchronization train packet is a basic rate ACL packet with type DM3 and LT_ADDR of zero. FLOW, ARQN and SEQN shall all be set to zero upon transmission and ignored upon receipt. The HEC LFSR shall be initialized with the Central’s UAP. In the payload header, the LLID shall contain the value 0b10 (start of an L2CAP message or no fragmentation). FLOW in the payload header shall be set to zero upon transmission and ignored upon reception. The length of the payload body (LENGTH) shall be 28 bytes. The CRC LFSR shall be initialized with the Central’s UAP. Data whitening is not used. Encryption is not used.
There are two possible formats. Format 1 shall be used when the synchronization train is being transmitted by a device which is the Central of a piconet where Connectionless Peripheral Broadcast mode is enabled, and format 2 shall be used otherwise. The format of the payload portion of the DM3 packet used in the synchronization train is shown in Table 8.11.
Bytes | Field | Length | Format 1 Description | Format 2 Description |
|---|---|---|---|---|
0-3 | CLK | 4 Bytes | Current piconet clock (CLK) | Current piconet clock (CLK) |
4-7 | Future Connectionless Peripheral Broadcast Instant | 4 Bytes | CLK[27:1] corresponding to the start of a future Connectionless Peripheral Broadcast Instant. | CLK[27:1] + 1600 slots |
8-17 | AFH Channel Map | 10 Bytes | The current AFH_Channel_Map used for the PBD logical link. The format is the same as the Link Manager AFH_Channel_Map parameter, see [Vol 2] Part C, Table 5.2. | Unspecified |
18-23 | Central BD_ADDR | 6 Bytes | Central’s BD_ADDR | Central’s BD_ADDR |
24-25 | Connectionless Peripheral Broadcast Interval | 2 Bytes | Time duration in slots from the start of a Connectionless Peripheral Broadcast packet to the start of the next Connectionless Peripheral Broadcast packet. Shall be even. | Unspecified |
26 | Connectionless Peripheral Broadcast LT_ADDR | 1 Byte | The LT_ADDR reserved for the CPB logical transport. | 0x00 |
27 | Service Data | 1 Byte | Defined by the service using the Connectionless Peripheral Broadcast feature. | 0x00 |
The Host provides the Service Data for the synchronization train packet payload body when format 1 is used. The BR/EDR Controller provides the data for all other fields.
All devices in the Synchronization Scan substate shall accept payloads of any length from 28 to 121 bytes and shall ignore bytes 28 (counting from 0) and beyond.
When format 1 is used the Future Connectionless Peripheral Broadcast Instant in the synchronization train packet payload shall correspond to one of the next 4 broadcast instants. Figure 8.26 shows an example of valid and invalid values for this field.
 |
The Central shall not transmit synchronization train packets in a Connectionless Peripheral Broadcast Instant.
9. Audio
On the air-interface, either a 64 kb/s log PCM (Pulse Code Modulation) format (A-law or μ-law) may be used, or a 64 kb/s CVSD (Continuous Variable Slope Delta Modulation) may be used. The latter format applies an adaptive delta modulation algorithm with syllabic companding.
The voice coding on the line interface is designed to have a quality equal to or better than the quality of 64 kb/s log PCM.
Table 9.1 summarizes the voice coding schemes supported on the air interface. The appropriate voice coding scheme is selected after negotiations between the Link Managers.
Voice Codecs | |
|---|---|
linear | CVSD |
8-bit logarithmic | A-law |
μ-law | |
9.1. LOG PCM codec
Since the synchronous logical transports on the air-interface can support a 64 kb/s information stream, a 64 kb/s log PCM traffic can be used for transmission. Either A-law or μ-law compression may be applied. In the event that the line interface uses A-law and the air interface uses μ-law or vice versa, a conversion from A-law to μ-law shall be performed. The compression method shall follow ITU-T recommendations G. 711.
