Bluetooth® LE legacy pairing passkey entry, we had an overview about LE legacy pairing with passkey. Other than LE legacy pairing, LE secure connections is the other option for pairing. LE secure connections is an enhanced security feature introduced in Bluetooth® Core 4.2. It uses a federal information processing standards (FIPS) compliant algorithm called elliptic curve Diffie Hellman (ECDH) for key generation. For LE secure connections, it support four association models:
- Just works
- Numeric comparison (only for LE secure connections)
- Passkey entry
- Out of band (OOB)
Numeric comparison only exists for LE secure connections, not for legacy pairing. So it is a newer association model, and today we will have an inside look at it.
Phase 1 – pairing feature exchange
I had talked about the pairing feature exchange in Bluetooth pairing feature exchange, but I want to review it here. Table 1 is the pairing request/response packet definition. In the AuthReq field, there is one bit named SC. If LE secure connections pairing is supported by the device, then the SC field shall be set to 1. Otherwise, it shall be set to 0. If both devices support LE secure connections pairing, then LE secure connections pairing shall be used. Otherwise, LE legacy pairing shall be used.
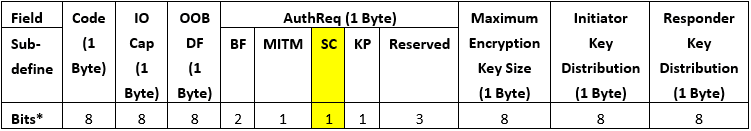
*Bit order is LSB to MSB.
So if two devices want to pair by LE secure connections, they must set the SC to 1 to indicate to the peer device that I have the capability for secure connections.
Phase 2 – key Generation method selection
After pairing feature exchange, the initiator and responder should determine what key generation method will be used. Below is sample C syntax coding for the key generation method.
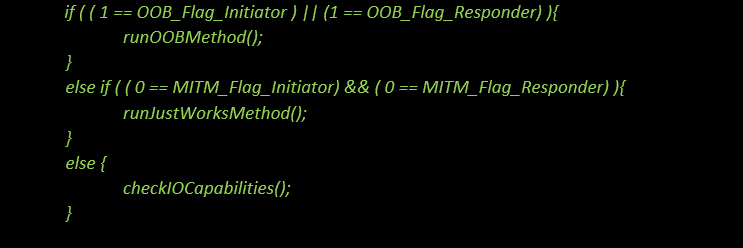
Table 2 lists the IO capabilities of initiating and responding devices for numeric comparison. When both the initiating and the responding devices have display and yes/no I/O capabilities or display and keyboard I/O capabilities, the numeric comparison association model is used.
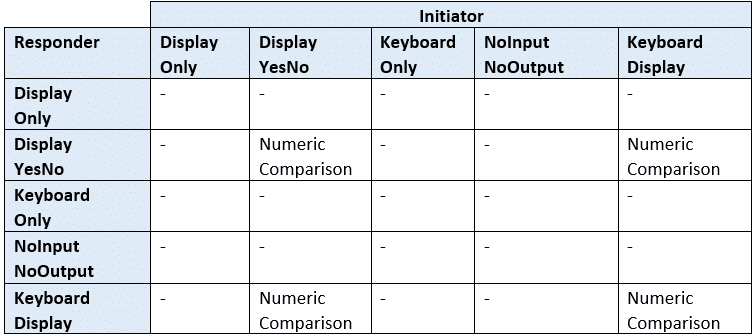
* – Means it is for other key generation methods, other than numeric comparison.
Phase 2 – authentication
After key generation, pairing will go to phase 2, authentication. The aim is for protection against man-in-the-middle (MITM) attacks and generation of the keys which will be used to encrypt the connection link.
In public key exchange, each device generates its own elliptic curve Diffie-Hellman (ECDH) public-private key pair. The public-private key pair contains a private key and public key.