9.2. CVSD codec
A more robust format for voice over the air interface is delta modulation. This modulation scheme follows the waveform where the output bits indicate whether the prediction value is smaller or larger than the input waveform. To reduce slope overload effects, syllabic companding is applied: the step size is adapted according to the average signal slope. The input to the CVSD encoder shall be 64000 samples per second linear PCM (typically 16 bits, but actual value is implementation specific). Block diagrams of the CVSD encoder and CVSD decoder are shown in Figure 9.1, Figure 9.2 and Figure 9.3. The system shall be clocked at 64 kHz.
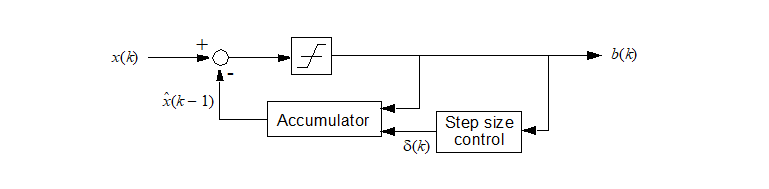

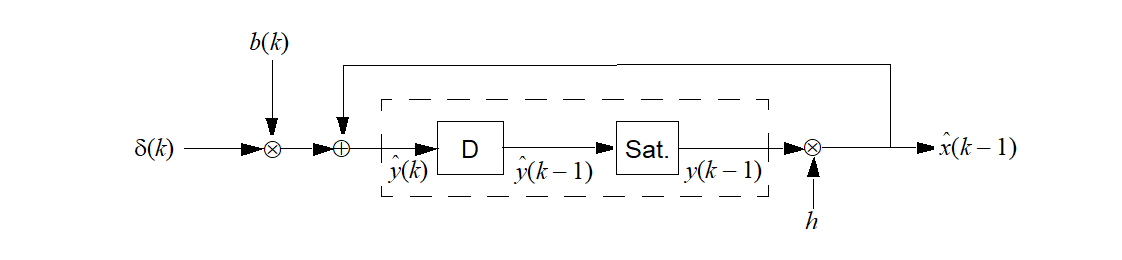
Let for , otherwise . On air these numbers shall be represented by the sign bit; i.e. negative numbers are mapped to “1” and positive and zero numbers are mapped to “0”.
Denote the CVSD encoder output bit b(k), the encoder input x(k), the accumulator contents y(k), and the step size . Furthermore, let h be the decay factor for the accumulator, let β denote the decay factor for the step size, and, let α be the syllabic companding parameter. The latter parameter monitors the slope by considering the K most recent output bits.
Let
Then, the CVSD encoder internal state shall be updated according to the following set of equations:
where
In these equations, δmin and δmax are the minimum and maximum step sizes, and, ymin and ymax are the accumulator’s negative and positive saturation values, respectively. Over air, the bits shall be sent in the same order they are generated by the CVSD encoder.
For a 64 kb/s CVSD, the parameters as shown in Table 9.2 shall be used. The numbers are based on a 16 bit signed number output from the accumulator. These values result in a time constant of 0.5 ms for the accumulator decay, and a time constant of 16 ms for the step size decay
Parameter | Value |
|---|---|
h | |
β | |
J | 4 |
K | 4 |
δmin | 10 |
δmax | 1280 |
ymin | or |
ymax |
9.3. Error handling
In the DV, HV3, EV3, EV5, 2-EV3, 3-EV3, 2-EV5 and 3-EV5 packets, the voice is not protected by FEC. The quality of the voice in an error-prone environment then depends on the robustness of the voice coding scheme and, in the case of eSCO, the retransmission scheme. CVSD, in particular, is rather insensitive to random bit errors, which are experienced as white background noise. However, when a packet is rejected because either the channel access code, the HEC test was unsuccessful, or the CRC has failed, measures have to be taken to “fill” in the lost speech segment.
The voice payload in the HV2 and EV4 packets are protected by a 2/3 rate FEC. For errors that are detected but cannot be corrected, the receiver should try to minimize the audible effects. For instance, from the 15-bit FEC segment with uncorrected errors, the 10-bit information part as found before the FEC decoder should be used. The HV1 packet is protected by a 3 bit repetition FEC. For this code, the decoding scheme will always assume zero or one-bit errors. Thus, there exist no detectable but uncorrectable error events for HV1 packets.
9.4. General audio requirements
9.4.1. Signal levels
For A-law and μ-law log-PCM encoded signals the requirements on signal levels shall follow the ITU-T recommendation G.711.
Full swing at the 16 bit linear PCM interface to the CVSD encoder is defined to be 3 dBm0.
9.4.2. CVSD audio quality
For Bluetooth audio quality the requirements are put on the transmitter side. The 64000 samples per second linear PCM input signal should have negligible spectral power density above 4 kHz. The power spectral density in the 4 kHz to 32 kHz band of the decoded signal at the 64000 samples per second linear PCM output, should be more than 20 dB below the maximum in the 0 kHz to 4 kHz range.
Appendix A. General audio recommendations
A.1. Maximum sound pressure
It is the sole responsibility of each manufacturer to design their audio products in a safe way with regards to injury to the human ear. The Bluetooth Specification doesn’t specify maximum sound pressure from an audio device.
A.2. Other telephony network requirements
It is the sole responsibility of each manufacturer to design the Bluetooth audio product so that it meets the regulatory requirements of all telephony networks that it may be connected to.
A.3. Audio levels for Bluetooth
Audio levels shall be calculated as Send Loudness Rating, SLR, and Receive Loudness Rating, RLR. The calculation methods are specified in ITU-T Recommendation P.79.
The physical test set-up for Handsets and Headsets is described in ITU-T Recommendation P.51 and P.57
The physical test set-up for speakerphones and “Vehicle hands-free systems” is specified in ITU-T Recommendation P.34.
A general equation for computation of loudness rating (LR) for telephone sets is given by ITU-T recommendations P.79 and is given by
where
m is a constant (~ 0.2). wi = weighting coefficient (different for the various LRs). Si = the sensitivity at frequency Fi , of the electro-acoustic path N1,N2, consecutive filter bank numbers (Art. Index: 200 Hz to 4000 Hz)
(EQ 20) is used for calculating the (SLR) according to Figure A.1, and (RLR) according to Figure A.2. When calculating LRs one must only include those parts of the frequency band where an actual signal transmission can occur in order to ensure that the additive property of LRs is retained. Therefore ITU-T P.79 uses only the frequency band 200 Hz to 4000 Hz in LR computations.
A.4. Microphone path
SLR measurement model

A.5. Loudspeaker path
RLR measurement model
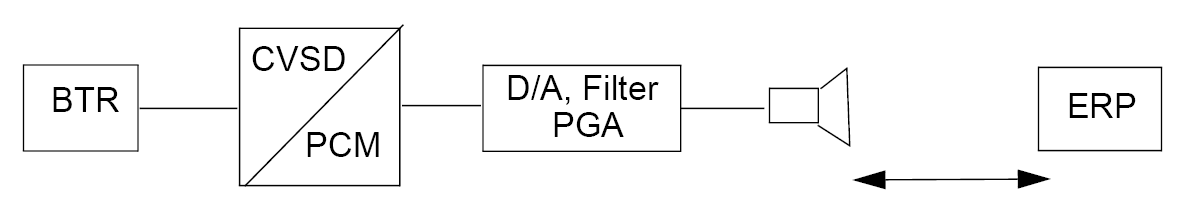
A.6. Bluetooth voice interface
The specification for the Bluetooth voice interface should follow in the first place the ITU-T Recommendations P.79, which specifies the loudness ratings for telephone sets. These recommendations give general guidelines and specific algorithms used for calculating the loudness ratings of the audio signal with respect to Ear Reference Point (ERP).
For Bluetooth voice interface to the different cellular system terminals, loudness and frequency recommendations based on the cellular standards should be used. For example, GSM 03.50 gives recommendation for both the loudness ratings and frequency mask for a GSM terminal interconnection with Bluetooth.