- SKa, private key of initiating device
- PKa, public key of initiating device
- SKb, private key of responding device
- PKb, public key of responding device
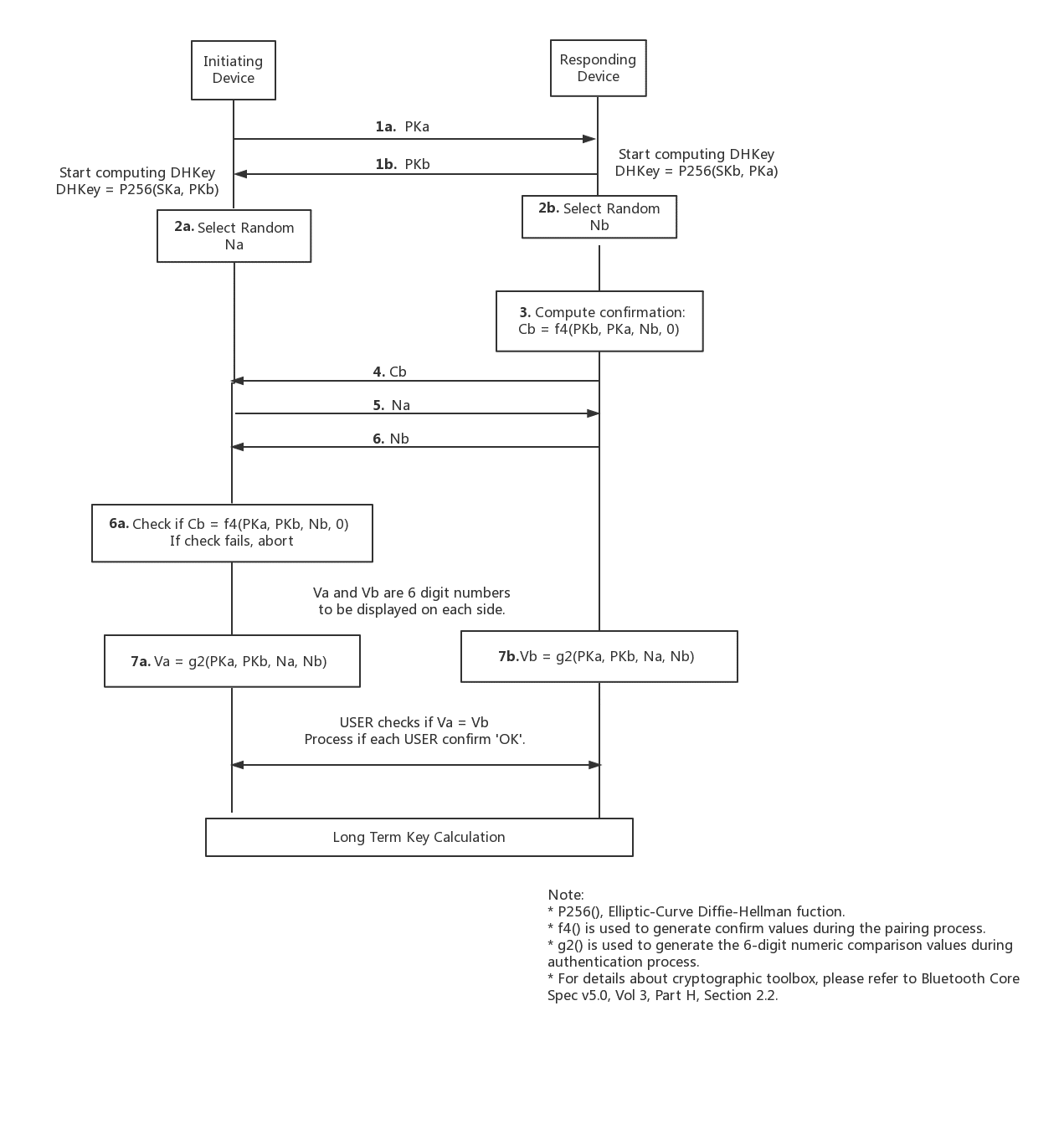
Pairing is started by the initiating device sending its PKa to responding device. The responding device replies with its own PKb. After the public keys have been exchanged, the device can then start computing the Diffie-Hellman key; you can see it starts at the end of 1b in figure 1.
After that, each device selects a random 128-bit nonce. This value is used to prevent replay attacks.
- Na, 128-bit random nonce of initiating device
- Nb, 128-bit random nonce of responding device
Following this the responding device then computes a commitment, Cb, which is calculated using Nb, PKa, PKb, and 0. It’s shown in step 3, figure 1.
Step 4, the responding device MUST share Cb before it receives the initiating device’s Na.
Step 5, the initiating device MUST share its Na before it receives the responding device’s Nb.
Step 6, the initiating device MUST check Cb which is from responding device after it receives the responding device’s Nb.
At this point, initiating or responding device already knows the peer device’s public key and random nonce. The initiating device can confirm commitment (Cb) from the responding device. A failure at this point indicates the presence of an attacker or other transmission error and should cause pairing process to abort, step 6.a.
Assuming the commitment check succeeds, the two devices each compute six-digit confirmation values that are displayed to the user on their respective devices. The user is expected to check that these six-digit values match and to confirm if there is a match. If no match, pairing aborts.
Phase 3 – long-term key (LTK)
When authentication is successful, the two devices start to compute the LTK which will be used for link encryption. This is the final piece of the puzzle for pairing and reconnection; within different association models, authenticate the peer device and prevent MITM attacks. Since the LTK calculation is common for any LE secure connections association model.
Conclusion
According to the user experience and convenience, compared with Bluetooth LE legacy pairing passkey entry, numeric comparison just need to two buttons, YES and NO, to indicate whether six-digit confirmation values match or not between these two devices, it does not need a digit-keyboard for passkey input, from 0-9, so this is an improvement to simplify the I/O capability for hardware. Meanwhile, due to numeric comparison only existing for LE secure connections, it provides enhanced protection against threats like eavesdropping and MITM. So guys, if you start to develop a product which is sensitive of privacy and needs high protection for Bluetooth LE link, This is a good choice for you.