1- The output of the CVSD decoder are 16-bit linear PCM digital samples, at a sampling frequency of 8000 samples per second. Bluetooth also supports 8-bit log PCM samples of A-law and μ-law type. The sound pressure at the ear reference point for a given 16‑bit CVSD sample, should follow the sound pressure level given in the cellular standard specification.
2- A maximum sound pressure which can be represented by a 16-bit linear PCM sample at the output of the CVSD decoder should be specified according to the loudness rating, in ITU P.79 and at PGA value of 0 dB. Programmable Gain Amplifiers (PGAs) are used to control the audio level at the terminals by the user. For conversion between various PCM representations: A-law, μ-law and linear PCM, ITU-T G.711, G.712, G.714 give guidelines and PCM value relationships. Zero-code suppression based on ITU-T G.711 is also recommended to avoid network mismatches.
A.7. Frequency mask
When interfacing a Bluetooth terminal to a digital cellular mobile terminal, the CVSD decoder signal should conform to the frequency mask given in the GSM cellular standard so that the speech coders operate in the intended manner. A recommendation for a frequency mask is given in Table A.1. Figure A.3 shows a plot of the frequency mask for Bluetooth (solid line). The GSM frequency mask (dotted line) is shown in Figure A.3 for comparison.
 |
Frequency (Hz) | Upper Limit (dB) | Lower Limit (dB) |
|---|---|---|
50 | -20 | none |
300 | 4 | -12 |
1000 | 4 | -9 |
2000 | 4 | -9 |
3000 | 4 | -9 |
3400 | 4 | -12 |
4000 | 0 | none |
Appendix B. Timers
This appendix contains a list of Baseband timers related to inactivity timeout defined in the specification. Definitions and default values of the timers are listed below
All timer values are given in slots.
B.1. List of timers
B.1.1. inquiryTO
The inquiryTO defines the number of slots the Inquiry substate shall last. The timer value may be changed by the Host. HCI provides a command to change the timer value.
B.1.2. pageTO
The pageTO defines the number of slots the Page substate can last before a response is received when the extended_pageTO is zero. The timer value may be changed by the Host. HCI provides a command to change the timer value.
B.1.3. extended_pageTO
The extended_pageTO defines the number of additional slots the Page substate can last beyond pageTO before a response is received. The timer value may be changed by the Host. HCI provides a command to change the timer value.
B.1.4. pagerespTO
In the Peripheral, pagerespTO defines the number of slots the Peripheral shall await the Central’s response, FHS packet, after sending the page acknowledgment ID packet. In the Central, pagerespTO defines the number of slots the Central should wait for the FHS packet acknowledgment before returning to Page substate. Both Central and Peripheral units should use the same value for this timeout, to allow common page/scan intervals after reaching pagerespTO.
The pagerespTO value is 8 slots.
B.1.5. newconnectionTO
Every time a new connection is started through paging, scanning, or role switch, the Central sends a POLL packet as the first packet in the new connection. Transmission and acknowledgment of this POLL packet is used to confirm the new connection. If the POLL packet is not received by the Peripheral or the response packet is not received by the Central for newconnectionTO number of slots, both the Central and the Peripheral should return to the previous substate.
newconnectionTO value is 32 slots.
B.1.6. supervisionTO
The supervisionTO is used by both the Central and Peripheral to monitor link loss. If a device does not receive any packets that pass the HEC check and have the proper LT_ADDR for a period of supervisionTO, it should reset the link. The supervision timer keeps running in Hold mode and Sniff mode.
The supervisionTO value may be changed by the Host. HCI provides a command to change the timer value. At the Baseband level a default value equivalent to 20 seconds should be used.
B.1.7. CPB_supervisionTO
The CPB_supervisionTO is used by the Peripheral to monitor connection loss and by the Central to monitor scheduling conflicts and shall be between 0x0002 to 0xFFFE with only even values valid. At the Baseband level a default value equivalent to 5.12 seconds should be used. The Host can change the value of CPB_supervisionTO.
B.1.8. synchronization_trainTO
The synchronization_trainTO is used by the Central to determine how long to continue broadcasting Synchronization Train packets and shall be between 0x00000002 to 0x07FFFFFE with only even values valid. At the Baseband level a default value equivalent to 120 seconds should be used for Connectionless Peripheral Broadcast and a default value equivalent to 20 seconds should be used for Coarse Clock Adjustment Recovery Mode. The Host may change the value of synchronization_trainTO that is used during Connectionless Peripheral Broadcast.
B.1.9. synchronization_scanTO
The synchronization_scanTO is used by the Peripheral to determine when to stop scanning for synchronization train packets. It shall be between 0x0022 to 0xFFFE with only even values valid. At the Baseband level a default value equivalent to 5.12 seconds should be used for Connectionless Peripheral Broadcast and a default value equivalent to 20 seconds should be used during Coarse Clock Adjustment Recovery Mode. The Host may change the value of synchronization_scanTO that is used during Connectionless Peripheral Broadcast.
B.1.10. authenticatedPayloadTO
The authenticatedPayloadTO is the maximum amount of time in seconds allowed between receiving packets containing a MIC. The Host can change the value of authenticatedPayloadTO.
The default value for authenticatedPayloadTO is 30 seconds.
B.1.11. CLK_adj_dragTO
The CLK_adj_dragTO is the minimum amount of time in seconds the drag shall be suspended when a Peripheral has not responded after the Central has dragged the clock.
The CLK_adj_dragTO value shall be 1 second.
Appendix C. Recommendations for AFH operation in Hold, Sniff, and Connectionless Peripheral Broadcast modes
The three possible AFH operation modes for an AFH capable Peripheral in Hold mode and Sniff mode are the same three AFH operation modes used during Connection state:
Enabled (using an AHS with some RF channels unused)
Enabled (using AHS(79))
Disabled
The Central may place an AFH capable Peripheral in any of the three AFH operating modes.
C.1. Operation at the Central
A Central that has one or more Peripherals in Hold mode or Sniff mode and decides to update them simultaneously shall schedule an AFH_Instant for a time that allows it to update all these Peripherals (as well as its active Peripherals) with the new adaptation.
A Central that has multiple Peripherals with non-overlapping “wake” times (e.g. Peripherals in Sniff mode with different timing parameters) may keep them enabled on the same adaptation provided that its scheduling of the AFH_Instant allows enough time to update them all.
This timing is summarized in Figure C.1. In this example the Central decides that a hop sequence adaptation applying to all its Peripherals at the same time is required. However it cannot schedule an AFH_Instant until it has informed its active Peripheral, its Peripheral in Hold mode, and its Peripheral in Sniff mode.
If it decides that only some Peripherals require the new adaptation, it need only take those Peripherals into account when scheduling the AFH_Instant.
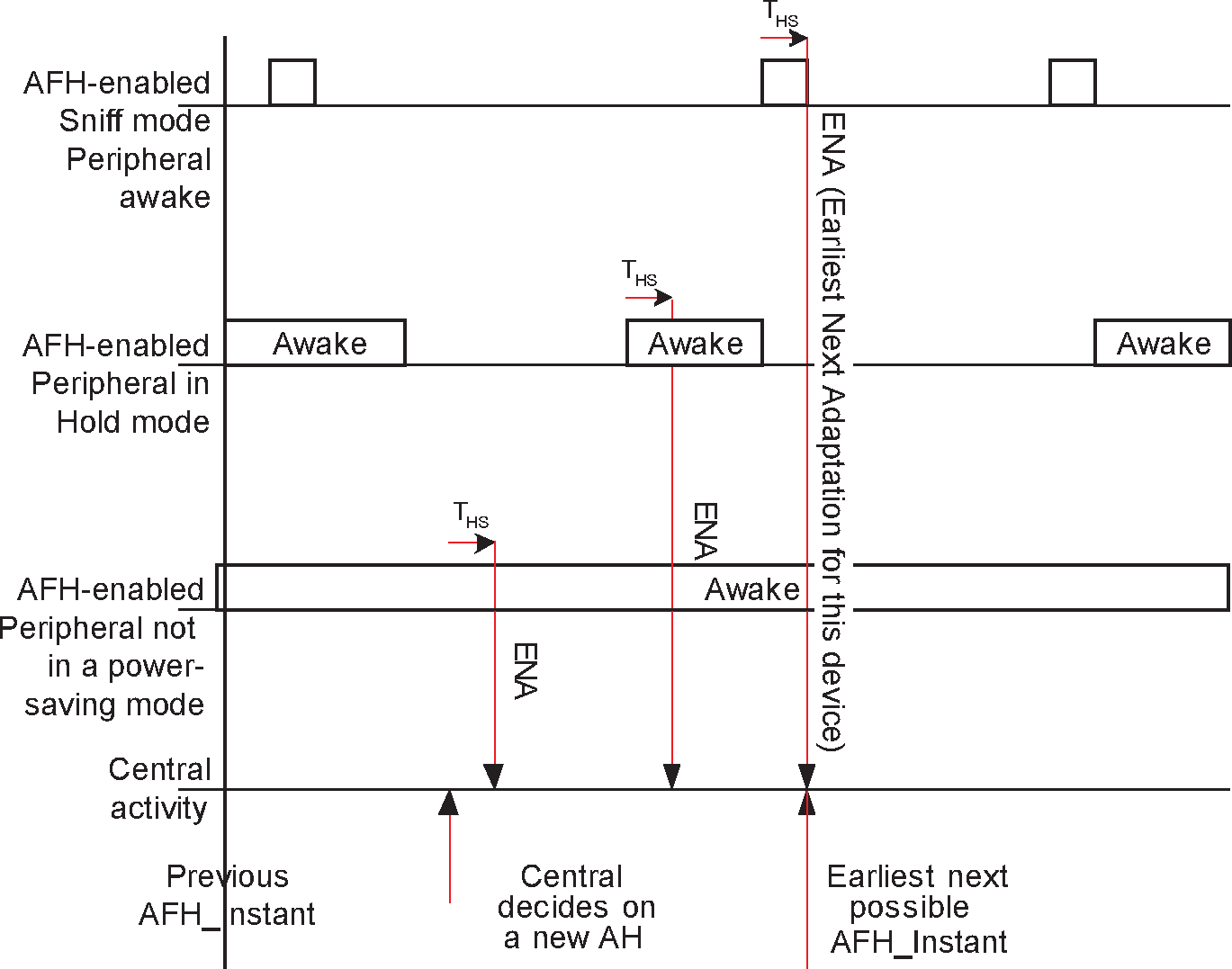
C.2. [This section is no longer used]
C.3. AFH operation in Sniff mode
Once a Peripheral has been placed in Sniff mode, the Central may periodically change its AHS without taking the Peripheral out of Sniff mode.
C.4. AFH operation in Hold mode
A Peripheral that is in Hold mode cannot send or receive any LMP messages. Once the Peripheral has left Hold mode the Central may subsequently update the Peripheral’s adaptation.
C.5. AFH operation in Connectionless Peripheral Broadcast
After the Transmitter’s BR/EDR Controller notifies the Transmitter’s Host that the AFH channel map has changed for the PBD logical link, the Transmitter’s Host may restart the synchronization train to allow Receivers to obtain the updated AFH channel map. This is shown in Figure C.2.

Modification of the AFH channel map will affect Receivers using a different AFH channel map. Depending on the overlap between a Receiver’s current AFH channel map and the current AFH channel map of the Transmitter (Central), the Receiver may miss some Connectionless Peripheral Broadcast instants and, in the case of disjoint or nearly disjoint AFH channel maps, the Receiver may lose synchronization. Receivers should monitor the Connectionless Peripheral Broadcast reception rate and obtain the current AFH channel map of the Transmitter (via the synchronization train) if degradation exceeds desired thresholds.